SSH public key + MACs
How can I copy a SSH public key to another computer.
This is between two MAC computers.
I cannot SSH from my Macbook air, when is 'ssh' it advises: Permission Denied (pubickey)
All the links I looked at look too complicated, can someone advise me of an easier way.
Thanks
This is between two MAC computers.
I cannot SSH from my Macbook air, when is 'ssh' it advises: Permission Denied (pubickey)
All the links I looked at look too complicated, can someone advise me of an easier way.
Thanks
You will have to use password authentication to copy the files over to the other machine.
Do you have physical access to both the computers? If yes, you can use a USB disk for example, if no, then you either need to have "password authentication" enabled in your ssh file on the other computer and use "username/password" combination to access it ...
The approach will be different on what your possibilities are ...
In any case, to add the public key so you can use it you should do the following in your Terminal:
Create the ssh folder if it doesn't exist
The approach will be different on what your possibilities are ...
In any case, to add the public key so you can use it you should do the following in your Terminal:
Create the ssh folder if it doesn't exist
you@machine:~$ mkdir ~/.sshyou@machine:~$ chmod 700 ~/.sshyou@machine:~$ cat ~/id_rsa.pub >> ~/.ssh/authorized_keysyou@machine:~$ chmod 600 ~/.ssh/authorized_keysyou@machine:~$ rm ~/id_rsa.pub
Have you looked at this link?
http://coolestguidesontheplanet.com/make-passwordless-ssh-connection-osx-10-9-mavericks-linux/
What ssh command have you tried? What have you tried so far?
Can you connect to the remote system without a public key, using a password? If you can, you can basically run the following from one system and copy the remote key to the others.
You'll have to enter your password 3 times.
There's no need to remove your public key from your local system. The public key is meant to be given out. You can generate it from your private key. Make sure you back up your private key to a secure location and only keep it on servers you use to connect to others. I only keep it on my local system and on a backup disk.
http://coolestguidesontheplanet.com/make-passwordless-ssh-connection-osx-10-9-mavericks-linux/
What ssh command have you tried? What have you tried so far?
Can you connect to the remote system without a public key, using a password? If you can, you can basically run the following from one system and copy the remote key to the others.
You'll have to enter your password 3 times.
ssh Remote_Account@Remote_Mac 'mkdir .ssh'
scp ~/.ssh/id_rsa.pub Remote_Account@Remote_Mac:~/.ssh/My_Key
ssh Remote_Account@Remote_Mac 'cat ~.ssh/My_key >> ~/.ssh/authorized keys: rm ~/.ssh/My_Key'ssh Remote_Account@Remote_Mac 'mkdir .ssh'
scp ~/.ssh/id_rsa.pub Remote_Account@Remote_Mac:~/.ssh/authorized keys'There's no need to remove your public key from your local system. The public key is meant to be given out. You can generate it from your private key. Make sure you back up your private key to a secure location and only keep it on servers you use to connect to others. I only keep it on my local system and on a backup disk.
ASKER
I just want to be able to SSH from my other MAC machine.
So I want to take the key from my office MAC and put it on my home MAC so I can SSH to a server. I will use a flash drive to do this.
Keep in mind I am a complete newbie to FreeBSD and line command stuff.
Thanks
So I want to take the key from my office MAC and put it on my home MAC so I can SSH to a server. I will use a flash drive to do this.
Keep in mind I am a complete newbie to FreeBSD and line command stuff.
Thanks
ASKER
I got the keys how do I install them on my other MAC, I do not see a .ssh folder and how do you create a hidden folder
You need to create the folder first. It's not there by default.
mkdir .ssh
If you're using the other mac as "duplicate" system to ssh to another server and you want to use the same keys, then you should copy your private key(by default it's id_rsa) to it.
mkdir .ssh
If you're using the other mac as "duplicate" system to ssh to another server and you want to use the same keys, then you should copy your private key(by default it's id_rsa) to it.
ASKER
I got the two files and now where do I put these files on my personal computer at home? You say make a .ssh folder but where?
Also I have the SSH key.
Thanks
Also I have the SSH key.
Thanks
Make it in your home folder and copy the files to your it.
mkdir ~/.ssh
cp /Volumes/USB_DEVICE/{id_rs
mkdir ~/.ssh
cp /Volumes/USB_DEVICE/{id_rs
The guidelines I gave above really describe what you need to do...
If you want to do everything via the filer you'll need to unhide the hidden files ... But still, you'll need to set the correct rights on the key-files because else you'll get an error when trying to use them.
To unhide the the hidden files, copy the line below into your terminal and press enter:
To hide them again use the line below:
If you want to do everything via the filer you'll need to unhide the hidden files ... But still, you'll need to set the correct rights on the key-files because else you'll get an error when trying to use them.
To unhide the the hidden files, copy the line below into your terminal and press enter:
defaults write com.apple.finder AppleShowAllFiles -boolean true ; killall FinderTo hide them again use the line below:
defaults write com.apple.finder AppleShowAllFiles -boolean false ; killall Finder
It's not necessary to "unhide" them in the finder. They're visible on the command line. ssh is already done via the terminal.
To view the files:
ls -a
will show them.
open .hidden_name
will open the "hidden" file or folder from the command line.
To view the files:
ls -a
will show them.
open .hidden_name
will open the "hidden" file or folder from the command line.
@serialband I did not say it was necessary to unhide them, as you can see in my first post, just giving the poster all the options seeing he/she isn't comfortable using the command line...
If you're going to use ssh, you should get used to the command line.
ASKER
I copied the files over to the hide share ./ssh on my home computer, and I get 'Permission Denied' when I try to ssh into another machine.
I put the two files in /users/<username/.ssh folder
Is there another way?
I put the two files in /users/<username/.ssh folder
Is there another way?
How are you connecting? What tool or command line are you using?
Eg:
If you are using above command and still can't connect, try it again with -vvvv at the end, like so:
This will produce a detailed log of what is happening, just post that log here so we can see what is happening.
Eg:
ssh root@<ip-address-server> -i ~/.ssh/idrsa If you are using above command and still can't connect, try it again with -vvvv at the end, like so:
ssh root@<ip-address-server> -i ~/.ssh/idrsa -vvvvThis will produce a detailed log of what is happening, just post that log here so we can see what is happening.
Have you set your permissions correctly? The private key must be restricted to the users only.
chmod 600 ~/.ssh/id_rsa
chmod 600 ~/.ssh/id_rsa
ASKER
still says:
Permission Denied (publickey)
Am I logged in under root?
Permission Denied (publickey)
Am I logged in under root?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
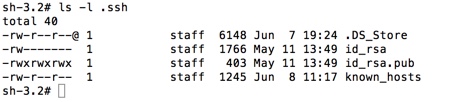
when I log on under 'su'
I get
sh-3.2# chmod 600 ~/.ssh/id_rsa
chmod: /var/root/.ssh/id_rsa: No such file or directory
I get
sh-3.2# chmod 600 ~/.ssh/id_rsa
chmod: /var/root/.ssh/id_rsa: No such file or directory
ASKER
debug2: key: /Users/zero/.ssh/id_rsa (0x7fc0b3c11cb0),
debug2: key: /Users/zero/.ssh/id_dsa (0x0),
debug1: Authentications that can continue: publickey
debug3: start over, passed a different list publickey
debug3: preferred publickey,keyboard-interac
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,passw
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Offering RSA public key: /Users/zero/.ssh/id_rsa
debug3: send_pubkey_test
debug2: we sent a publickey packet, wait for reply
debug1: Authentications that can continue: publickey
debug1: Trying private key: /Users/zero/.ssh/id_dsa
debug3: no such identity: /Users/zero/.ssh/id_dsa: No such file or directory
debug2: we did not send a packet, disable method
debug1: No more authentication methods to try.
Permission denied (publickey).
I also get this.
debug2: key: /Users/zero/.ssh/id_dsa (0x0),
debug1: Authentications that can continue: publickey
debug3: start over, passed a different list publickey
debug3: preferred publickey,keyboard-interac
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,passw
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Offering RSA public key: /Users/zero/.ssh/id_rsa
debug3: send_pubkey_test
debug2: we sent a publickey packet, wait for reply
debug1: Authentications that can continue: publickey
debug1: Trying private key: /Users/zero/.ssh/id_dsa
debug3: no such identity: /Users/zero/.ssh/id_dsa: No such file or directory
debug2: we did not send a packet, disable method
debug1: No more authentication methods to try.
Permission denied (publickey).
I also get this.
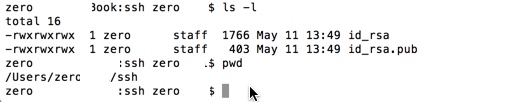
Ok, this tells us the keys should be under your user folder, not the root folder.
so you should put the keys under /Users/zero/.ssh/
Then do the same regarding the permissions and try to logon again.
so you should put the keys under /Users/zero/.ssh/
Then do the same regarding the permissions and try to logon again.
ASKER
try by changing owner and group like this (in the .ssh folder):
chown zero:zero id_rsa
and
chown zero:zero id_rsa.pub
in terminal you should always be able to see the hidden folders by doing "ls -la".
chown zero:zero id_rsa
and
chown zero:zero id_rsa.pub
in terminal you should always be able to see the hidden folders by doing "ls -la".
ASKER
Get: Invalid file mode: zero:zero
hmmm ... It's a Mac, I'm barking up the wrong tree, the staff group is normal, so that's not the problem.
Did you remove the dot (.) from the ssh folder? If your ssh folder doesn't have the dot you shouldn't use it in the command to connect.
So, what is the command you use?
Did you remove the dot (.) from the ssh folder? If your ssh folder doesn't have the dot you shouldn't use it in the command to connect.
So, what is the command you use?
Have you put your public key into the ~/.ssh/authorized_keys file?
cat ~/.ssh/id_rsa >> ~/.ssh/authorized_keys
A Mac is basically BSD. The permission should be that of the owner or user of the account.
chown -R Acount_Name:staff ~/.ssh
to fix the permissions.
cat ~/.ssh/id_rsa >> ~/.ssh/authorized_keys
A Mac is basically BSD. The permission should be that of the owner or user of the account.
chown -R Acount_Name:staff ~/.ssh
to fix the permissions.
ASKER
I do not have a file called: authorized_keys?
Where is that located?
I did this:chown -R Acount_Name:staff ~/.ssh
I still get: Permission denied(publickey)
Where is that located?
I did this:chown -R Acount_Name:staff ~/.ssh
I still get: Permission denied(publickey)
The authorized_keys file is on the server/client you're trying to connect to, in the same folder (.ssh). This file should also have permissions set to 600.
Can you post the log again when you're trying to connect (-vvvv)...
You place the contents of you public key into authorized_keys, either by manually editing it with a cut and paste, or just running the command I had in my previous response.
This command append the contents of your id_rsa into your authorized_keys file, creating it if it doesn't exist.
cat ~/.ssh/id_rsa >> ~/.ssh/authorized_keys
The authorized_keys file allows users with the correct matching private key to connect. If it's empty or nonexistent, then no keys are allowed to connect.
This command append the contents of your id_rsa into your authorized_keys file, creating it if it doesn't exist.
cat ~/.ssh/id_rsa >> ~/.ssh/authorized_keys
The authorized_keys file allows users with the correct matching private key to connect. If it's empty or nonexistent, then no keys are allowed to connect.
ASKER
There is no ./ssh/authorized_keys folder.
Does it have to be created?
Does it have to be created?
Yes it does.
mkdir ~/.ssh
Then run the other commands from my previous comment. Be sure to note that the folder name is preceded by a dot(.) to be a "hidden" folder. ( .ssh )
mkdir ~/.ssh
Then run the other commands from my previous comment. Be sure to note that the folder name is preceded by a dot(.) to be a "hidden" folder. ( .ssh )