Kinan Al-Haffar
asked on
Remote Desktop Services Collection Creation Issue
Hi Guys;
I've set up an RDS environment consisting of 5 servers "Session Host, Gateway, Webaccess, License Server, & connection broker"
The Webaccess and the GW servers are in the DMZ, all the required ports are open on the FW, and Windows firewall is disabled on the all servers "service is on though". All servers are on 2012 R2, SQL 2012 Express is installed on the Licensing server. Everything went smooth till the Collection Creation phase, where I'm getting the following:
1. Warning: CorpRDSHP11 "Session host server" The property UserAuthenticationRequired
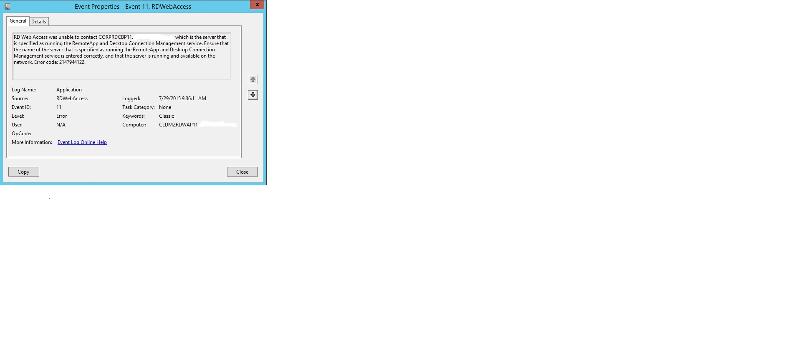
2. When I access the WebAccess through the link "https://webaccess.domain.com/RDWeb/", I don't see anything under Current Folder!
Please help.
Thanks.
I've set up an RDS environment consisting of 5 servers "Session Host, Gateway, Webaccess, License Server, & connection broker"
The Webaccess and the GW servers are in the DMZ, all the required ports are open on the FW, and Windows firewall is disabled on the all servers "service is on though". All servers are on 2012 R2, SQL 2012 Express is installed on the Licensing server. Everything went smooth till the Collection Creation phase, where I'm getting the following:
1. Warning: CorpRDSHP11 "Session host server" The property UserAuthenticationRequired
2. When I access the WebAccess through the link "https://webaccess.domain.com/RDWeb/", I don't see anything under Current Folder!
Please help.
Thanks.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Hi Solacement;
The check box for showing the collection in WA is checked by default. I checked it, and it is ticked. I un-ticked it, and re-ticked it again and applied the changes, but nothing changed.
Thanks.
The check box for showing the collection in WA is checked by default. I checked it, and it is ticked. I un-ticked it, and re-ticked it again and applied the changes, but nothing changed.
Thanks.
ASKER
Hi Cliff Galiher;
Thank you for your help, I'm sorry for posting 2 questions, but I thought that since both questions are related then it might be better to post them together, but I agree with you.
As for your suggestion, I will check and let you know in a shot while.
Thanks.
Thank you for your help, I'm sorry for posting 2 questions, but I thought that since both questions are related then it might be better to post them together, but I agree with you.
As for your suggestion, I will check and let you know in a shot while.
Thanks.
ASKER
Hi Cliff Galiher;
#1 has been solved as suggested, it was the local GPO. However; #2 is still an issue :-(
#1 has been solved as suggested, it was the local GPO. However; #2 is still an issue :-(
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
I am not surprised that #2 is still an issue. Ultimately I didn't suspect the issues were related, which is why I thought combining them in the same question would actually be detrimental. But we'll tackle it.
ASKER
Hi Cliff Galiher;
Thank you for your continuous help, below are the FW rules on the ASA which include all the open ports:
DMZ Servers:
1. CLDMZRDGP11 “10.64.31.62” Remote Desktop Gateway Server – VIP 192.168.71.125
2. CLDMZRDWAP11 “10.64.31.60” Remote Desktop Web Access Server – VIP 192.168.71.124
Internal Servers:
1. CORPRDLSP11 “10.64.10.60” Remote Desktop Licensing Server
2. CORPRDSHP11 “10.64.4.227” Remote Desktop Session Host Server – VIP 10.64.14.139
3. CORPRDCBP11 “10.64.4.225” Remote Desktop Connection Broker Server – VIP 10.64.14.140
Ports have been configured according to the following KB:
http://social.technet.microsoft.com/wiki/contents/articles/16164.which-ports-are-used-by-a-rds-2012-deployment.aspx
Thank you for your continuous help, below are the FW rules on the ASA which include all the open ports:
DMZ Servers:
1. CLDMZRDGP11 “10.64.31.62” Remote Desktop Gateway Server – VIP 192.168.71.125
2. CLDMZRDWAP11 “10.64.31.60” Remote Desktop Web Access Server – VIP 192.168.71.124
Internal Servers:
1. CORPRDLSP11 “10.64.10.60” Remote Desktop Licensing Server
2. CORPRDSHP11 “10.64.4.227” Remote Desktop Session Host Server – VIP 10.64.14.139
3. CORPRDCBP11 “10.64.4.225” Remote Desktop Connection Broker Server – VIP 10.64.14.140
US-C-PRI-ASA-FW# show access-list outside-acl
access-list outside-acl; 1175 elements; name hash: 0xb1b82131
access-list outside-acl line 1 remark ***Access for Windows Remote Desktop Services (RDS)***
access-list outside-acl line 2 extended permit tcp any object-group RDS-Ext object-group RDS-Ext-TCP 0xe91026ea
access-list outside-acl line 2 extended permit tcp any host 192.168.71.124 eq https (hitcnt=0) 0x06306c37
access-list outside-acl line 2 extended permit tcp any host 192.168.71.124 eq 3389 (hitcnt=0) 0xaccefcea
access-list outside-acl line 2 extended permit tcp any host 192.168.71.124 eq 3391 (hitcnt=0) 0x3c4ef7ba
access-list outside-acl line 3 extended permit udp any object-group RDS-Ext object-group RDS-Ext-UDP 0xda08c491
access-list outside-acl line 3 extended permit udp any host 192.168.71.124 eq 3389 (hitcnt=0) 0xabbb45ab
access-list outside-acl line 3 extended permit udp any host 192.168.71.124 eq 3391 (hitcnt=0) 0x48a99fb0
access-list Web-DMZ-acl line 1 remark ***Access for Windows Remote Desktop Services (RDS)***
access-list Web-DMZ-acl line 2 extended permit tcp object-group RDS-DMZ object-group RDS-Int object-group RDS-DMZ-TCP 0x51a7e0eb
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.139 eq 445 (hitcnt=0) 0x7b7cab59
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.139 eq 3389 (hitcnt=0) 0x83568535
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.139 eq 5504 (hitcnt=0) 0x2609d746
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.139 eq 5985 (hitcnt=0) 0xea64f8fd
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.140 eq 445 (hitcnt=0) 0x46bb88f0
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.140 eq 3389 (hitcnt=0) 0xf0f8e2ea
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.140 eq 5504 (hitcnt=0) 0x78f08609
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.124 host 10.64.14.140 eq 5985 (hitcnt=0) 0x38376943
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.139 eq 445 (hitcnt=0) 0x88b1e830
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.139 eq 3389 (hitcnt=0) 0x83de87d5
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.139 eq 5504 (hitcnt=0) 0x2dac1a6f
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.139 eq 5985 (hitcnt=0) 0x0dd1d0de
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.140 eq 445 (hitcnt=0) 0xb1e4513a
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.140 eq 3389 (hitcnt=0) 0x1136490b
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.140 eq 5504 (hitcnt=0) 0x4fac369a
access-list Web-DMZ-acl line 2 extended permit tcp host 192.168.71.125 host 10.64.14.140 eq 5985 (hitcnt=0) 0xec586c73Ports have been configured according to the following KB:
http://social.technet.microsoft.com/wiki/contents/articles/16164.which-ports-are-used-by-a-rds-2012-deployment.aspx
ASKER
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Re point 2 - I'm sure when I last did this I had to tick a checkbox within the collection properties to show it in RDWeb. By default nothing is published there