Old SSL Cert Still Being Presented In Outlook - Exchange 2010
Hi EE peeps!
After creating a new SSL cert in Exchange, users are still getting the old, expired cert in their Outlook client. I have checked IIS bindings and made sure the new cert is in https. I have reset IIS and also had a user restart their computer. The old cert has been deleted from EMC. Yes, I've run the "get-exchangecertificate | fl" cmdlet and the old cert is not there, just the new one.
Any thoughts on how to fix this?
After creating a new SSL cert in Exchange, users are still getting the old, expired cert in their Outlook client. I have checked IIS bindings and made sure the new cert is in https. I have reset IIS and also had a user restart their computer. The old cert has been deleted from EMC. Yes, I've run the "get-exchangecertificate | fl" cmdlet and the old cert is not there, just the new one.
Any thoughts on how to fix this?
The areas I would look next are within Exchange management console. You created the new cert, but did you bind the services to actually use it? Usually the old one is still there and binded, you have to move services to the new cert and then optionally remove the old one too.
The Microsoft KB article for that is: https://technet.microsoft.com/en-us/library/dd351257(v=exchg.141).aspx
Other than that, do you have any proxies or load balancers in front of Exchange that may have the old certificate still in use?
The Microsoft KB article for that is: https://technet.microsoft.com/en-us/library/dd351257(v=exchg.141).aspx
Other than that, do you have any proxies or load balancers in front of Exchange that may have the old certificate still in use?
ASKER
@Will
Yes, the cert is enabled.
Yes, I've recreated an Outlook profile for a user. Didn't work.
@whoajack
Yes, the services are bound to the new cert.
Yes, the old cert has been deleted.
No proxies or load balancers.
Yes, the cert is enabled.
Yes, I've recreated an Outlook profile for a user. Didn't work.
@whoajack
Yes, the services are bound to the new cert.
Yes, the old cert has been deleted.
No proxies or load balancers.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
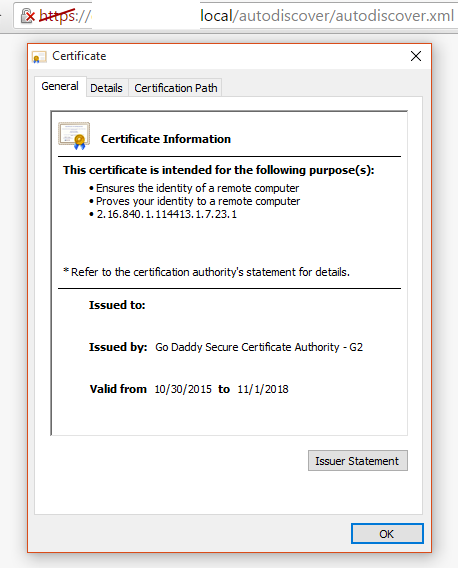
This might clear some things up.
I am using:
-Internal CA to sign exchange.domain.local
-External CA to sign autodiscover.domain.com and mail.domain.com
The external (GoDaddy) CA has been given the IIS and SMTP bindings in the EMC.
@whoajack
I have reset IIS already and everyone still gets the old cert
No load balancers or proxies (deja vu?)
One Exchange server
@Will
Yes, this happens for all users.
No cert error on OWA. The new cert shows with 2018 expiration.
I am using:
-Internal CA to sign exchange.domain.local
-External CA to sign autodiscover.domain.com and mail.domain.com
The external (GoDaddy) CA has been given the IIS and SMTP bindings in the EMC.
@whoajack
I have reset IIS already and everyone still gets the old cert
No load balancers or proxies (deja vu?)
One Exchange server
@Will
Yes, this happens for all users.
No cert error on OWA. The new cert shows with 2018 expiration.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
@whoajack
IIS, EMC and EMS do not show the old cert. It is gone. Only the new cert is showing.
IIS, EMC and EMS do not show the old cert. It is gone. Only the new cert is showing.
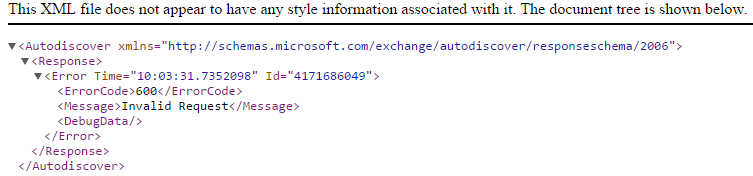
Pretty weird. Doing some online searches, finding hits about this SCP for Exchange that is used before DNS is even used in some configurations. Let's check your settings. Do the following...
Get-ClientAccessServer | fl *
Look for this AutoDiscoverInternalUri property and see what it's pointing to. Just thinking out loud, not sure if will help but can't hurt.
Get-ClientAccessServer | fl *
Look for this AutoDiscoverInternalUri property and see what it's pointing to. Just thinking out loud, not sure if will help but can't hurt.
ASKER
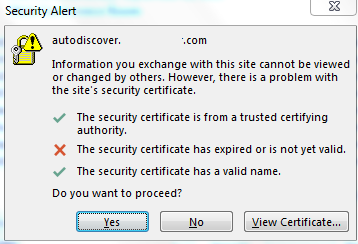
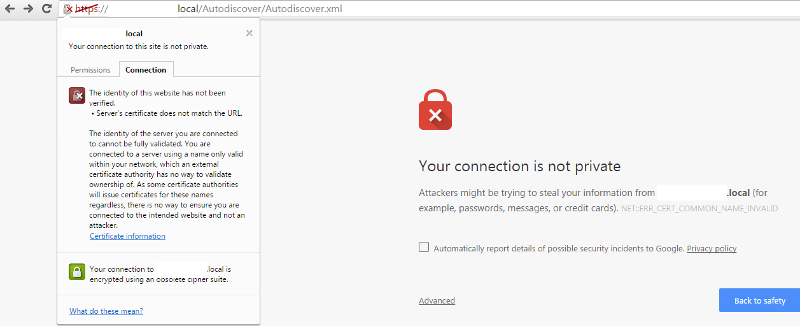
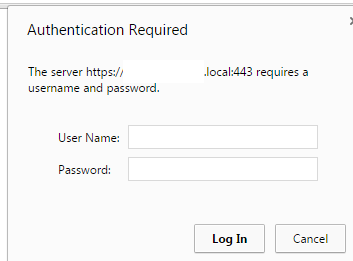
When you go to that URL from your computer (and from one of the computers that pose the problem) do you get a valid page or file loading or a warning?
That's good progress. So the browser test is also failing and has a certificate warning. If it's the new cert, am wondering why it is not seen as valid. We'd have to look some more cert details to ensure the valid from/to dates, the subject name, the subject alternate name / SAN entries are valid.
You are getting the "does not match the URL" error. Compare your old cert to the new one and see what might be different.
You are getting the "does not match the URL" error. Compare your old cert to the new one and see what might be different.
ASKER
OK, it appears to be fixed!
I restarted the Default Web Site in IIS and did an IISreset for the 10th time, and this time it worked... no idea why it took so many resets, though.
The URL mismatch is because CAB forum doesn't allow private domains to be secured by 3rd party CAs any more. I will have to change all of my internal addresses for owa, autodiscover, etc. to the external address... but that's an entirely different matter.
Thanks for your help in troubleshooting.
I restarted the Default Web Site in IIS and did an IISreset for the 10th time, and this time it worked... no idea why it took so many resets, though.
The URL mismatch is because CAB forum doesn't allow private domains to be secured by 3rd party CAs any more. I will have to change all of my internal addresses for owa, autodiscover, etc. to the external address... but that's an entirely different matter.
Thanks for your help in troubleshooting.
Awesome Paul, glad you got your issue resolved. I was thinking that could be quite frustrating to deal with. Have a good one!
ASKER
It was tough to pick which answers were the solution since performing several IISresets is what finally made the new cert show up... something that was not suggested.... but your inquiries led me to the solution and I appreciate it. Thanks!
Also have you tried to re-create the Outlook profile for a user that is encountering this issue?
Will.