Windows - Common repository for digital certificates?
Here's how I think it works. Tell me if I'm wrong.
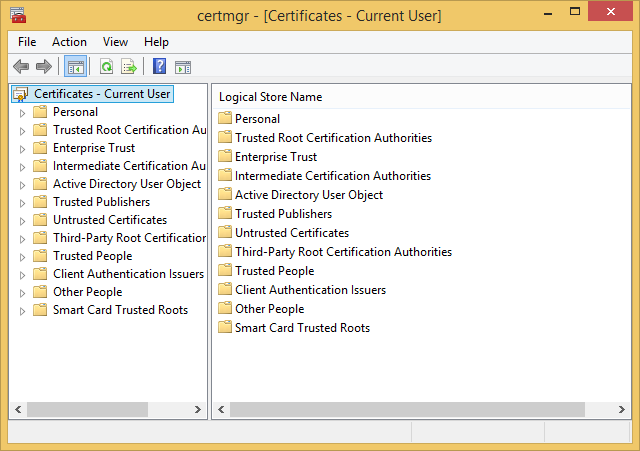
Is this accurate? All my digital certificates, whether they're obtained through Chrome, Firefox, IE, or another third-party tool, eventually end up in the common repository, Windows Cert Manager?
I go to amazon.com for the first time and buy some swim goggles. Amazon's site directs my browser to the certificate authority (CA), my browser pulls the Amazon certificate, and stores it in Windows Cert Manger.
I navigate to a client's site for the first time via Citrix. At some point during the process I again retrieve a certificate from a CA, and store it in the Windows Cert Manager.
Any time my Windows machine is involved in a SSL/TLS handshake, I'll eventually pull a certificate and store it in the Windows Cert Manager.
Is this accurate? All my digital certificates, whether they're obtained through Chrome, Firefox, IE, or another third-party tool, eventually end up in the common repository, Windows Cert Manager?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER