Skype for Business 2015 inplace upgrade from Lync 2013 Certificate Binding Issue
Hi,
I have been having a problem in my Skype for Business 2015 server that I get a lot of Events as follows:
Event 4097: 1e9fd4a0: ignore error 0x80092013:certificate revocation list offline
Event 4097: 1e9fd4a0: cert chain trust status is in error: 0x1000040
This has been driving me mad for ages and this seems to affect a lot of people.
Can anyone running S4B that was not an inplace upgrade from Lync 2013 check if the values for "Verify Revocation Using Cached Client Certificate Only", "Usage Check" & "Negotiate Client Certificate" as the same as below:
(I am particularly interested in the values in 0.0.0.0:444 & [::]:444)
C:\>netsh http show sslcert
SSL Certificate bindings:
-------------------------
IP:port : 0.0.0.0:443
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {4dc3e181-e14b-4a21-b022-5
Certificate Store Name : My
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Disabled
Usage Check : Enabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Disabled
IP:port : 0.0.0.0:444
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {00000000-0000-0000-0000-0
Certificate Store Name : (null)
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Enabled
Usage Check : Disabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Enabled
IP:port : 0.0.0.0:4443
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {4dc3e181-e14b-4a21-b022-5
Certificate Store Name : My
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Disabled
Usage Check : Enabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Disabled
IP:port : [::]:444
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {00000000-0000-0000-0000-0
Certificate Store Name : (null)
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Enabled
Usage Check : Disabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Enabled
Thanks
Jack
I have been having a problem in my Skype for Business 2015 server that I get a lot of Events as follows:
Event 4097: 1e9fd4a0: ignore error 0x80092013:certificate revocation list offline
Event 4097: 1e9fd4a0: cert chain trust status is in error: 0x1000040
This has been driving me mad for ages and this seems to affect a lot of people.
Can anyone running S4B that was not an inplace upgrade from Lync 2013 check if the values for "Verify Revocation Using Cached Client Certificate Only", "Usage Check" & "Negotiate Client Certificate" as the same as below:
(I am particularly interested in the values in 0.0.0.0:444 & [::]:444)
C:\>netsh http show sslcert
SSL Certificate bindings:
-------------------------
IP:port : 0.0.0.0:443
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {4dc3e181-e14b-4a21-b022-5
Certificate Store Name : My
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Disabled
Usage Check : Enabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Disabled
IP:port : 0.0.0.0:444
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {00000000-0000-0000-0000-0
Certificate Store Name : (null)
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Enabled
Usage Check : Disabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Enabled
IP:port : 0.0.0.0:4443
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {4dc3e181-e14b-4a21-b022-5
Certificate Store Name : My
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Disabled
Usage Check : Enabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Disabled
IP:port : [::]:444
Certificate Hash : xxxxxxxxxxxxxxxxxxxxxxxxxx
Application ID : {00000000-0000-0000-0000-0
Certificate Store Name : (null)
Verify Client Certificate Revocation : Enabled
Verify Revocation Using Cached Client Certificate Only : Enabled
Usage Check : Disabled
Revocation Freshness Time : 0
URL Retrieval Timeout : 0
Ctl Identifier : (null)
Ctl Store Name : (null)
DS Mapper Usage : Disabled
Negotiate Client Certificate : Enabled
Thanks
Jack
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
I don't know if this is going to be helpful or not, but I presume you have your own PKI infrastructure, which you have used to issue your certificates to your Front End servers. The default Certifiate Authority CRL is to have file and ldap. By default, I change this and remove file and ldap and use http instead, because file and ldap require authentication to obtain the CRL, whereas http does not (I have a fairly large environment spanning 30 Active directory forests, not all of which are trusted, so I need to ensure certificates work everywhere).
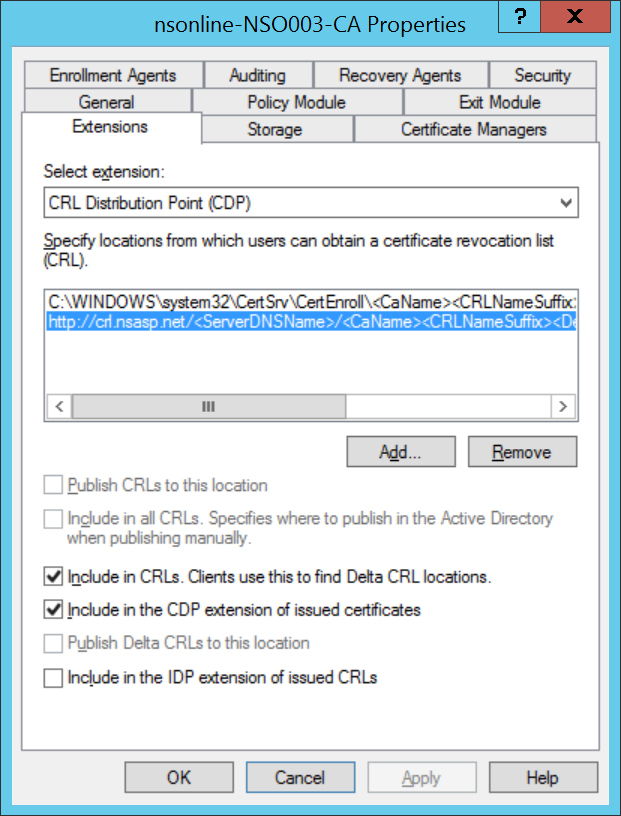
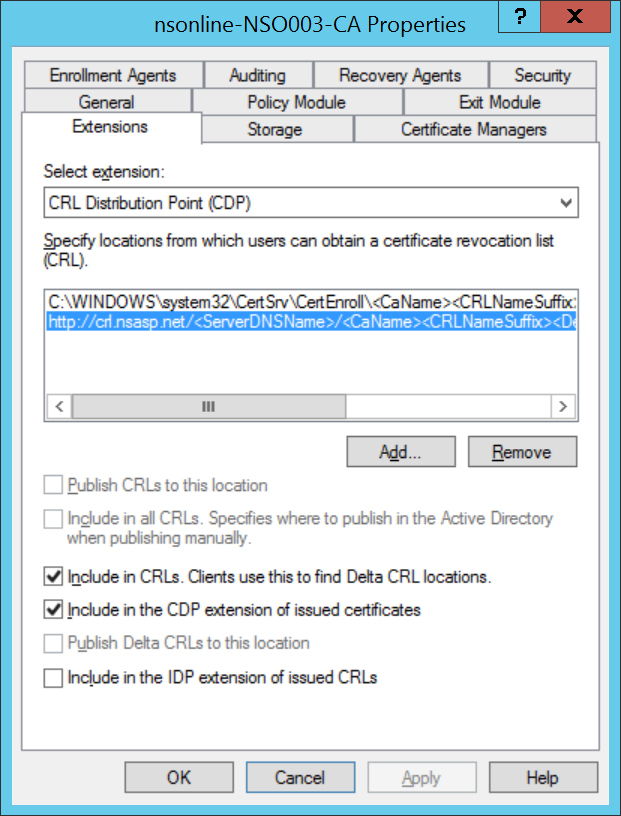
This is what my Certificate Authority configuration looks like for the CDP portion:
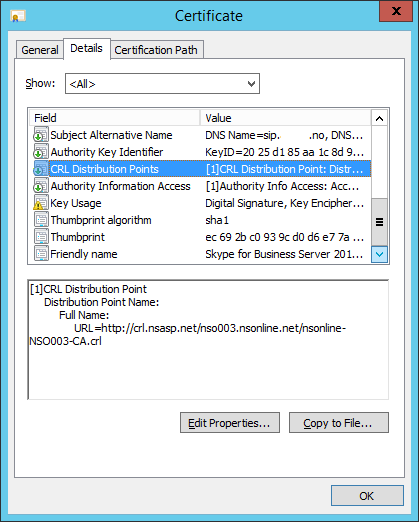
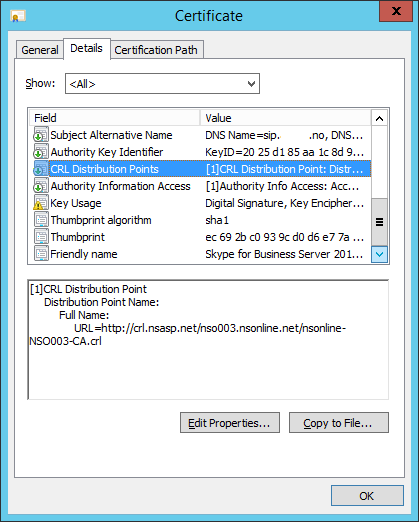
and this is what the CRL of the Skype for Business certificate looks like:
You could try to do something similar - but please make sure that the URL you use is valid and gets updated frequently. You can use http to test the URL. I have a schedule task that copies the CA and CRL to the relevant place for me.
This is what my Certificate Authority configuration looks like for the CDP portion:
and this is what the CRL of the Skype for Business certificate looks like:
You could try to do something similar - but please make sure that the URL you use is valid and gets updated frequently. You can use http to test the URL. I have a schedule task that copies the CA and CRL to the relevant place for me.
ASKER