Extract link for file from web page
Dear Experts
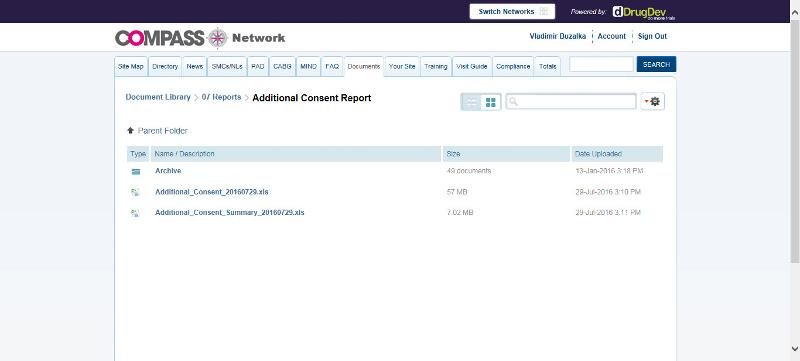
I am new to this topic, I have web page listing files, see picture 1, when you click on file, it will start download. However when you rightclick on file and clik SaveTargetAs, you will not save final file, but HTML page.
Can you advice me what is link for given file?
Web page code is showed on picture 1.
Many thanks for advice
V
 COMPASS-Network_-Document-Library.html
COMPASS-Network_-Document-Library.html
I am new to this topic, I have web page listing files, see picture 1, when you click on file, it will start download. However when you rightclick on file and clik SaveTargetAs, you will not save final file, but HTML page.
Can you advice me what is link for given file?
Web page code is showed on picture 1.
Many thanks for advice
V
 COMPASS-Network_-Document-Library.html
COMPASS-Network_-Document-Library.html
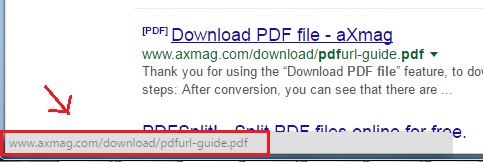
Can you hover your mouse on the file. The link to the file should be displayed at the status bar of the browser.
ASKER
Unfortunatelly status bar shows nothing when I hover mouse over file
Any advice?
Any advice?
You have to FULLY understand the WHOLE CONVERSATION TRAFFIC before you even start attempting to code something in Java.
You are running into this problem because this website is shielded from the normal user. The download HAS TO BE CHECKED that the correct user has access to it. That's why there's a page behind it which serves you the real file after checking your login information.
To fully code it in Java (or any other programs), you have to code the login sequence first, then the correct cookie storage. After that find out what the content is of the links, and finally from the reply of the server (after you request each link seperately), you can finally extract the link for the file (yes, you have to do it one by one).
If you made the Java tag by accident (meaning, you really only want this one link, and you don't intend to start programming), just download the file. In the Downloads tab of your program, the correct direct download link is displayed. However, this link may not work at all for someone else, since it's a protected environment. The direct download link only works for you for only that session. Tomorrow, it will fail (or if you log out).
You are running into this problem because this website is shielded from the normal user. The download HAS TO BE CHECKED that the correct user has access to it. That's why there's a page behind it which serves you the real file after checking your login information.
To fully code it in Java (or any other programs), you have to code the login sequence first, then the correct cookie storage. After that find out what the content is of the links, and finally from the reply of the server (after you request each link seperately), you can finally extract the link for the file (yes, you have to do it one by one).
If you made the Java tag by accident (meaning, you really only want this one link, and you don't intend to start programming), just download the file. In the Downloads tab of your program, the correct direct download link is displayed. However, this link may not work at all for someone else, since it's a protected environment. The direct download link only works for you for only that session. Tomorrow, it will fail (or if you log out).
ASKER
Dear Kimputer
many thanks, my primary aim is to automatically download that single file every day, I do not need to program anything, I mentioned JAVA probably incorrectly, I had a feeling that environment itself was programmed in JAVA? I do not know.
I need simply to automate process of download of that single XLS file you can see on picture. I use software Winadutomation or Automate, I know how to log in automatically, I can switch to correct "folder", but I cannot parse link to file, this is what confused me a lot.
Thanks
V
many thanks, my primary aim is to automatically download that single file every day, I do not need to program anything, I mentioned JAVA probably incorrectly, I had a feeling that environment itself was programmed in JAVA? I do not know.
I need simply to automate process of download of that single XLS file you can see on picture. I use software Winadutomation or Automate, I know how to log in automatically, I can switch to correct "folder", but I cannot parse link to file, this is what confused me a lot.
Thanks
V
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks