intcomser
asked on
Cisco ASA 5505 with Cisco VPN Client Software - Ping only works one way
Hello all -
Just replaced an older 5505 with a new unit running 9.2. Configured entirely using ASDM and it is very simple config. For some reason when users connect via the Cisco VPN Client software they are unable to ping hosts on the internal network, however I can ping the VPN clients from within the internal network with no issues. I know this has got to be an ACL issue but I can't find it. Config is below. Thanks very much in advance!
!
hostname vhcafirewall
names
ip local pool VPN-Pool 10.10.10.2-10.10.10.19 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.100.254 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address x.x.x.x 255.255.255.0
!
ftp mode passive
dns server-group DefaultDNS
domain-name vhca.org
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network NETWORK_OBJ_10.10.10.0_27
subnet 10.10.10.0 255.255.255.224
object network NETWORK_OBJ_192.168.100.0_
subnet 192.168.100.0 255.255.255.0
access-list remote-users_splitTunnelAc
access-list inbound extended permit icmp any any
access-list outside_cryptomap_65535.65
pager lines 24
logging enable
logging asdm informational
mtu inside 1500
mtu outside 1500
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (inside,outside) source static NETWORK_OBJ_192.168.100.0_
!
object network obj_any
nat (inside,outside) dynamic interface
!
nat (inside,outside) after-auto source dynamic any interface
access-group inbound in interface outside
route outside 0.0.0.0 0.0.0.0 1.1.1.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-reco
user-identity default-domain LOCAL
http server enable
http 192.168.100.0 255.255.255.0 inside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec ikev1 transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-MD5 esp-des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-SHA esp-aes esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-MD5 esp-aes esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-SHA esp-des esp-sha-hmac
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev1 transform-set ESP-A
ES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-A
ES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto ca trustpool policy
crypto ikev1 enable outside
crypto ikev1 policy 10
authentication crack
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 20
authentication rsa-sig
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 30
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 40
authentication crack
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 50
authentication rsa-sig
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 60
authentication pre-share
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 70
authentication crack
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 80
authentication rsa-sig
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 90
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 100
authentication crack
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 110
authentication rsa-sig
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 120
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 130
authentication crack
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 140
authentication rsa-sig
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 150
authentication pre-share
encryption des
hash sha
group 2
lifetime 86400
telnet 192.168.100.0 255.255.255.0 inside
telnet timeout 5
no ssh stricthostkeycheck
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
group-policy remote-users internal
group-policy remote-users attributes
wins-server value 192.168.100.3
dns-server value 192.168.100.3
vpn-tunnel-protocol ikev1
password-storage disable
split-tunnel-policy tunnelspecified
split-tunnel-network-list value remote-users_splitTunnelAc
default-domain value vhca.org
username vhcavpn
username vhcavpn attributes
vpn-group-policy remote-users
tunnel-group remote-users type remote-access
tunnel-group remote-users general-attributes
address-pool VPN-Pool
default-group-policy remote-users
tunnel-group remote-users ipsec-attributes
ikev1 pre-shared-key *****
!
!
Just replaced an older 5505 with a new unit running 9.2. Configured entirely using ASDM and it is very simple config. For some reason when users connect via the Cisco VPN Client software they are unable to ping hosts on the internal network, however I can ping the VPN clients from within the internal network with no issues. I know this has got to be an ACL issue but I can't find it. Config is below. Thanks very much in advance!
!
hostname vhcafirewall
names
ip local pool VPN-Pool 10.10.10.2-10.10.10.19 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.100.254 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address x.x.x.x 255.255.255.0
!
ftp mode passive
dns server-group DefaultDNS
domain-name vhca.org
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network NETWORK_OBJ_10.10.10.0_27
subnet 10.10.10.0 255.255.255.224
object network NETWORK_OBJ_192.168.100.0_
subnet 192.168.100.0 255.255.255.0
access-list remote-users_splitTunnelAc
access-list inbound extended permit icmp any any
access-list outside_cryptomap_65535.65
pager lines 24
logging enable
logging asdm informational
mtu inside 1500
mtu outside 1500
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (inside,outside) source static NETWORK_OBJ_192.168.100.0_
!
object network obj_any
nat (inside,outside) dynamic interface
!
nat (inside,outside) after-auto source dynamic any interface
access-group inbound in interface outside
route outside 0.0.0.0 0.0.0.0 1.1.1.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-reco
user-identity default-domain LOCAL
http server enable
http 192.168.100.0 255.255.255.0 inside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec ikev1 transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-MD5 esp-des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-SHA esp-aes esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-MD5 esp-aes esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-SHA esp-des esp-sha-hmac
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev1 transform-set ESP-A
ES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-A
ES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto ca trustpool policy
crypto ikev1 enable outside
crypto ikev1 policy 10
authentication crack
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 20
authentication rsa-sig
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 30
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 86400
crypto ikev1 policy 40
authentication crack
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 50
authentication rsa-sig
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 60
authentication pre-share
encryption aes-192
hash sha
group 2
lifetime 86400
crypto ikev1 policy 70
authentication crack
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 80
authentication rsa-sig
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 90
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 100
authentication crack
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 110
authentication rsa-sig
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 120
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 130
authentication crack
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 140
authentication rsa-sig
encryption des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 150
authentication pre-share
encryption des
hash sha
group 2
lifetime 86400
telnet 192.168.100.0 255.255.255.0 inside
telnet timeout 5
no ssh stricthostkeycheck
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
group-policy remote-users internal
group-policy remote-users attributes
wins-server value 192.168.100.3
dns-server value 192.168.100.3
vpn-tunnel-protocol ikev1
password-storage disable
split-tunnel-policy tunnelspecified
split-tunnel-network-list value remote-users_splitTunnelAc
default-domain value vhca.org
username vhcavpn
username vhcavpn attributes
vpn-group-policy remote-users
tunnel-group remote-users type remote-access
tunnel-group remote-users general-attributes
address-pool VPN-Pool
default-group-policy remote-users
tunnel-group remote-users ipsec-attributes
ikev1 pre-shared-key *****
!
!
^^^ If you do that, normal internet traffic will stop getting NATTED?
access-list no_nat0_outbound extended permit ip any 192.168.100.0 255.255.255.0 10.10.10.0 255.255.255.0
would make more sense
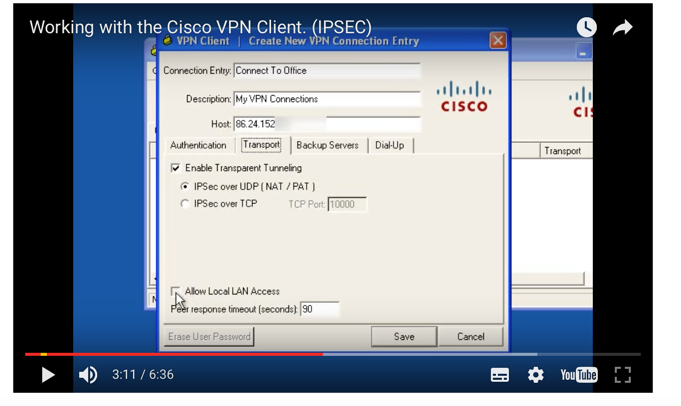
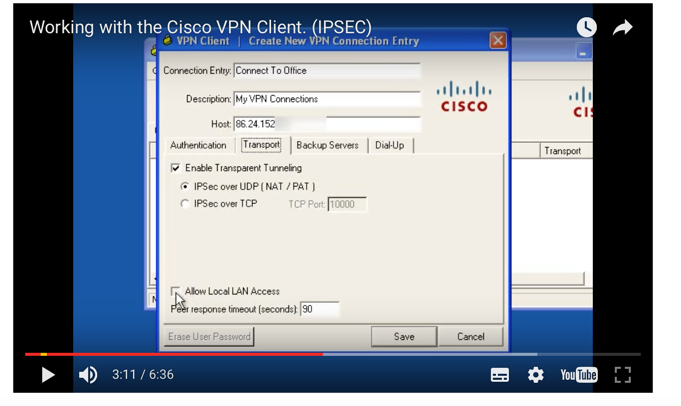
also make sure the clients have LAN access enabled, (and if they are Windows clients their Windows firewall is disabled, or allows ICMP_
access-list no_nat0_outbound extended permit ip any 192.168.100.0 255.255.255.0 10.10.10.0 255.255.255.0
would make more sense
also make sure the clients have LAN access enabled, (and if they are Windows clients their Windows firewall is disabled, or allows ICMP_
ASKER
Unfortunately neither of these solutions worked. Adding the access-list and assigning them did not change the symptom; hosts on the internal network could ping the VPN clients but not vice versa. The Allow Local LAN Access box was already checked and these clients were able to ping internal hosts via the VPN before the ASA was replaced. I've run this config against other working configs and I don't see any differences.
Any other ideas?
Any other ideas?
nat (inside,outside) source static NETWORK_OBJ_192.168.100.0_
ASKER
Thank you but I believe that line is already in the config:
nat (inside,outside) source static NETWORK_OBJ_192.168.100.0_
Unless I need to remove the no-proxy-arp route-lookup qualifiers?
nat (inside,outside) source static NETWORK_OBJ_192.168.100.0_
Unless I need to remove the no-proxy-arp route-lookup qualifiers?
Haven't noticed it was already in due to the line brakes.
Why do you have
object network obj_any
subnet 0.0.0.0 0.0.0.0
nat (inside,outside) dynamic interface
and
nat (inside,outside) after-auto source dynamic any interface
I think the problem is with the NAT order. Try to remove NAT statement from object network obj_any as you already have NAT rule for the internet traffic - nat (inside,outside) after-auto source dynamic any interface.
Why do you have
object network obj_any
subnet 0.0.0.0 0.0.0.0
nat (inside,outside) dynamic interface
and
nat (inside,outside) after-auto source dynamic any interface
I think the problem is with the NAT order. Try to remove NAT statement from object network obj_any as you already have NAT rule for the internet traffic - nat (inside,outside) after-auto source dynamic any interface.
ASKER
Okay I removed the extra NAT statement (don't know where that came from, guessing the ASDM threw it in there). However the issue remains. I can still ping the VPN clients from a server from within the internal network but can't ping the server from those clients (or any other host on the internal network). Very strange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Brilliant! That worked and the clients can now ping internal resources. Thank you very much for the assistance!
nat (inside) 0 access-list no_nat0_outbound
access-list no_nat0_outbound extended permit ip any 192.168.100.0 255.255.255.0
access-list no_nat0_outbound extended permit ip any 10.10.10.0 255.255.255.0