Ubuntu 16.04 Canonical Software Missing
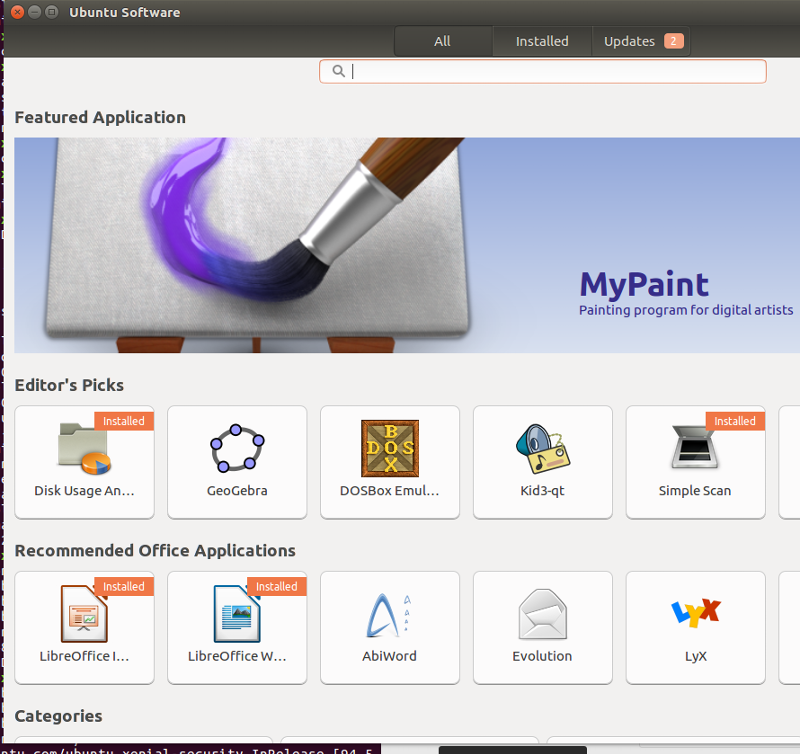
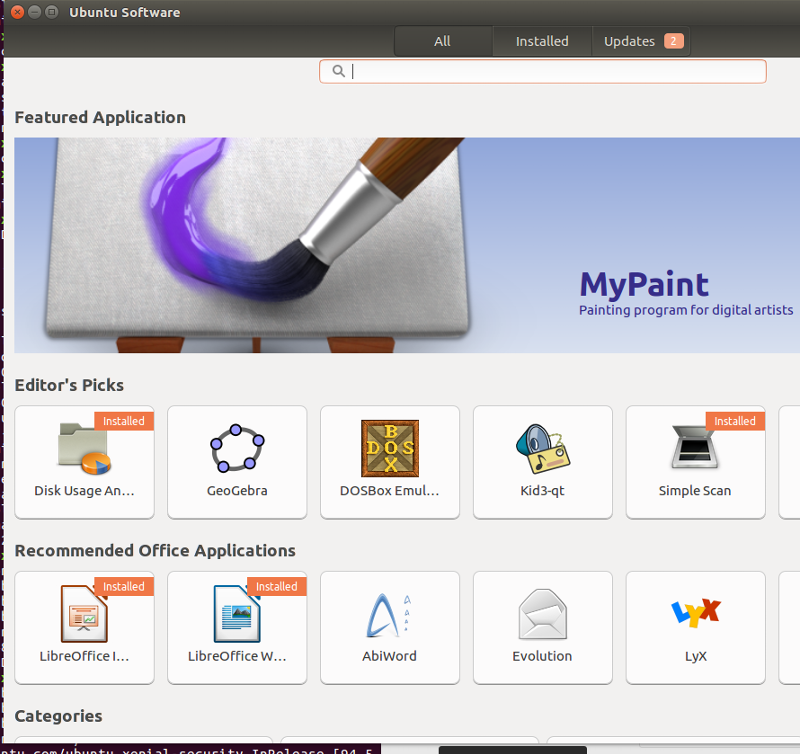
I have just downloaded Ubuntu 16.04 and I cannot find the commercial programs, even though I did enable Canonical in "Software & Updates".
The whole software center looks different. In Ubuntu 14 I could select with a drop-down whether I wanted to see the free and/or commercial programs.
What else do I need to change?
Thanks for your help.
The whole software center looks different. In Ubuntu 14 I could select with a drop-down whether I wanted to see the free and/or commercial programs.
What else do I need to change?
Thanks for your help.
ASKER
I have tried it with the following output.
But I still cannot see the other programs.
Hit:1 http://ch.archive.ubuntu.com/ubuntu xenial InRelease
Hit:2 http://ch.archive.ubuntu.com/ubuntu xenial-updates InRelease
Hit:3 http://ch.archive.ubuntu.com/ubuntu xenial-backports InRelease
Hit:4 http://archive.canonical.com/ubuntu xenial InRelease
Get:5 http://security.ubuntu.com/ubuntu xenial-security InRelease [94.5 kB]
Fetched 94.5 kB in 0s (160 kB/s)
Reading package lists... DoneBut I still cannot see the other programs.
ASKER
I remember that in Ubuntu 14, I could change from free to commercial programs by using a pull-down menu at the top. But the whole software center looks like a big overhaul.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Personally I'd rather suggest on installing and using Synaptic as GUI package manager. It is much easier to use and more straight forward than the software center stuff.