PeraHoman
asked on
HSRP question
Yes, you can. It would have to be configured under L3 interfaces.
Can you give more details?
The way question is written I am not sure that I understand what you want to achieve - and what is the purpose of HSRP here.
The way question is written I am not sure that I understand what you want to achieve - and what is the purpose of HSRP here.
ASKER
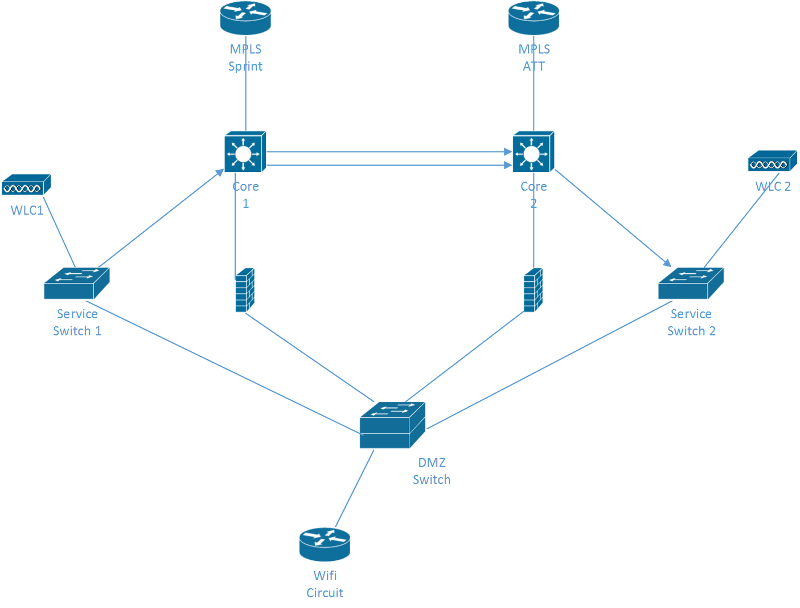
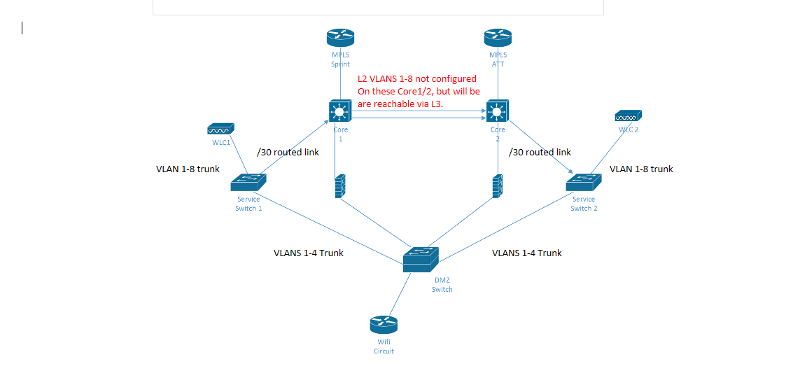
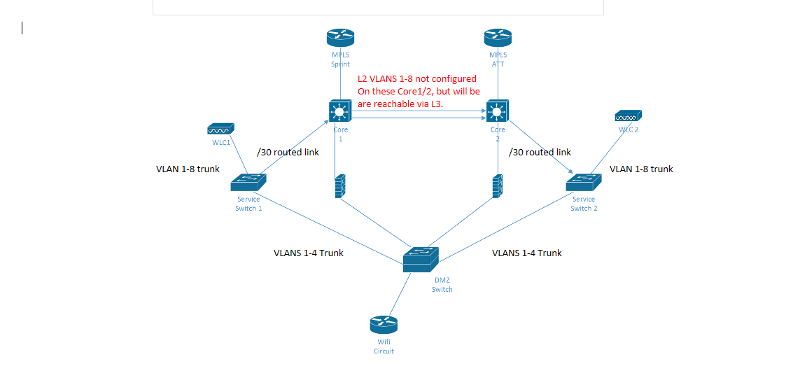
I'm wondering if it is possible to configure HSRP (8 standby groups - VLANS) between the service switches with this setup? Doesn't there need to be a L2 connection between the service switches? Will traversing through the DMZ as L2 trunk allow HSRP to work (See below)?
If the L2 connection through the DMZ works, the issue I have with that is only 4 of the 8 VLANS are trunked from the service switch through the DMZ, so I'd have to add the rest of the VLANs onto the trunk for HSRP for the rest of them.
Service Switch 1
VLAN 1-8
HSRP 1-8, priority 120
-Connection to core is L3 routed link
-Connection to DMZ is L2 trunk (only VLAN 1-4 allowed now)
Service Switch 1
VLAN 1-8
HSRP 1-8 priority 110
-Connection to core is L3 routed link
-Connection to DMZ is L2 trunk (only VLAN 1-4 allowed now)
DMZ Switch
Connection to both service switches is L2 trunk (only VLAN 1-4 allowed now)
If the L2 connection through the DMZ works, the issue I have with that is only 4 of the 8 VLANS are trunked from the service switch through the DMZ, so I'd have to add the rest of the VLANs onto the trunk for HSRP for the rest of them.
Service Switch 1
VLAN 1-8
HSRP 1-8, priority 120
-Connection to core is L3 routed link
-Connection to DMZ is L2 trunk (only VLAN 1-4 allowed now)
Service Switch 1
VLAN 1-8
HSRP 1-8 priority 110
-Connection to core is L3 routed link
-Connection to DMZ is L2 trunk (only VLAN 1-4 allowed now)
DMZ Switch
Connection to both service switches is L2 trunk (only VLAN 1-4 allowed now)
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Your diagram is correct, but only 1-4 will be trunked through the DMZ. Will HSRP work if for VLAN 5-8 since there is no L2 connectivity? The reason is because we are restricting 5-8 in the DMZ.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
So, HSRP doesn't require a L2 connection between them?
No, not strictly, but do not forget that IP addresses must be in the same subnet, so typically you need will have L2 device between devices, but not VLANs (so if you can get around that limitation problem solved). If you use subinterfaces you will again have to use dot1q, so - VLANs (not to mention discontiguous network problem in that case). But, you can configure HSRP on L3 interfaces, but, on the other hand,it can be also considered as native VLAN.
Also if you do not have L2 connectivity how you will forward packets? Typically, floating static route with IP SLA or dynamic routing is used for that purpose.
PS
I forgot above, HSRP group must match. :)
Also if you do not have L2 connectivity how you will forward packets? Typically, floating static route with IP SLA or dynamic routing is used for that purpose.
PS
I forgot above, HSRP group must match. :)
ASKER
Ok, to end this, the devices that participate in HSRP do not have to be physically connected, just reachable via L2 or L3.
Example:
- The core 1 and core 2 are connected (2 connections between them) and HSRP will work. (typical setups I've seen)
- Service switch 1 and service switch 2 are not connected but HSRP will work because but are connected via L3 (Service switch 1 -- Core 1-- Core 2 -- Service switch 2) VLANs 1-8 will work here.
As well as L2 (Service switch 1 -- DMZ switch -- Service switch 2) and HSRP will work for VLANs 1-4 ONLY because DMZ switch only has VLANs 1-4 and not VLAN 4-8 on switch/trunk.
I haven't done a setup where the HSRP was configured between two devices that weren't connected so I wasn't sure if HSRP was going to actually work.
Example:
- The core 1 and core 2 are connected (2 connections between them) and HSRP will work. (typical setups I've seen)
- Service switch 1 and service switch 2 are not connected but HSRP will work because but are connected via L3 (Service switch 1 -- Core 1-- Core 2 -- Service switch 2) VLANs 1-8 will work here.
As well as L2 (Service switch 1 -- DMZ switch -- Service switch 2) and HSRP will work for VLANs 1-4 ONLY because DMZ switch only has VLANs 1-4 and not VLAN 4-8 on switch/trunk.
I haven't done a setup where the HSRP was configured between two devices that weren't connected so I wasn't sure if HSRP was going to actually work.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Example of using HSRP without VLAN where it is valid design:
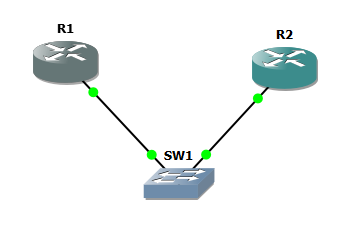
R1
R2
L2 tunnel can provide the same functionality (allow HSRP to work properly) on not physically connected devices, but what would be the point of that scenario?
R1
interface FastEthernet0/0
ip address 10.0.0.3 255.255.255.0 secondary
ip address 192.168.0.3 255.255.255.0
standby 1 ip 10.0.0.1
standby 2 ip 192.168.0.1R2
interface FastEthernet0/0
ip address 10.0.0.2 255.255.255.0 secondary
ip address 192.168.0.2 255.255.255.0
standby 1 ip 10.0.0.1
standby 2 ip 192.168.0.1L2 tunnel can provide the same functionality (allow HSRP to work properly) on not physically connected devices, but what would be the point of that scenario?
ASKER
I think we're on the same page, but it still goes back to my question to VLAN 5-8.
HSRP will be configured onto the VLAN interfaces of VLAN 1-8. I didn't details VLAN 1-4 below, but I know HSRP will work for VLANs 1-4 because they have L2 connectivity through the DMZ via trunks. They're wanting HSRP for VLANs 5-8 as well, but there isn't L2 connection for these VLANs 5-8 because the only VLANs 1-4 are allowed on the trunk to the DMZ switch.
Having a trunk between the service switches would make HSRP work for VLANs 5-8, and to make it short I know this isn't done normally. I want to know if HSRP will or will not work correctly for VLANs 5-8 in this scenario since there is no L2 connection between them. It was mentioned that it may work through the routed link to the core, but I don't think this is true since it needs L2?
I appreciate the input.
Service Switch 1
**Assume the rest of the L2/L3 VLANs and HSRP are created and configured correctly**
interface Vlan5
ip address 10.148.58.2 255.255.254.0
standby 982 ip 10.148.58.1
standby 982 priority 110
standby 982 preempt delay minimum 30
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to DMZ-Switch, , Te3/1
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4 (VLAN 5 not allowed)
switchport nonegotiate
spanning-tree portfast trunk
no shut
Service Switch 2
**Assume the rest of the L2/L3 VLANs and HSRP are created and configured correctly**
interface Vlan5
ip address 10.148.58.3 255.255.254.0
standby 982 ip 10.148.58.1
standby 982 priority 90
standby 982 preempt delay minimum 30
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to DMZ-Switch, Te3/2
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4
switchport nonegotiate
spanning-tree portfast trunk
no shut
DMZ Switch
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to Service Switch 1
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4 (VLAN 5 not allowed)
switchport nonegotiate
spanning-tree portfast trunk
no shut
interface TenGigabitEthernet3/2
Description L2-Guest-Traffic to Service Switch 2
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4
switchport nonegotiate
spanning-tree portfast trunk
no shut
HSRP will be configured onto the VLAN interfaces of VLAN 1-8. I didn't details VLAN 1-4 below, but I know HSRP will work for VLANs 1-4 because they have L2 connectivity through the DMZ via trunks. They're wanting HSRP for VLANs 5-8 as well, but there isn't L2 connection for these VLANs 5-8 because the only VLANs 1-4 are allowed on the trunk to the DMZ switch.
Having a trunk between the service switches would make HSRP work for VLANs 5-8, and to make it short I know this isn't done normally. I want to know if HSRP will or will not work correctly for VLANs 5-8 in this scenario since there is no L2 connection between them. It was mentioned that it may work through the routed link to the core, but I don't think this is true since it needs L2?
I appreciate the input.
Service Switch 1
**Assume the rest of the L2/L3 VLANs and HSRP are created and configured correctly**
interface Vlan5
ip address 10.148.58.2 255.255.254.0
standby 982 ip 10.148.58.1
standby 982 priority 110
standby 982 preempt delay minimum 30
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to DMZ-Switch, , Te3/1
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4 (VLAN 5 not allowed)
switchport nonegotiate
spanning-tree portfast trunk
no shut
Service Switch 2
**Assume the rest of the L2/L3 VLANs and HSRP are created and configured correctly**
interface Vlan5
ip address 10.148.58.3 255.255.254.0
standby 982 ip 10.148.58.1
standby 982 priority 90
standby 982 preempt delay minimum 30
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to DMZ-Switch, Te3/2
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4
switchport nonegotiate
spanning-tree portfast trunk
no shut
DMZ Switch
interface TenGigabitEthernet3/1
Description L2-Guest-Traffic to Service Switch 1
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4 (VLAN 5 not allowed)
switchport nonegotiate
spanning-tree portfast trunk
no shut
interface TenGigabitEthernet3/2
Description L2-Guest-Traffic to Service Switch 2
switchport trunk encap dot1q
switchport mode trunk
switchport allowed vlan 1-4
switchport nonegotiate
spanning-tree portfast trunk
no shut
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.