Processing configuration Error: A general system error occurred: The called function cannot be performed on partial chains. ]
I'm getting the following error message from one of my replication jobs:
Processing configuration Error: A general system error occurred: The called function cannot be performed on
partial chains. Open the parent virtual disk VM disk size changed since last sync, deleting all restore points
Error: A general system error occurred: The called function cannot be performed on partial chains. Open the
parent virtual disk
Has anyone seen this before and or no of a solution?
Processing configuration Error: A general system error occurred: The called function cannot be performed on
partial chains. Open the parent virtual disk VM disk size changed since last sync, deleting all restore points
Error: A general system error occurred: The called function cannot be performed on partial chains. Open the
parent virtual disk
Has anyone seen this before and or no of a solution?
ASKER
ASKER
there are no snapshots, that I can see.
what operation is trying to be performed, when the error occurs ?
I assume the VM is currently powered up?
what operation is trying to be performed, when the error occurs ?
I assume the VM is currently powered up?
ASKER
Yes it is powered up.
ASKER
However, when I look at the VM Server_replica, I see a Configuration Issue and it says Virtural machine disks consolidation is needed..
Can I consolidate the replica and still have the users attached to VM Server?
Can I consolidate the replica and still have the users attached to VM Server?
this is a replica, operations cannot be completed on a replica, because it's synced with the Parent VM!
what are you trying to do on the replica!?
what are you trying to do on the replica!?
ASKER
The attached is what I'm seeing when I look at my Virtual Devices.
I see a Configuration Issue and it says Virtual machine disks consolidation is needed..
VCenter.png
I see a Configuration Issue and it says Virtual machine disks consolidation is needed..
VCenter.png
Yes, it's a replica of a production VM, from VMware Replication or Veeam Backup and replication.
do you have a production VM which is currently on....called this?
Leave alone... or you will break the replica link between Parent and Replica!
do you have a production VM which is currently on....called this?
Leave alone... or you will break the replica link between Parent and Replica!
ASKER
Yes I do. OK!
Any suggestions?
Any suggestions?
Any suggestions for what ?
ASKER
About the original error:
I'm getting the following error message from one of my replication jobs:
Processing configuration Error: A general system error occurred: The called function cannot be performed on
partial chains. Open the parent virtual disk VM disk size changed since last sync, deleting all restore points
Error: A general system error occurred: The called function cannot be performed on partial chains. Open the
parent virtual disk
Has anyone seen this before and or no of a solution?
I'm getting the following error message from one of my replication jobs:
Processing configuration Error: A general system error occurred: The called function cannot be performed on
partial chains. Open the parent virtual disk VM disk size changed since last sync, deleting all restore points
Error: A general system error occurred: The called function cannot be performed on partial chains. Open the
parent virtual disk
Has anyone seen this before and or no of a solution?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks,
I will try this tonight.
I will try this tonight.
no problems
ASKER
Andrew Hancock,
I tried what your recommended, but now I'm getting the following error when I try to power on the VM:
An error was received from the ESX host while powering on VM wlldocsql.
Cannot open the disk '/vmfs/volumes/51af4020-b4
Now I'm stuck. Do you know how I can fix this?
The file specified is not a virtual disk
I tried what your recommended, but now I'm getting the following error when I try to power on the VM:
An error was received from the ESX host while powering on VM wlldocsql.
Cannot open the disk '/vmfs/volumes/51af4020-b4
Now I'm stuck. Do you know how I can fix this?
The file specified is not a virtual disk
possible the VMDK is corrupted, can you check if the VM is running on a snapshot disk.
see my EE Article for guidance
HOW TO: VMware Snapshots :- Be Patient
see my EE Article for guidance
HOW TO: VMware Snapshots :- Be Patient
ASKER
Last Night I ended up Recreating the VM Descriptor file. That allowed me to power on my VM, but I still have the original problem.
While trying to follow your advice, I got stuck at cloning the VM. I didn't have enough space in my datastore to complete the cloning.
While trying to follow your advice, I got stuck at cloning the VM. I didn't have enough space in my datastore to complete the cloning.
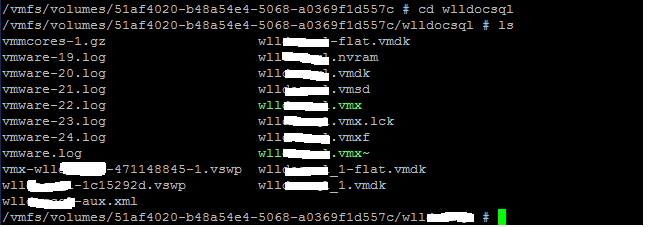
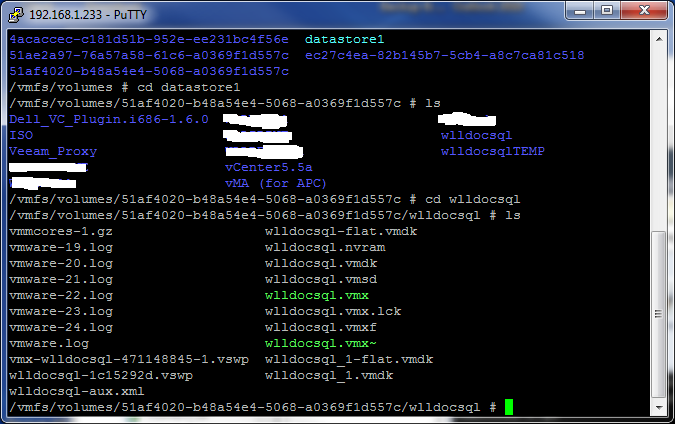
screenshot of VM folder and files please.
Is this a VDI client or server ?