Is CCleaner a virus? Do you use CCleaner?
Yes? Why do you use it?
No? Why don't you use it?
No? Why don't you use it?
Yes, for internet history cleanup, for registry cleanup after a load of malware removals or uninstalls, and recently the startup tools have been extremely useful.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
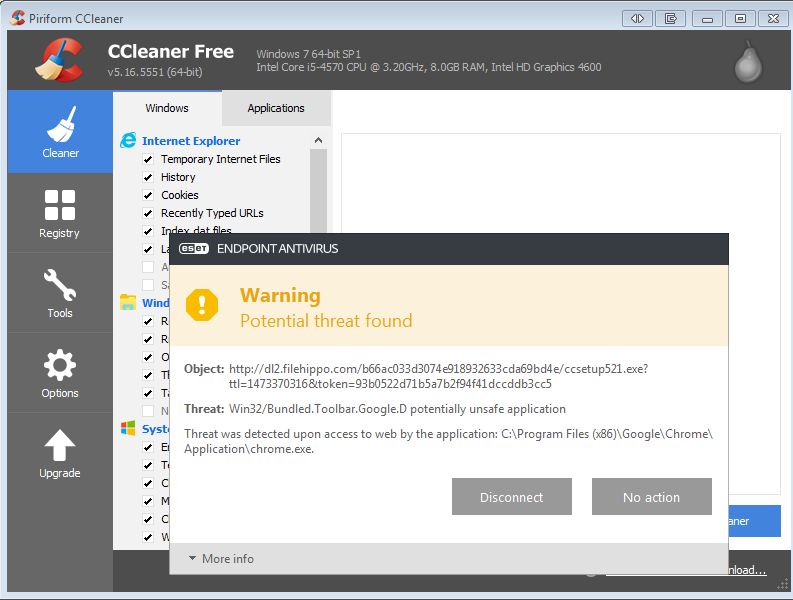
Thanks for the additional feedback. I figured it would be ok to update my version since its already installed, but I thought maybe the mirror to which I was downloading contained a virus? I don't know.
Personally, I started using it a few years ago upon a recommendation from a friend. I was told it would make my computer 'faster and clean useless crap'. What did I find? I found some noticeable areas of improvement, as well as, it cleaned a lot of areas of 'crap' that I've yet to need to go back and ever recover.
This is definitely an interesting split on feedback about the usage! =)
Personally, I started using it a few years ago upon a recommendation from a friend. I was told it would make my computer 'faster and clean useless crap'. What did I find? I found some noticeable areas of improvement, as well as, it cleaned a lot of areas of 'crap' that I've yet to need to go back and ever recover.
This is definitely an interesting split on feedback about the usage! =)
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you, everyone!
Beating a dead horse here, and necroposting I realize, but the corpse is still warm...so...
You'll get lots of heavily weighted opinions on this one. Here is my $0.02
Q: Will CCLEANER harm my system? Cause Apps to crash after I run it?
A: Meh Not really. To people who say otherwise I guarantee you there was some underlying issue with the app that was exposed. it is highly unlikely that CCleaner would cause it.
Q: Will CCLEANER speed up my system?
A: No
Q: What good is it then?
A: CCLEANER is good for cleaning up a few things. Every AV/AM/Cleaning tool has it's gaps. No one of them gets everything. Just like any good Golf bag, there is more than 1 type of club in there. CCLEANER is just another club.
Personally, I use CCLEANER on Workstations regularly. No issues. But I don't use it on a server unless it's non production. Servers have less of a chance of having apps/registry changes installed and uninstalled repeatedly.
You'll get lots of heavily weighted opinions on this one. Here is my $0.02
Q: Will CCLEANER harm my system? Cause Apps to crash after I run it?
A: Meh Not really. To people who say otherwise I guarantee you there was some underlying issue with the app that was exposed. it is highly unlikely that CCleaner would cause it.
Q: Will CCLEANER speed up my system?
A: No
Q: What good is it then?
A: CCLEANER is good for cleaning up a few things. Every AV/AM/Cleaning tool has it's gaps. No one of them gets everything. Just like any good Golf bag, there is more than 1 type of club in there. CCLEANER is just another club.
Personally, I use CCLEANER on Workstations regularly. No issues. But I don't use it on a server unless it's non production. Servers have less of a chance of having apps/registry changes installed and uninstalled repeatedly.
ASKER
Piriform advised people with CCleaner v5.33.6162 or CCleaner Cloud v1.07.3191 installed on their machines to delete them and download new versions as soon as possible. The software doesn't update automatically.
https://www.cnet.com/news/hackers-hid-malicious-code-in-popular-ccleaner-software/#ftag=CAD590a51e
If you are running a 64 bit OS with the 64 bit version of CCleaner you are OK.
It is essentially only those people who are using the 32 bit version of CCleaner v5.33.6162 (or the Cloud version) who are in trouble.
Check the registry for this key HKLM\SOFTWARE\Piriform\Ago
Also see https://www.ghacks.net/2017/09/18/ccleaner-compromised-better-check-your-pc/
It is essentially only those people who are using the 32 bit version of CCleaner v5.33.6162 (or the Cloud version) who are in trouble.
Check the registry for this key HKLM\SOFTWARE\Piriform\Ago
Also see https://www.ghacks.net/2017/09/18/ccleaner-compromised-better-check-your-pc/
ASKER
Nice. Thanks for the clarity on that.