Is it possible to obtain the creation script of an Access database?
Hi Experts
Is it possible to obtain the creation script of an Access database?
If so, how to do that?
Thanks in advance.
Is it possible to obtain the creation script of an Access database?
If so, how to do that?
Thanks in advance.
ASKER
Hi
I meant by creation script all the commands needed to create tables and relations between them PK, FK, index, constraints etc. giving an existing database.
I meant by creation script all the commands needed to create tables and relations between them PK, FK, index, constraints etc. giving an existing database.
There's a tool called DBWScript that does this. The full trial works for a month, then the cost is $29 http://dbweigher.com/dbwscript.php
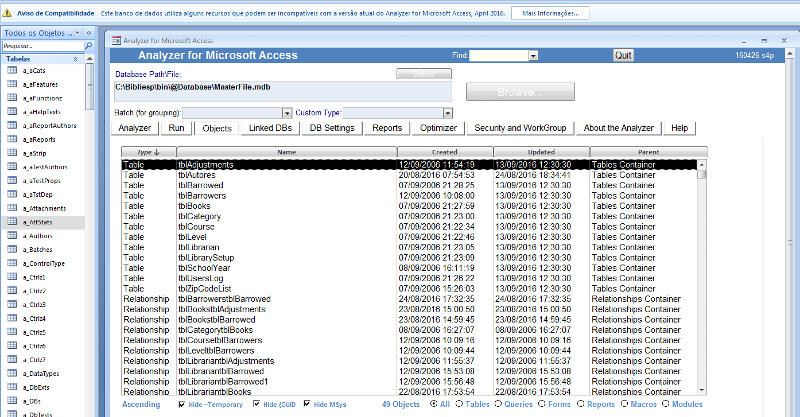
Crystal Long (strive4peace) has this free tool:
https://analyzer.codeplex.com/
You could possibly take the output from that and construct new tables.
Alternatively, you could import the tables' structures using the import wizard.
https://analyzer.codeplex.com/
You could possibly take the output from that and construct new tables.
Alternatively, you could import the tables' structures using the import wizard.
ASKER
Hi and thank you for the replies
@Ferruccio
The tool you suggested generates an script that seens have to be all rewrited to run.... I don't know it's caused by Access 2007 I'm using, directives like COMPRESSION and fields into brackets [ ]
aren't accepted.
@aikimark
I saw the video, it seens a free and very good tool, my interest is in database itself (I'm using C# - not access forms). It's not clear to me if it simply generates the DDL code for database recreation.
@Ferruccio
The tool you suggested generates an script that seens have to be all rewrited to run.... I don't know it's caused by Access 2007 I'm using, directives like COMPRESSION and fields into brackets [ ]
aren't accepted.
CREATE TABLE [tblAdjustments] (
[BookNumber] LONG,
[AdjustBy] TEXT(50) WITH COMPRESSION,
[DateAdjust] DATETIME
);@aikimark
I saw the video, it seens a free and very good tool, my interest is in database itself (I'm using C# - not access forms). It's not clear to me if it simply generates the DDL code for database recreation.
That "with compression" keyword makes me think the utility is designed for SQL Server output.
ASKER
I had defined it to create as Access Script
(It doesn't runs as SQLServer script too... )
(It doesn't runs as SQLServer script too... )
ASKER
I pinged the author of the utility. Hopefully, Crystal will shed some light on the utility.
ASKER
Ok. Thank you by now.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
ASKER
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
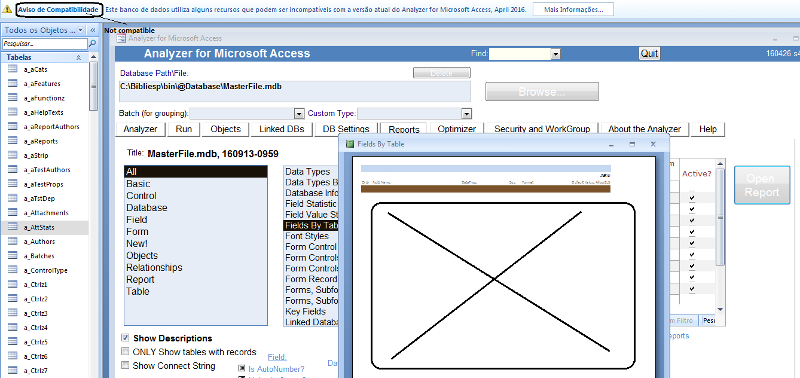
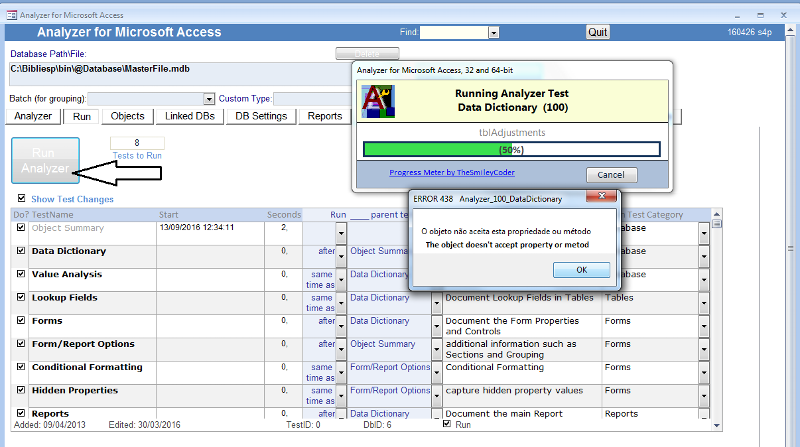
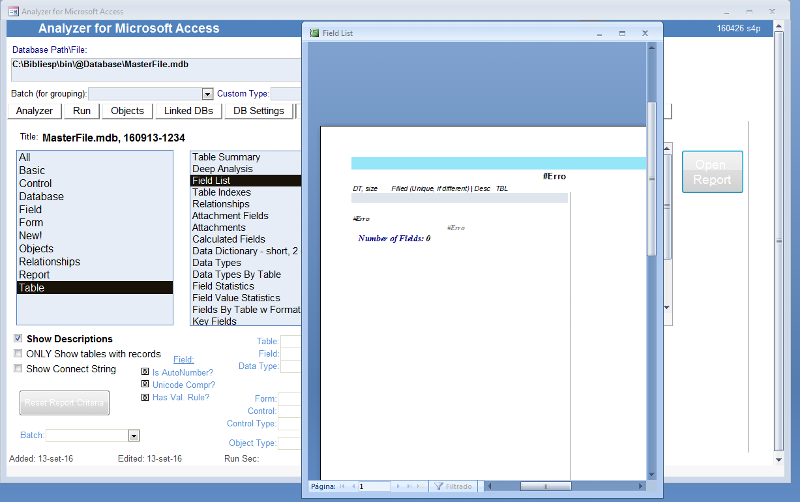
@crystal
I downloaded and ran. The table reports are still blank.
A log error erased (attached).
ErrorLog_Analyzer.txt
I downloaded and ran. The table reports are still blank.
A log error erased (attached).
ErrorLog_Analyzer.txt
ASKER
Backing to DBWScript/ DBWConsole
The tool 1st generated its own "metadata" by using DBWScript. Something useful only by DBWConsole. So in truth it doesn't create an Access DDL
Then is needed to use DBWConsole, create a .mdb by using this tool, open the metadata script and then run it.
The new database will be a clone of the previous database. I'm wondering in what it is advantageous to use it...making a backup copy of database could be more util.
The tool 1st generated its own "metadata" by using DBWScript. Something useful only by DBWConsole. So in truth it doesn't create an Access DDL
Then is needed to use DBWConsole, create a .mdb by using this tool, open the metadata script and then run it.
The new database will be a clone of the previous database. I'm wondering in what it is advantageous to use it...making a backup copy of database could be more util.
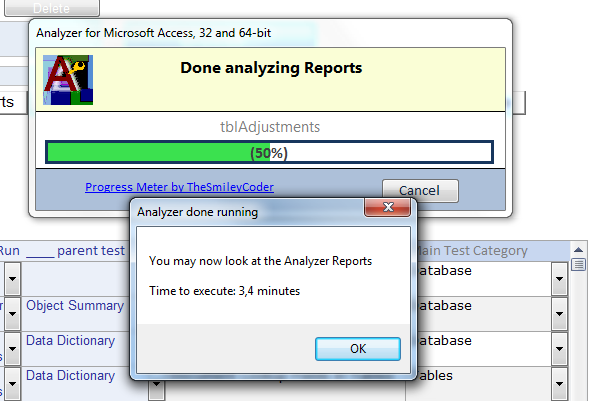
can you switch the language to English? That is what the code is written in. If not, open the tables directly -- you can also create another database and import all the tables. That will give you the results of the analysis
ASKER
@crystal
Your suggestion is directly to read the tables Analyzer tables?
If so, I did that, hard to interpretate its contents.
Your suggestion is directly to read the tables Analyzer tables?
If so, I did that, hard to interpretate its contents.
Yes. There is a query called "qFields" you can look at -- but if you modify it, give it a different name. I often open that query and put its information into Excel then delete what I don't want. The fields are named logically (at least I think so). Once you see what they are called and the information they have, I think you will get the logic.
ASKER
Ok. Good to know this resources, certainly it will be useful in the future.
Backing the original subject of the question it's amazing how difficult is to find by now a feature that could obtain a DDL script for an existing Access database. As I read you are planning to do that...
Backing the original subject of the question it's amazing how difficult is to find by now a feature that could obtain a DDL script for an existing Access database. As I read you are planning to do that...
yes I am ... and now perhaps sooner --- desire from others drives me ;)
ASKER
I guess you teached the lesson in youtube also, isn't it?
Thanks for your kindness and dedication.
Thanks for your kindness and dedication.
ASKER
Congratulations for the product you are constantly improving.
I hope the next version could cover DDL generation for Access database,
Thanks for the guidance!
I hope the next version could cover DDL generation for Access database,
Thanks for the guidance!
thank you and you're welcome, Eduardo ~ happy to help
/gustav