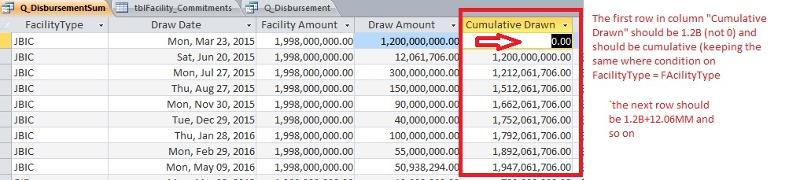
Cumulative (Running Sum) in a query
Experts, I need my query (in the attached sample db) to return a cumulative amount for each tblDraws_Details1.[Amount]
= $1,212,061,706.00. What I am looking for is a running sum for tblDraws_Details1.[Amount]
How would an expert do this? I have taken too much time trying to modify.
thank you
I have attached a database.
Please open the query: Q_DisbursementSum
 BalanceEE.accdb
BalanceEE.accdb
= $1,212,061,706.00. What I am looking for is a running sum for tblDraws_Details1.[Amount]
How would an expert do this? I have taken too much time trying to modify.
thank you
I have attached a database.
Please open the query: Q_DisbursementSum
 BalanceEE.accdb
BalanceEE.accdb
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
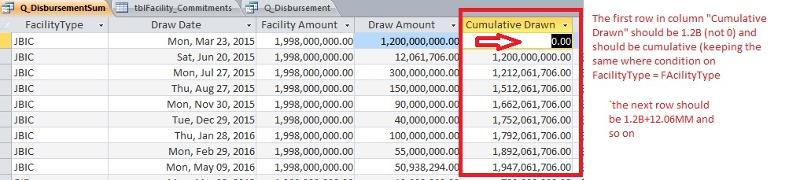
I see where the edit is:
Old
And T.ValueDate <= Q_Disbursement.ValueDate)-
Your solution:
And T.ValueDate <= Q_Disbursement.ValueDate) AS [Cumulative Drawn],
I see my old way subtracted the Sum([Amount]) and that is where I was wrong.
Unfortunately, I will forget what I learned by tomorrow. :(
thank you for the help Ryan.
Old
And T.ValueDate <= Q_Disbursement.ValueDate)-
Your solution:
And T.ValueDate <= Q_Disbursement.ValueDate) AS [Cumulative Drawn],
I see my old way subtracted the Sum([Amount]) and that is where I was wrong.
Unfortunately, I will forget what I learned by tomorrow. :(
thank you for the help Ryan.
ASKER