Finding out if the TLS data was compressed from a wireshark capture
Hi,
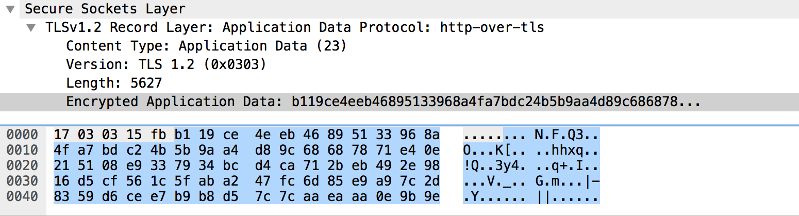
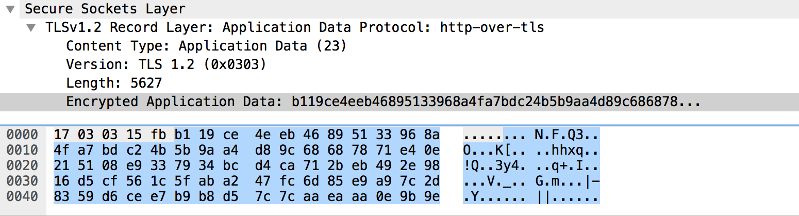
Following is a TLS record captured in the wireshark...
 I read in a book that TLS data should not be compressed so wanted to verify if it is getting compressed in my web application.
I read in a book that TLS data should not be compressed so wanted to verify if it is getting compressed in my web application.
This is a TLS record of data transfered between my computer and server...
How do i see from the record that the data is compressed or not ?
Also one thing i dont understand in the capture is that the Encrypted application data is different from what is shown in the below tab of wireshark . Why is that ?
Thanks
Following is a TLS record captured in the wireshark...
 I read in a book that TLS data should not be compressed so wanted to verify if it is getting compressed in my web application.
I read in a book that TLS data should not be compressed so wanted to verify if it is getting compressed in my web application.This is a TLS record of data transfered between my computer and server...
How do i see from the record that the data is compressed or not ?
Also one thing i dont understand in the capture is that the Encrypted application data is different from what is shown in the below tab of wireshark . Why is that ?
Thanks
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.