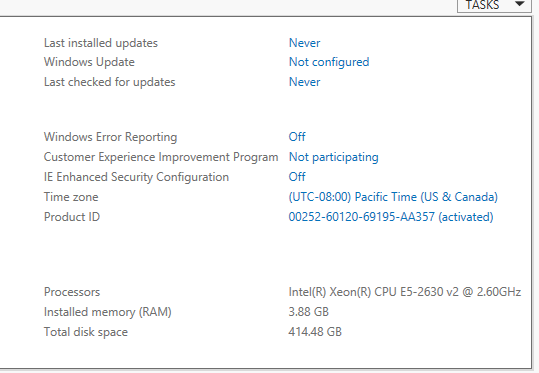
Win 2012 R2 not recognizing correct RAM
Is the host also 2012 R2? Why was 2008 selected as a tag?
ASKER
yes, the host is also 2012 R2. I selected 2008 as a tag just to give my question more visibility.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
No, I'm using static memory. Since it's a SQL box, I was thinking the static memory will be better or faster than the dynamic.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I'm using 64 bit.
The host has been fully updated with windows updates. I will update the VM, I have not done
That yet. Just for kicks to rule that out, I will
Change the ram to dynamic and see what happens.
I have already restarted the VM a few times.
The host has been fully updated with windows updates. I will update the VM, I have not done
That yet. Just for kicks to rule that out, I will
Change the ram to dynamic and see what happens.
I have already restarted the VM a few times.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Actually, since MS creates a dynamic disk by default, I tried converting it to fixed, but ran out of space, so I deleted the VM and am creating a new one. This issue might be a mute point after the disk is created.
Thanks for everyone's help, I'll see what happens with the next install of the OS.
Thanks for everyone's help, I'll see what happens with the next install of the OS.