Getting #Type! error in expression builder
Dear Experts,
Wondering if you all could help me with this expression:
The following expression is in the control source of txtPercentPos:
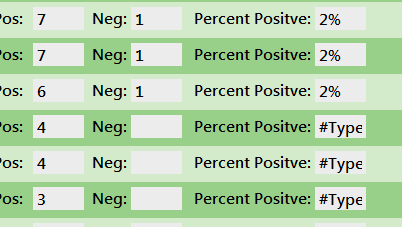
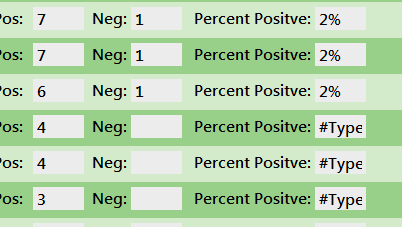
but when I display the continuous form I get:
How can I prevent the error from happening if there are no values in the txtPosCnt or txtNegCnt textboxes?
Thanks!
Wondering if you all could help me with this expression:
The following expression is in the control source of txtPercentPos:
=Format((Val([txtPosCnt])/Val([txtPosCnt])+Val([txtNegCnt]))/100,"#%")but when I display the continuous form I get:
How can I prevent the error from happening if there are no values in the txtPosCnt or txtNegCnt textboxes?
Thanks!
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Joe,
This works if txtNegCnt is blank but errors if txtPosCnt is blank as well. Can you assist with check if both fields are blank?
This works if txtNegCnt is blank but errors if txtPosCnt is blank as well. Can you assist with check if both fields are blank?
ASKER
Nevermind! Figured it out! Thanks again!
Cool. Mainly, you have to prevent Divide By Zero ....and ... Null propagation - hence the Nz() to convert Null to Zero.
Sorry ... I went to bed shortly after that post.
Sorry ... I went to bed shortly after that post.
Open in new window