Crystal Reports conditional formula execution based upon field contents
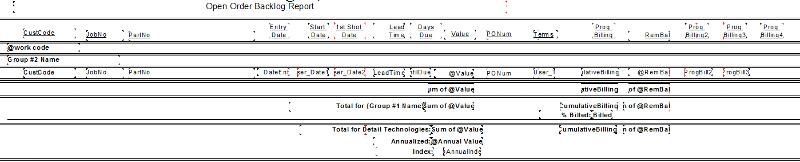
I developed an Order Backlog report to forecast anticipated billing dates. Some of our orders are "progress billings"... where the order is based upon various milestones:
The Prog Billing2, Prog Billing3 and Prog Billing3 dates are calculated from the Start Date and the 1st Shot Date using the formula: DateADD ("d", 90, {OrderDet.User_Date1})
If the Terms are something other than a Progress Billing Term code, I don't want the dates to appear under the Prog Billing2, Prog Billing3 and Prog Billing3 headings.
I've tried using IF IsNull{OrderDet.CumulativeBillin
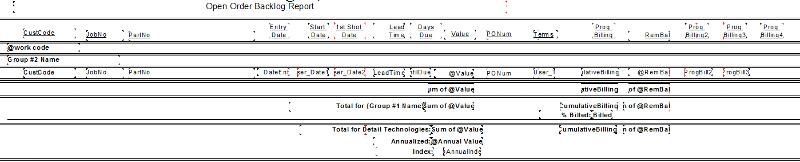
Order-Backlog-Progress-Billings.pdf
Thanks for any suggestions.
Regards, Lee
- First 1/3 with Purchase Order
- Second 1/3 at delivery
- Final 1/3 at plant approval
The Prog Billing2, Prog Billing3 and Prog Billing3 dates are calculated from the Start Date and the 1st Shot Date using the formula: DateADD ("d", 90, {OrderDet.User_Date1})
If the Terms are something other than a Progress Billing Term code, I don't want the dates to appear under the Prog Billing2, Prog Billing3 and Prog Billing3 headings.
I've tried using IF IsNull{OrderDet.CumulativeBillin
Order-Backlog-Progress-Billings.pdf
Thanks for any suggestions.
Regards, Lee
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Perfect.
You are the man!
Thanks Michael.
You are the man!
Thanks Michael.
ASKER
Thanks for the response.
Are you suggesting I add the NOT({TermsField} LIKE '*PROG*') to my ProgBill formula?
If so, I'm not certain how??
The ProgBilling2 field is the StartDate Field plus 90 days using ProgBill2 formula:
DateADD ("d", 90, {OrderDet.User_Date1})
The ProgBilling3 field is the 1StShotDate field plus 120 days using ProgBill3 formula:
DateADD ("d", 120, {OrderDet.User_Date2})
Regards, Lee
ProgBill2-formula.pdf