Dustin Stanley
asked on
MS Access How To Set Up Keeping Part Sheets, Owners Manuals, PDF Forms and Other Documents In Access Organized
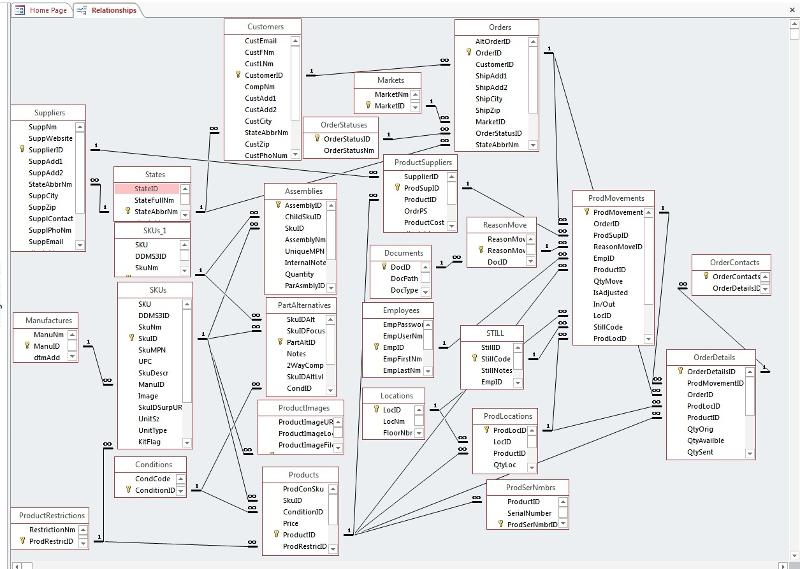
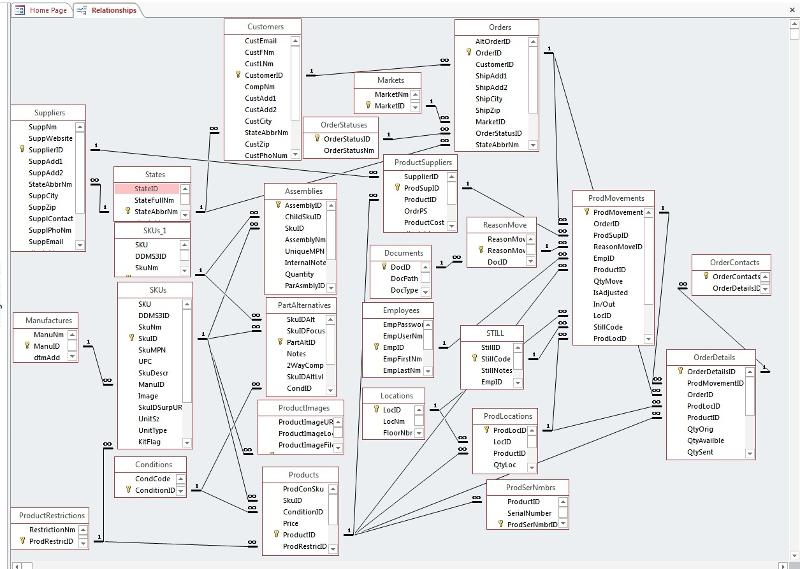
I was wondering ways to setup keeping track of documents like Jpg Pdf and so on in Access. These would mainly be for Repair Manuals, Parts Manuals, and General Documentation about a specific SkuID (SkuID Found in my SKUs Table). The files will be stored in a folder just below the Database Backend.
The user would be using these files and searching for these files to use pretty frequently.
How would I set up the table and forms for this?
Thank you for suggestions and ideas!
The user would be using these files and searching for these files to use pretty frequently.
How would I set up the table and forms for this?
Thank you for suggestions and ideas!
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
By "store at a higher level", I meant - store the path at the level which controlled it. So for example, If I wanted to separate files by department, I would store the path in the department record.
How granular you should get is largely dictated by how structured the existing file names are and the number of files that will be in any folder. You want to make it as easy as possible for the users to get the file into the correct folder. In one app, I programatically download completed files from an FTP folder. The file name includes the ClientID. I use that to look up the client record and find the folder name for that client's files. Users don't want folders named 1234. They want to see "My Special Robots" as the file name.
How granular you should get is largely dictated by how structured the existing file names are and the number of files that will be in any folder. You want to make it as easy as possible for the users to get the file into the correct folder. In one app, I programatically download completed files from an FTP folder. The file name includes the ClientID. I use that to look up the client record and find the folder name for that client's files. Users don't want folders named 1234. They want to see "My Special Robots" as the file name.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
That's a good idea for images John but I think Dustin is dealing with lots of documents, not images so having thumbnails wouldn't help him
Thats why @PatHartman i mentiond PDFs...covers...summarys..
Firebird doesn't care what you are storing...its up to "you" to organize table so that it can present the user the least needed information to access the needed information...
Firebird doesn't care what you are storing...its up to "you" to organize table so that it can present the user the least needed information to access the needed information...
ASKER
Ok lets keep it simple for now but NOT to simple. Something that can grow with me. My main foucus for now is the Tech department (Repair, Diassemble, and Testing).
So I would store these files in a folder that only the Tech Room can access, Correct?
Lets just say we are starting all over from scratch. So there are no files yet. So think of it as a new canvas and tell me your best thoughts.
The Table:
Besides FileName,DateAdd, DateEdit,FileExtension and EmployeeID what other fields would you suggest?
What kind of relationships would I need?
Would this only be a single table situation or would I need multiple tables?
The Files:
How would you name them for simplicity to find?
Tags??? I know about them but never used or looked into them. Would this be a good thing for me?
I don't really plan on the end user to generate these files and such and name them and file them away. Just be able to say "Here is this product and here are the documents that go with it." so they can service, test or disassemble the product.
Filing and naming away should probably be left up to a higher or specific employee or manager.
PDFs do have covers and I use them in my own PC when looking for a specific one. Very helpful.
So I would store these files in a folder that only the Tech Room can access, Correct?
How granular you should get is largely dictated by how structured the existing file names are and the number of files that will be in any folder.
Lets just say we are starting all over from scratch. So there are no files yet. So think of it as a new canvas and tell me your best thoughts.
The Table:
Besides FileName,DateAdd, DateEdit,FileExtension and EmployeeID what other fields would you suggest?
What kind of relationships would I need?
Would this only be a single table situation or would I need multiple tables?
The Files:
How would you name them for simplicity to find?
Tags??? I know about them but never used or looked into them. Would this be a good thing for me?
I don't really plan on the end user to generate these files and such and name them and file them away. Just be able to say "Here is this product and here are the documents that go with it." so they can service, test or disassemble the product.
Filing and naming away should probably be left up to a higher or specific employee or manager.
That's a good idea for imagesThat is very true. I am for this specific question mainly using documents but I have a application that may just benefit from Johns answer.
PDFs do have covers and I use them in my own PC when looking for a specific one. Very helpful.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Firebird is totally free.....no restrictions what so ever..
ASKER
Thank you guys. I will see what I can do with your the information you gave. Again thanks for your time!
I would be quite cautious of entrusting my production data to a "free" application. Nothing is actually free in this world despite what the left would have you believe. Someone is monetizing this application. Volunteers may provide support on an "as they have time" basis much in the way experts answer questions here but don't expect to call me personally to solve a production problem just because I answered a question for you.
"Free" applications probably are right now the backbone of our digital world ...MySQL, Apache, PHP.....to mention a few....
Nothing in this world is totally free because usually what you save from buying a product it is wasted on work hours...but....when something is free ...is free
Nothing in this world is totally free because usually what you save from buying a product it is wasted on work hours...but....when something is free ...is free
I think we're going to have to agree to disagree on this point.
Thats fine by me :)
ASKER
Ok I am going to give you an example Pat and you tell me what you think of my questions from that example.
Lets say I have a Dell Laptop Model A1B2 (SkuID 3303)
Documents needed for this could be like User Manuals, Service Manuals, and Parts Diagrams.
You say group them. Would I have a folder for only Service Manuals and then put all the SkuIDs (SkuID 3303,4456,7853,etc...) Service Manuals in it?
(Maybe a subform for this to show matching files for that specific SkuID)
And then the same for User Manuals and Parts Diagrams and so on?
You say store it at a higher level? Im a little confused. I planned on placing the folders diectly under the database file. So the database would be in a location and next to it would be the folder.
Also what would the table setup look like?
Of course if I was linking by SkuID then I would have to have a SkuID FK in the table but what other fields and what other links might I want?
Thanks for the help.