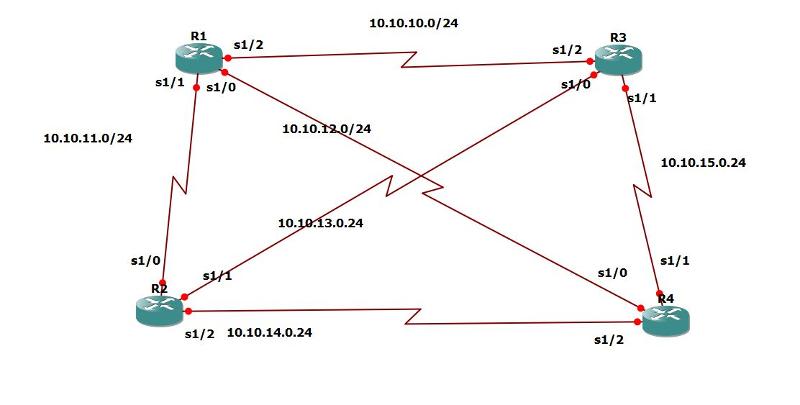
EIGRP Full Mesh
I have an EIGRP Routers in Full Mesh as shown below. I would like to know what is the down side about having Full Mesh. For instance:
if it can create a Loop
if one router or interface Fails, how to prevent unnecessary queries to fly around the whole network
And probably more issues can stem out of the Full Mesh
Any EE insights on this ?
Thank you
if it can create a Loop
if one router or interface Fails, how to prevent unnecessary queries to fly around the whole network
And probably more issues can stem out of the Full Mesh
Any EE insights on this ?
Thank you
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER