ASA 5506 blocks telnet
Dear Experts,
i have a very anoying and obsolete issue.
A customer of ours has an old school device with telnet enabled on the inside interface of the cisco ASA.
I have created a permit 23 ACL and a NAT port forward.
I cant figure out why my port forward is not working.
It looks like the cisco asa has reserved port 23 for itself or blocked by the service policys.
i cant find the setting.
I tried the oldschool commands Line vty. but it doesn't work on the new Cisco Asa's :) obviously.
Is there anything i forgot to check?
my code:
i have a very anoying and obsolete issue.
A customer of ours has an old school device with telnet enabled on the inside interface of the cisco ASA.
I have created a permit 23 ACL and a NAT port forward.
I cant figure out why my port forward is not working.
It looks like the cisco asa has reserved port 23 for itself or blocked by the service policys.
i cant find the setting.
I tried the oldschool commands Line vty. but it doesn't work on the new Cisco Asa's :) obviously.
Is there anything i forgot to check?
my code:
: Serial Number:
: Hardware: ASA5506, 4096 MB RAM, CPU Atom C2000 series 1250 MHz, 1 CPU (4 cores)
:
ASA Version 9.6(2)3
!
hostname XXX-XXX-ASA
domain-name XXX.local
enable password encrypted
names
ip local pool XXX_DHCP 10.56.13.100-10.56.13.200 mask 255.255.255.0
!
interface GigabitEthernet1/1
nameif outside
security-level 0
ip address XXXX 255.255.255.0
!
interface GigabitEthernet1/2
nameif inside
security-level 100
ip address 10.56.12.254 255.255.255.0
!
interface GigabitEthernet1/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/6
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/7
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1/8
shutdown
no nameif
no security-level
no ip address
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
!
boot system disk0:/asa962-3-lfbff-k8.SPA
boot system disk0:/asa961-lfbff-k8.SPA
ftp mode passive
clock timezone CEST 1
clock summer-time CEDT recurring last Sun Mar 2:00 last Sun Oct 3:00
dns domain-lookup outside
dns domain-lookup inside
dns server-group DefaultDNS
domain-name xxx.local
object network obj_any
subnet 0.0.0.0 0.0.0.0
object network FWD_DC_RDP
host 10.56.12.1
object network INSIDE_xxx-xxx-DC01
host 10.56.12.1
object network INSIDE_xxx-xxx-HYP01
host 10.56.12.10
object network INSIDE_xxx-xxx-ILO
host 10.56.12.9
object network INSIDE_xxx-xxx-APP01
host 10.56.12.2
object network FWD_APP_RDP
host 10.56.12.2
object network FWD_HYP_RDP
host 10.56.12.10
object network FWD_ILO_161
host 10.56.12.9
object network FWD_ILO_162
host 10.56.12.9
object network FWD_ILO_17988
host 10.56.12.9
object network FWD_ILO_17990
host 10.56.12.9
object network FWD_ILO_24
host 10.56.12.9
object network FWD_ILO_445
host 10.56.12.9
object network FWD_ILO_58080
host 10.56.12.9
object network xxxxThuis
host xxx
object network xxxKantoor
host xxx
object network NETWORK_OBJ_10.56.12.192_26
subnet 10.56.12.192 255.255.255.192
object network xxx_Network
subnet 10.56.12.0 255.255.255.0
object network xxx-VPN_Network
subnet 10.56.13.0 255.255.255.0
object network EXTERN_xxx
host xxx
object network EXTERN_xxx
host xxxx
object network EXTERN_xxx
host xxx
object network FWD_APP_808
host 10.56.12.2
object network EXTERN_xxx
host xxxx
object network FWD_CAM1_554_TCP
host 10.56.12.40
object network FWD_CAM2_21_TCP
host 10.56.12.45
object network FWD_CAM2_23_TCP
host 10.56.12.45
object network INSIDE_xxx-xxx-CAM1
host 10.56.12.40
object network INSIDE_xxx-xxx-CAM2
host 10.56.12.45
object network EXTERN_PRIMA-1
host 8xxx
object network EXTERN_PRIMA-2
host xxx
object network FWD_CAM1_554_UDP
host 10.56.12.40
object network FWD_CAM1_2000_TCP
host 10.56.12.40
object network FWD_CAM1_2000_UDP
host 10.56.12.40
object network FWD_CAM2_21_UDP
host 10.56.12.45
object network FWD_CAM2_23_UDP
host 10.56.12.45
object network EXTERN_IMPULS
host xxxx
object-group network GROUP_BEHEER
network-object object xxxThuis
network-object object xxxKantoor
object-group service DM_INLINE_TCP_1 tcp
port-object eq 3389
port-object eq 4489
object-group service DM_INLINE_TCP_2 tcp
port-object eq 3389
port-object eq 5589
object-group service DM_INLINE_TCP_3 tcp
port-object eq 3389
port-object eq 6689
port-object eq 808
object-group service DM_INLINE_TCP_4 tcp
port-object eq 161
port-object eq 162
port-object eq 17988
port-object eq 17990
port-object eq 24
port-object eq 58080
port-object eq ssh
port-object eq 445
object-group network GROUP_APPLICATIE-BEHEER
network-object object EXTERN_Gxxx
network-object object xxx
network-object object xxx
network-object object xxx
network-object object xxx
object-group network DM_INLINE_NETWORK_1
group-object GROUP_APPLICATIE-BEHEER
group-object GROUP_BEHEER
object-group network DM_INLINE_NETWORK_2
group-object GROUP_APPLICATIE-BEHEER
group-object GROUP_BEHEER
object-group service DM_INLINE_SERVICE_1
service-object tcp destination eq 2000
service-object tcp destination eq rtsp
service-object udp destination eq 2000
service-object udp destination eq 554
object-group service DM_INLINE_SERVICE_2
service-object tcp destination eq ftp
service-object tcp destination eq telnet
service-object udp destination eq 21
service-object udp destination eq 23
object-group network GROUP_CAM-BEHEER
network-object object xxx1
network-object object xxx2
object-group network DM_INLINE_NETWORK_3
group-object GROUP_BEHEER
group-object GROUP_CAM-BEHEER
object-group network DM_INLINE_NETWORK_4
group-object GROUP_BEHEER
group-object GROUP_CAM-BEHEER
access-list outside_access_in extended permit tcp object-group DM_INLINE_NETWORK_1 object INSIDE_xxx-xxx-DC01 object-group DM_INLINE_TCP_1
access-list outside_access_in extended permit tcp object-group GROUP_BEHEER object INSIDE_xxx-xxx-HYP01 object-group DM_INLINE_TCP_2
access-list outside_access_in extended permit tcp object-group GROUP_BEHEER object INSIDE_xxx-xxx-ILO object-group DM_INLINE_TCP_4
access-list outside_access_in extended permit tcp object-group DM_INLINE_NETWORK_2 object INSIDE_xxx-xxx-APP01 object-group DM_INLINE_TCP_3
access-list outside_access_in extended permit object-group DM_INLINE_SERVICE_1 object-group DM_INLINE_NETWORK_3 object INSIDE_xxx-xxx-CAM1
access-list outside_access_in extended permit object-group DM_INLINE_SERVICE_2 object-group DM_INLINE_NETWORK_4 object INSIDE_xxx-xxx-CAM2
access-list outside_access_in extended permit icmp any any
access-list AnyConnect_Client_Local_Print extended deny ip any4 any4
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq lpd
access-list AnyConnect_Client_Local_Print remark IPP: Internet Printing Protocol
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 631
access-list AnyConnect_Client_Local_Print remark Windows' printing port
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 9100
access-list AnyConnect_Client_Local_Print remark mDNS: multicast DNS protocol
access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.251 eq 5353
access-list AnyConnect_Client_Local_Print remark LLMNR: Link Local Multicast Name Resolution protocol
access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.252 eq 5355
access-list AnyConnect_Client_Local_Print remark TCP/NetBIOS protocol
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 137
access-list AnyConnect_Client_Local_Print extended permit udp any4 any4 eq netbios-ns
access-list Anyconnect_ACL standard permit 10.56.12.0 255.255.255.0
pager lines 24
logging enable
logging asdm informational
mtu outside 1500
mtu inside 1500
no failover
no monitor-interface service-module
icmp unreachable rate-limit 1 burst-size 1
icmp permit host xxxoutside
icmp permit host xxxoutside
asdm image disk0:/asdm-762-150.bin
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 16384
nat (outside,inside) source static xxx-VPN_Network xxx-VPN_Network destination static xxx_Network xxx_Network no-proxy-arp route-lookup
!
object network obj_any
nat (any,outside) dynamic interface
object network FWD_DC_RDP
nat (inside,outside) static interface service tcp 3389 4489
object network FWD_APP_RDP
nat (inside,outside) static interface service tcp 3389 6689
object network FWD_HYP_RDP
nat (inside,outside) static interface service tcp 3389 5589
object network FWD_ILO_161
nat (inside,outside) static interface service tcp 161 161
object network FWD_ILO_162
nat (inside,outside) static interface service tcp 162 162
object network FWD_ILO_17988
nat (inside,outside) static interface service tcp 17988 17988
object network FWD_ILO_17990
nat (inside,outside) static interface service tcp 17990 17990
object network FWD_ILO_24
nat (inside,outside) static interface service tcp ssh 24
object network FWD_ILO_445
nat (inside,outside) static interface service tcp 445 445
object network FWD_ILO_58080
nat (inside,outside) static interface service tcp 58080 58080
object network FWD_APP_808
nat (inside,outside) static interface service tcp 808 808
object network FWD_CAM1_554_TCP
nat (inside,outside) static interface service tcp rtsp rtsp
object network FWD_CAM2_21_TCP
nat (inside,outside) static interface service tcp ftp ftp
object network FWD_CAM2_23_TCP
nat (inside,outside) static interface service tcp telnet telnet
object network FWD_CAM1_554_UDP
nat (inside,outside) static interface service udp 554 554
object network FWD_CAM1_2000_TCP
nat (inside,outside) static interface service tcp 2000 2000
object network FWD_CAM1_2000_UDP
nat (inside,outside) static interface service udp 2000 2000
object network FWD_CAM2_21_UDP
nat (inside,outside) static interface service udp 21 21
access-group outside_access_in in interface outside
route outside 0.0.0.0 0.0.0.0 145.116.32.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
aaa-server xxx_LDAP protocol ldap
aaa-server xxx_LDAP (inside) host 10.56.12.1
timeout 60
ldap-base-dn DC=xxxx,DC=local
ldap-scope subtree
ldap-naming-attribute sAMAccountName
ldap-login-password *****
ldap-login-dn xxx_LDAP@xxx.local
server-type microsoft
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
aaa authentication telnet console LOCAL
http server enable 444
http 0.0.0.0 0.0.0.0 inside
http xx255.255.255.255 outside
http xx255.255.255.255 outside
http 10.56.12.0 255.255.255.0 inside
no snmp-server location
no snmp-server contact
service sw-reset-button
crypto ipsec security-association pmtu-aging infinite
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpoint ASDM_TrustPoint0
enrollment terminal
subject-name xxxxxxICT,C=NL,St=Noord-Brabant,L=Exxx
crl configure
crypto ca trustpool policy
crypto ca certificate chain _SmartCallHome_ServerCA
certificate ca 6ecc7aa5a7032009b8cebcf4e952d491
308205ec 308204d4 a0030201 0202106e cc7aa5a7 032009b8 cebcf4e9 52d49130
0d06092a 864886f7 0d010105 05003081 ca310b30 09060355 04061302 55533117
30150603 55040a13 0e566572 69536967 6e2c2049 6e632e31 1f301d06 0355040b
13165665 72695369 676e2054 72757374 204e6574 776f726b 313a3038 06035504
0b133128 63292032 30303620 56657269 5369676e 2c20496e 632e202d 20466f72
20617574 686f7269 7a656420 75736520 6f6e6c79 31453043 06035504 03133c56
65726953 69676e20 436c6173 73203320 5075626c 69632050 72696d61 72792043
65727469 66696361 74696f6e 20417574 686f7269 7479202d 20473530 1e170d31
30303230 38303030 3030305a 170d3230 30323037 32333539 35395a30 81b5310b
30090603 55040613 02555331 17301506 0355040a 130e5665 72695369 676e2c20
496e632e 311f301d 06035504 0b131656 65726953 69676e20 54727573 74204e65
74776f72 6b313b30 39060355 040b1332 5465726d 73206f66 20757365 20617420
68747470 733a2f2f 7777772e 76657269 7369676e 2e636f6d 2f727061 20286329
3130312f 302d0603 55040313 26566572 69536967 6e20436c 61737320 33205365
63757265 20536572 76657220 4341202d 20473330 82012230 0d06092a 864886f7
0d010101 05000382 010f0030 82010a02 82010100 b187841f c20c45f5 bcab2597
a7ada23e 9cbaf6c1 39b88bca c2ac56c6 e5bb658e 444f4dce 6fed094a d4af4e10
9c688b2e 957b899b 13cae234 34c1f35b f3497b62 83488174 d188786c 0253f9bc
7f432657 5833833b 330a17b0 d04e9124 ad867d64 12dc744a 34a11d0a ea961d0b
15fca34b 3bce6388 d0f82d0c 948610ca b69a3dca eb379c00 48358629 5078e845
63cd1941 4ff595ec 7b98d4c4 71b350be 28b38fa0 b9539cf5 ca2c23a9 fd1406e8
18b49ae8 3c6e81fd e4cd3536 b351d369 ec12ba56 6e6f9b57 c58b14e7 0ec79ced
4a546ac9 4dc5bf11 b1ae1c67 81cb4455 33997f24 9b3f5345 7f861af3 3cfa6d7f
81f5b84a d3f58537 1cb5a6d0 09e4187b 384efa0f 02030100 01a38201 df308201
db303406 082b0601 05050701 01042830 26302406 082b0601 05050730 01861868
7474703a 2f2f6f63 73702e76 65726973 69676e2e 636f6d30 12060355 1d130101
ff040830 060101ff 02010030 70060355 1d200469 30673065 060b6086 480186f8
45010717 03305630 2806082b 06010505 07020116 1c687474 70733a2f 2f777777
2e766572 69736967 6e2e636f 6d2f6370 73302a06 082b0601 05050702 02301e1a
1c687474 70733a2f 2f777777 2e766572 69736967 6e2e636f 6d2f7270 61303406
03551d1f 042d302b 3029a027 a0258623 68747470 3a2f2f63 726c2e76 65726973
69676e2e 636f6d2f 70636133 2d67352e 63726c30 0e060355 1d0f0101 ff040403
02010630 6d06082b 06010505 07010c04 61305fa1 5da05b30 59305730 55160969
6d616765 2f676966 3021301f 30070605 2b0e0302 1a04148f e5d31a86 ac8d8e6b
c3cf806a d448182c 7b192e30 25162368 7474703a 2f2f6c6f 676f2e76 65726973
69676e2e 636f6d2f 76736c6f 676f2e67 69663028 0603551d 11042130 1fa41d30
1b311930 17060355 04031310 56657269 5369676e 4d504b49 2d322d36 301d0603
551d0e04 1604140d 445c1653 44c1827e 1d20ab25 f40163d8 be79a530 1f060355
1d230418 30168014 7fd365a7 c2ddecbb f03009f3 4339fa02 af333133 300d0609
2a864886 f70d0101 05050003 82010100 0c8324ef ddc30cd9 589cfe36 b6eb8a80
4bd1a3f7 9df3cc53 ef829ea3 a1e697c1 589d756c e01d1b4c fad1c12d 05c0ea6e
b2227055 d9203340 3307c265 83fa8f43 379bea0e 9a6c70ee f69c803b d937f47a
6decd018 7d494aca 99c71928 a2bed877 24f78526 866d8705 404167d1 273aeddc
481d22cd 0b0b8bbc f4b17bfd b499a8e9 762ae11a 2d876e74 d388dd1e 22c6df16
b62b8214 0a945cf2 50ecafce ff62370d ad65d306 4153ed02 14c8b558 28a1ace0
5becb37f 954afb03 c8ad26db e6667812 4ad99f42 fbe198e6 42839b8f 8f6724e8
6119b5dd cdb50b26 058ec36e c4c875b8 46cfe218 065ea9ae a8819a47 16de0c28
6c2527b9 deb78458 c61f381e a4c4cb66
quit
crypto ca certificate chain ASDM_TrustPoint0
certificate 230676e5b82c050f95e56aa227367552
308205e0 308204c8 a0030201 02021023 0676e5b8 2c050f95 e56aa227 36755230
0d06092a 864886f7 0d01010b 05003042 310b3009 06035504 06130255 53311630
14060355 040a130d 47656f54 72757374 20496e63 2e311b30 19060355 04031312
52617069 6453534c 20534841 32353620 4341301e 170d3136 31313038 30303030
30305a17 0d313831 31303832 33353935 395a301c 311a3018 06035504 030c1174
75652e6a 6176656c 696e6963 742e6e6c 30820122 300d0609 2a864886 f70d0101
01050003 82010f00 3082010a 02820101 00acbc46 274407af d6ffba8e db8a0b42
a44a2cef a4e726e3 fc98e676 891f9ffe 75b6c28f edf55c66 7c493dea 6f985d91
aaf37405 9a8a457b 6f4b2b08 e28aa3f0 d8e7ee94 40cea244 b140ed56 9a9433df
cd99e668 6801a2e0 28064660 dd72054d fcc479ef 54ab8c58 6b23626d ff0f0b23
8c25d0ad 426ca9f6 78f45c9f 978aa9a8 f02d7bbb dfe17735 507266f5 1814ec75
8bbe55b5 62126a47 7679f206 61e05f63 f2ac76b3 36204f19 e2e63cc2 e3358a4f
6c7f4cbc 8564fba6 8f21b583 f86f8278 a9bf0708 b2be9b26 60ee8284 3ab2921e
6c0fa343 46d96acf a348338c f293298c 4a62094b bbfd7c39 e96f100d d5ab70ce
3d7e2333 9779b201 09949f66 2c723299 3d020301 0001a382 02f63082 02f2301c
0603551d 11041530 13821174 75652e6a 6176656c 696e6963 742e6e6c 30090603
551d1304 02300030 2b060355 1d1f0424 30223020 a01ea01c 861a6874 74703a2f
2f67702e 73796d63 622e636f 6d2f6770 2e63726c 306f0603 551d2004 68306630
64060667 810c0102 01305a30 2a06082b 06010505 07020116 1e687474 70733a2f
2f777777 2e726170 69647373 6c2e636f 6d2f6c65 67616c30 2c06082b 06010505
07020230 200c1e68 74747073 3a2f2f77 77772e72 61706964 73736c2e 636f6d2f
6c656761 6c301f06 03551d23 04183016 801497c2 27509ec2 c9ec0c88 32c87cad
e2a6014f da6f300e 0603551d 0f0101ff 04040302 05a0301d 0603551d 25041630
1406082b 06010505 07030106 082b0601 05050703 02305706 082b0601 05050701
01044b30 49301f06 082b0601 05050730 01861368 7474703a 2f2f6770 2e73796d
63642e63 6f6d3026 06082b06 01050507 3002861a 68747470 3a2f2f67 702e7379
6d63622e 636f6d2f 67702e63 72743082 017e060a 2b060104 01d67902 04020482
016e0482 016a0168 007600dd eb1d2b7a 0d4fa620 8b81ad81 68707e2e 8e9d01d5
5c888d3d 11c4cdb6 ecbecc00 00015844 89c25900 00040300 47304502 2023fa30
cba4bfd6 d57684a2 9178d7ed 7f62df9e dbbd24ba 013de672 c4939c7f 66022100
d8c96c2a cd13aa11 baa1d57d ea24d101 39349583 0ea05ab7 19c91d0e 3362d854
00750068 f698f81f 6482be3a 8ceeb928 1d4cfc71 515d6793 d444d10a 67acbb4f
4ffbc400 00015844 89c27f00 00040300 46304402 20761998 2b95e3fd da1222df
058ef1a0 5d644cd0 b3d604a9 db822a3a b465a102 b102201a cb42e56b a1bac440
e4700667 f4d188ab b263584a c20e5c2e 7b246435 3d7db700 7700ee4b bdb775ce
60bae142 691fabe1 9e66a30f 7e5fb072 d88300c4 7b897aa8 fdcb0000 01584489
c2a70000 04030048 30460221 00e68a07 2c7644b2 79fdfacc 28c7978c e89ca948
a57ebe10 a0ba4853 b0227869 a1022100 c21cb691 7aa7e52e 82f74a4d 86067398
2a9d6283 53a65716 d0ca1d3d bbd217b5 300d0609 2a864886 f70d0101 0b050003
82010100 0af4a339 283bd53a 35ac57f7 5305caf7 83c89962 c08c7899 a4138ee5
07383791 199ccda8 2cfb9613 defcf9a4 cdc6a9b1 ed907862 58eca5f7 b9dc1905
59b8b0a4 e69e4e48 420c25b8 73cd7979 4debdf22 d30a6ddd 209bc851 c4100703
39ade600 034f113d a1473933 04f6884e c293e31a 5bb0e2b5 42822ac4 ad1a47ff
aeadff16 53c9b5c5 5e305c92 267c0565 54f62790 d9f423a9 65524564 f412e1c3
42aa45a0 df957371 26ad9f58 65c50fdc 903e6311 0bcfdcc6 2221b641 2eee3a80
dc175500 10605c89 dbb886df 357bfc7e dadeaff7 3fa28ba2 5c32846a 15345cb3
5b5720d0 a5fef1e2 d9f82335 df1de09c d126b987 9bc21b67 1dc16f1d 286cdace
1cba2d5e
quit
no crypto isakmp nat-traversal
telnet timeout 5
no ssh stricthostkeycheck
ssh 212.61.72.251 255.255.255.255 outside
ssh 213.10.67.17 255.255.255.255 outside
ssh 0.0.0.0 0.0.0.0 inside
ssh 10.56.12.0 255.255.255.0 inside
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
dhcpd auto_config outside
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server xxxsource outside prefer
ssl cipher default custom "AES256-SHA:AES128-SHA:DES-CBC3-SHA"
ssl cipher tlsv1 custom "AES256-SHA:AES128-SHA:DES-CBC3-SHA"
ssl cipher dtlsv1 custom "AES256-SHA:AES128-SHA:DES-CBC3-SHA"
ssl trust-point ASDM_TrustPoint0 outside
ssl trust-point ASDM_TrustPoint0 inside
webvpn
port 446
enable outside
dtls port 446
anyconnect-essentials
anyconnect image disk0:/anyconnect-win-4.2.01035-k9.pkg 1 regex "Windows NT"
anyconnect image disk0:/anyconnect-macosx-i386-4.2.01035-k9.pkg 2 regex "Intel Mac OS X"
anyconnect enable
tunnel-group-list enable
cache
disable
error-recovery disable
group-policy GroupPolicy_xxx_Anyconnect internal
group-policy GroupPolicy_xxx_Anyconnect attributes
wins-server none
dns-server value 10.56.12.1 8.8.8.8
vpn-tunnel-protocol ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Anyconnect_ACL
default-domain value xxx.local
split-tunnel-all-dns enable
dynamic-access-policy-record DfltAccessPolicy
username xxxx password hkK.yAUeUpkAJ0Hi encrypted privilege 15
tunnel-group xxx_Anyconnect type remote-access
tunnel-group xxx_Anyconnect general-attributes
address-pool xxx_DHCP
authentication-server-group xxx_LDAP
default-group-policy GroupPolicy_xxx_Anyconnect
tunnel-group xxx_Anyconnect webvpn-attributes
group-alias xxx_Anyconnect enable
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect netbios
inspect tftp
inspect ip-options
inspect pptp
inspect icmp
inspect icmp error
!
service-policy global_policy global
prompt hostname context
call-home reporting anonymous
Cryptochecksum:1352e35c237e06123a3a1ddd8e8d4643
: endASKER
Sorry SIM50 if i was unclear.
I want to forward telnet port 23 to a inside device. with ip 10.56.12.45.
I am 100% sure the acl and the nat are correct.
Still the port is not forwarded.
My question. is it blocked somehow? by the firewall? and where can i unblock it?
I want to forward telnet port 23 to a inside device. with ip 10.56.12.45.
I am 100% sure the acl and the nat are correct.
Still the port is not forwarded.
My question. is it blocked somehow? by the firewall? and where can i unblock it?
object network FWD_CAM2_23_TCP
host 10.56.12.45
nat (inside,outside) static interface service tcp telnet telnet
access-list outside_access_in extended permit object-group DM_INLINE_SERVICE_2 object-group DM_INLINE_NETWORK_4 object INSIDE_xxx-xxx-CAM2
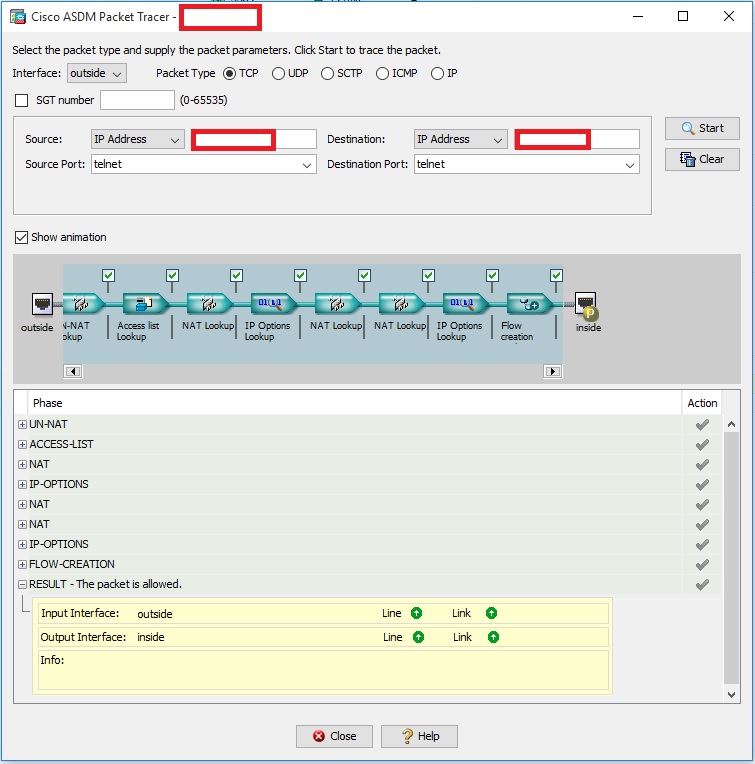
Looks good. Run the packet tracer tool to double check. If it allows through, the ASA is not a problem.
host 10.56.12.45
nat (inside,outside) static interface service tcp telnet telnet
access-list outside_access_in extended permit object-group DM_INLINE_SERVICE_2 object-group DM_INLINE_NETWORK_4 object INSIDE_xxx-xxx-CAM2
Looks good. Run the packet tracer tool to double check. If it allows through, the ASA is not a problem.
It looks like the cisco asa has reserved port 23 for itself or blocked by the service policys.
ASA does block telnet traffic to it's interface with the low security level. This is by design because telnet is unsecure. So I did some testing on my desktop ASA.
1. I configured PAT for telnet.
2. Created ACL and applied to outside interface.
My config:
object network switch_ip
host 192.168.1.2
nat (inside,outside) static interface service tcp telnet telnet
!
access-list outside_in extended permit tcp any object switch_ip eq telnet
access-group outside_in in interface outside
!
Test result:
ciscoasa(config)# sh nat
Auto NAT Policies (Section 2)
1 (inside) to (outside) source static switch_ip interface service tcp telnet telnet
translate_hits = 0, untranslate_hits = 1
ciscoasa(config)# sh xlate
1 in use, 1 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
TCP PAT from inside:192.168.1.2 23-23 to outside:10.128.98.175 23-23
flags sr idle 1:19:21 timeout 0:00:00
ciscoasa(config)# sh access-l
access-list cached ACL log flows: total 0, denied 0 (deny-flow-max 4096)
alert-interval 300
access-list global_mpc; 1 elements; name hash: 0x2e734f01
access-list global_mpc line 1 extended permit ip any any (hitcnt=14576) 0x52c4ba82
access-list outside_in; 1 elements; name hash: 0xc5896c24
access-list outside_in line 1 extended permit tcp any object switch_ip eq telnet (hitcnt=6) 0xd5479019
access-list outside_in line 1 extended permit tcp any host 192.168.1.2 eq telnet (hitcnt=6) 0xd5479019
You can see that it works, my internal IP gets unnated and ACL is matching telnet traffic.
Now when I try to enable telnet on outside interface:
ciscoasa(config)# telnet 0.0.0.0 0.0.0.0 outside
ERROR: Unable to configure service on port 23, on interface 'outside'. This port is currently in use by another feature
ASA is smart enough to recognize that telnet traffic is not really destined to itself even though the destination is its outside interface.
It would work if you would use the global IP. Here is the explanation why:
http://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-next-generation-firewalls/116388-technote-nat-00.html#anc8
http://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-next-generation-firewalls/116388-technote-nat-00.html#anc8
ASKER
I read the article, and i don't quite understand yet.. you mean destination ip the external ASA outsite address?
Yes. Put external (interface) IP as destination in the packet tracker.
ASKER
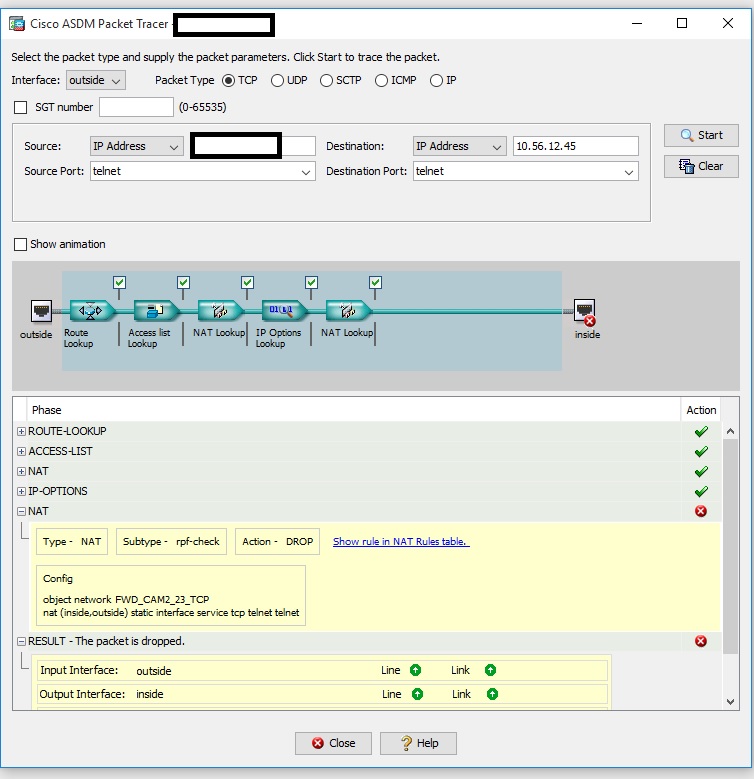
when i do that! see result.
It works but it doesn''t
Customer says he can telnet internally to the device.
any suggestions?
 telnet2.JPG
telnet2.JPG
It works but it doesn''t
Customer says he can telnet internally to the device.
any suggestions?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
In you config you are doing static interface PAT for telnet to WD_CAM1_554_TCP.