Use packet tracer to verify anyconnect VPN
Hi team,
Kindly confirm how one could use packet tracer to verify policies and configuration for Anyconnect.
To be more precise, while using CLI, kindly confirm the source interface that should be selected for VPN pool source IP in packet tracer
Kindly confirm how one could use packet tracer to verify policies and configuration for Anyconnect.
To be more precise, while using CLI, kindly confirm the source interface that should be selected for VPN pool source IP in packet tracer
ASKER
Hi Pete,
Was waiting for your inputs.
Kindly confirm thr source interface to be selected when we define a VPN pool for anyconnect users.
Here the testing needs to be done with the source ip from.the VPN pool
Was waiting for your inputs.
Kindly confirm thr source interface to be selected when we define a VPN pool for anyconnect users.
Here the testing needs to be done with the source ip from.the VPN pool
Hi Ian,
Treat it just as you would any external ip so remote clients you check input on the outside (WAN) interface and for outbound checks form servers etc input is in the inside (LAN) interface.
Pete
Treat it just as you would any external ip so remote clients you check input on the outside (WAN) interface and for outbound checks form servers etc input is in the inside (LAN) interface.
Pete
ASKER
Hi Pete,
Let me test this tomorrow.
I tried the input interface as outside but it was showing a route lookup error.
Will post the output accordingly.
Let me test this tomorrow.
I tried the input interface as outside but it was showing a route lookup error.
Will post the output accordingly.
ASKER
Hi Pete,
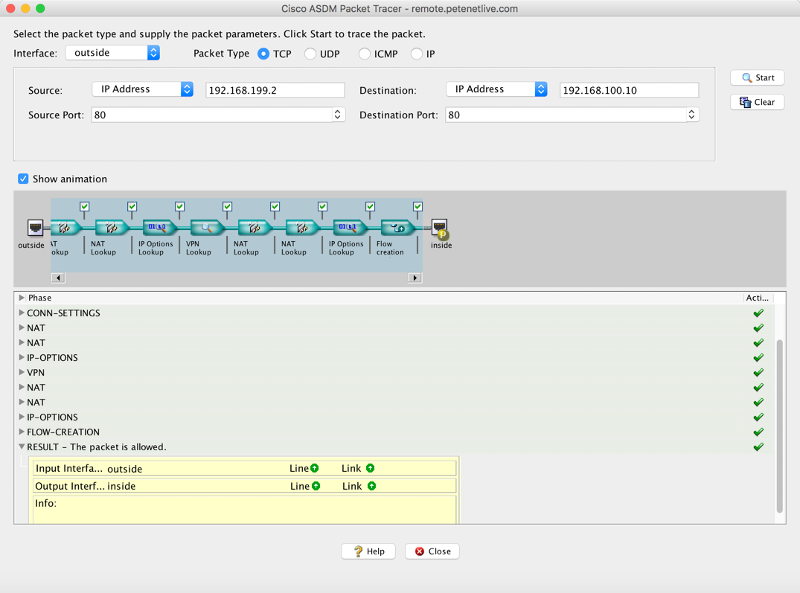
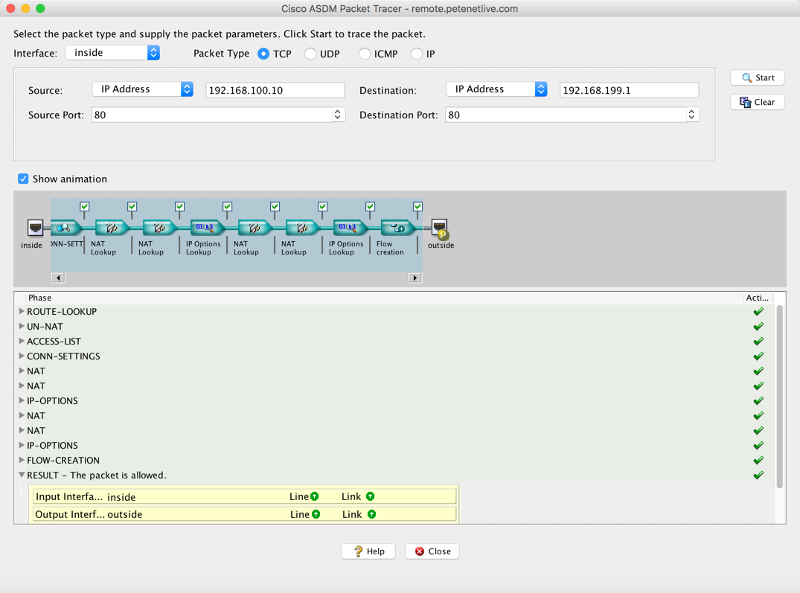
PFA: The output of packet-tracer.
It works with input as inside.
The doubt out here is that the VPN access list wherein we permit the VPN pool access to the internal resources does not reflect anywhere.
Ethernet adapter Local Area Connection 2:
Connection-specific DNS Suffix . :*com
IPv4 Address. . . . . . . . . . . : 172.21.7.109
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
packet-tracert.txt
PFA: The output of packet-tracer.
It works with input as inside.
The doubt out here is that the VPN access list wherein we permit the VPN pool access to the internal resources does not reflect anywhere.
Ethernet adapter Local Area Connection 2:
Connection-specific DNS Suffix . :*com
IPv4 Address. . . . . . . . . . . : 172.21.7.109
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
packet-tracert.txt
Dos this access-list have a deny in it?
access-group outside_access_in in interface Outside
access-group outside_access_in in interface Outside
ASKER
Hi,
Yes there is an access-list configured on the outside interface.
Just help me understanding a logic.
The remote user when obtains an IP from VPN pool, ideally hits the firewall on the outside interface.
Here even though packet tracer indicates there is a drop in the traffic flow, users are able to access the resources.
Kindly confirm if I am missing out something here.
Yes there is an access-list configured on the outside interface.
Just help me understanding a logic.
The remote user when obtains an IP from VPN pool, ideally hits the firewall on the outside interface.
Here even though packet tracer indicates there is a drop in the traffic flow, users are able to access the resources.
Kindly confirm if I am missing out something here.
ASKER
Hi Team,
Kindly help.
Kindly help.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Exactly what I needed....tx a lot Pete....appreciate it..
Packet tracer is a great tool, but it does have a problem with remove VPN sessions, the you are testing connections DONT use the IP that a remote client is already using - or it will fail.
TO use packet tracer I use a (free) IP address from the outside 'pool' and test it coming IN thought the outside interface going to an inside client like so
packet-tracer input outside tcp host 192.168.100.1 www host 10.10.1.1 www
Where 192 is the remote machine and 10.10 is the inside range.