netsh advfirewall - Update (add to existing IP Addresses)
Hello All;
I am going to use the following script to add to the Windows Firewall, a list of IP Addresses.
2 Questions.
First
How do you UPDATE an existing rule?
The above script will update the existing RULE, however. It will overwrite all the IP Entries.
I need to add to that list.
Second
I test the script to make sure it would work, and I added my other computer to it.
Well, it works and now my other computer cannot access this computer.
I deleted the entry, and still cannot access this computer.
I cut off the Windows Firewall for Domain, and the computer was then able to access this system.
So, HOW can I remove an entry, if a person contacts me, that is an innocent bystander, that was not a part of the hack attempt, and needs the IP removed. I would HATE to have to reboot the server every time I get a request to remove an IP Address.
(I believe the mistake I made, was "Deleting" the rule, and I should have "Disabled" the rules.
That is what I get from reading the Technet.Microsoft.com site.
That only Disabled Rules are not monitored as Active.
So, it seems the ones I deleted, and still showing as Active)
I checked in the Registry, and there is nothing there.
So, I am unsure where these are located at.
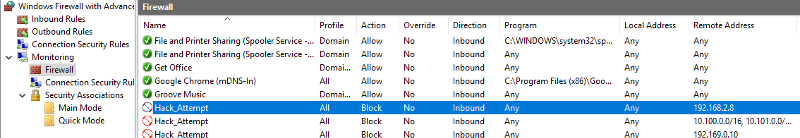
Inbound (ONE rule with 2 entries)
 Firewall (THREE Hack Attempt Rules) These cannot be removed. There is NO option to remove them.
Firewall (THREE Hack Attempt Rules) These cannot be removed. There is NO option to remove them.
 Wayne
Wayne
I am going to use the following script to add to the Windows Firewall, a list of IP Addresses.
netsh advfirewall firewall set rule name="IP Block" dir=in interface=any action=block new remoteip=<IP_Address>/32,<IP_Address>/32,<IP_Address>/32,<IP_Address>/322 Questions.
First
How do you UPDATE an existing rule?
The above script will update the existing RULE, however. It will overwrite all the IP Entries.
I need to add to that list.
Second
I test the script to make sure it would work, and I added my other computer to it.
Well, it works and now my other computer cannot access this computer.
I deleted the entry, and still cannot access this computer.
I cut off the Windows Firewall for Domain, and the computer was then able to access this system.
So, HOW can I remove an entry, if a person contacts me, that is an innocent bystander, that was not a part of the hack attempt, and needs the IP removed. I would HATE to have to reboot the server every time I get a request to remove an IP Address.
(I believe the mistake I made, was "Deleting" the rule, and I should have "Disabled" the rules.
That is what I get from reading the Technet.Microsoft.com site.
That only Disabled Rules are not monitored as Active.
So, it seems the ones I deleted, and still showing as Active)
I checked in the Registry, and there is nothing there.
So, I am unsure where these are located at.
Inbound (ONE rule with 2 entries)
 Firewall (THREE Hack Attempt Rules) These cannot be removed. There is NO option to remove them.
Firewall (THREE Hack Attempt Rules) These cannot be removed. There is NO option to remove them.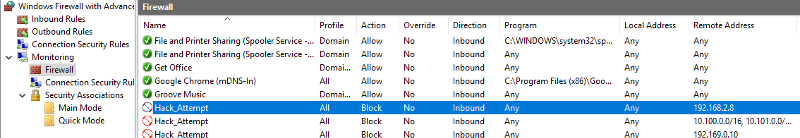 Wayne
Wayne
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I had to enable all the walls by hand, in order for this to work.
>> NetSh Advfirewall set allprofiles state on
But now, In the Monitoring section, it is showing that the Firewall is OFF, even though it is on. ??
Confused.
>> NetSh Advfirewall set allprofiles state on
But now, In the Monitoring section, it is showing that the Firewall is OFF, even though it is on. ??
Confused.
That does not stop the firewall service. That just sets every profile to disabled (but the service is still running)
As to the database suggestion, you'd definitely be rolling your own. But something like SQLite would be sufficient. Even a single-field table with one row per IP. Building the IP lost would probably be easier than complex regular expressions to parse the existing rule.
As to the database suggestion, you'd definitely be rolling your own. But something like SQLite would be sufficient. Even a single-field table with one row per IP. Building the IP lost would probably be easier than complex regular expressions to parse the existing rule.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
You can stop and start the actual firewall service by running the following commands from an elevated privileged command prompt:
Additionally, you can achieve your intended result by first querying the existing values of the rule, parsing them, and then appending.
net stop MpsSvcnet start MpsSvcAdditionally, you can achieve your intended result by first querying the existing values of the rule, parsing them, and then appending.
netsh advfirewall firewall show rule name="IP Block"
Even if there was an IP per line, you can write the script o read each line and construct a single rule. Which, depending on how IP addresses get into the text file, may be necessary. And since you tagged this as 2016 I'd strongly recommend rewriting your script in Powershell instead of a batch file. You can still call command line utilities such as netsh, but the logic and flow control would be much cleaner. PowerShell is a modern full scripting language. Batch files were old and outdated in the 90s (when vbscript supplanted them for most windows sysadmins) and are downright decrepit now.
ASKER
@Giovanni
How do you APPEND to the existing IPs?
@Cliff
I tried to find some PowerShell information, but could not find exactly what I needed.
If you would now, please provide.
How do you APPEND to the existing IPs?
@Cliff
I tried to find some PowerShell information, but could not find exactly what I needed.
If you would now, please provide.
ASKER
OK. I found this script that works pretty good.
But, since I am initially going to be adding in (over the course of time) 1,000's of IPs.
I would need to read from a file.
So, that is going to be the next step.
Would be cool to have something that would get the existing IPs, then load the additional IPs to that list, and then re-insert them.
But, since I am initially going to be adding in (over the course of time) 1,000's of IPs.
I would need to read from a file.
So, that is going to be the next step.
Would be cool to have something that would get the existing IPs, then load the additional IPs to that list, and then re-insert them.
$name = Get-NetFirewallRule -DisplayName "*Hack_Attempt*"
$ips = @("1.1.1.1","2.2.2.2")
foreach($r in $name)
{
Set-NetFirewallRule -DisplayName $r.DisplayName -RemoteAddress $ips
}
Which is why I suggested a database instead of a flat text file. Any SQL variant would make searching, happening, deleting, easier as it can be done per record without rebuilding a whole text file if an address in the middle needs to be removed. And there are database APIs for almost every scripting language out there so integration is easier.
ASKER
How would I attach the powershell to a database?
That depends on the database. They'll have documentation and APIs.
ASKER
Either SQL Server or Access.
Could you at least provide a link to the API and Database information so I can have a look at it?
That would be great!
Could you at least provide a link to the API and Database information so I can have a look at it?
That would be great!
ASKER
I found this, which looks promising.
I guess I will learn a new language... So to speak.
https://www.sqlshack.com/connecting-powershell-to-sql-server/
I guess I will learn a new language... So to speak.
https://www.sqlshack.com/connecting-powershell-to-sql-server/
ASKER
Thanks for the information on the netsh not being able to update current records.
That gave me the idea to hunt for something else to work with.
Have a good one.
Wayne
That gave me the idea to hunt for something else to work with.
Have a good one.
Wayne
ASKER
Could you elaborate a little more on the database?
2)
I used this command to stop
NetSh Advfirewall set allprofiles state off
OK.
I then used this command to start
NetSh Advfirewall set allprofiles state on
..The following command was not found: Advfirewall set allrprofiles state on.