Questions on keyfiles and constant use of TrueCrypt volumnes
We have a user who heavily depends on Truecrypt (she uses the last known version prior the site leaving their users). The size of the volumes range from 360gb to 1 tb and have been using them since 2012 with no glitch whatsoever. She changes the volumes password successfully every year.
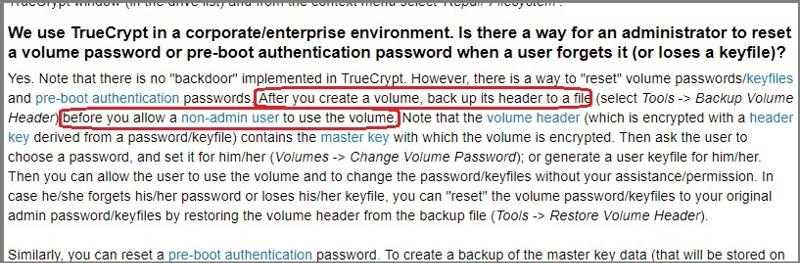
Yesterday, a colleague told her that she has to have the keyfiles of each volume and even more, that right after creating all her volumes, she should have backed up those keyfiles - she has never done this. We have search on this topic and effectively it does says it (see pix below).
Based on the above, 2 questions:
1. Is there any considerations or maintenance she should consider for her TC volumes?
(this is because the user is constantly using the TC volumes, sometimes having them open for
days even is she hibernate her computer, the TC volumes are open)
2. Since she never backed the header or keyfiles when creating TC, may there be some problem?
Also should we do regarding this?
Thank you very much in advance.
Yesterday, a colleague told her that she has to have the keyfiles of each volume and even more, that right after creating all her volumes, she should have backed up those keyfiles - she has never done this. We have search on this topic and effectively it does says it (see pix below).
Based on the above, 2 questions:
1. Is there any considerations or maintenance she should consider for her TC volumes?
(this is because the user is constantly using the TC volumes, sometimes having them open for
days even is she hibernate her computer, the TC volumes are open)
2. Since she never backed the header or keyfiles when creating TC, may there be some problem?
Also should we do regarding this?
Thank you very much in advance.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
No difference or disadvantage, no. TC advises you to do it at once, because corruption or other disasters may happen at any time. But it hasn't happened, luckily.
ASKER
Thanx!
Lastly, the part of the question on "any considerations or maintenance the user should consider for her TC volumes?"
(due to the constantly use of the TC volumes during these years, sometimes having the TC volumes open for days even when hibernating the computers)
Any maintenance recommendation for this type of use of TC volumes?
Lastly, the part of the question on "any considerations or maintenance the user should consider for her TC volumes?"
(due to the constantly use of the TC volumes during these years, sometimes having the TC volumes open for days even when hibernating the computers)
Any maintenance recommendation for this type of use of TC volumes?
No. As you see, it just works and it's ok to use it like this. The usual backups should be done, anyway.
ASKER
I meant more like tools for checking the volume, or defrag, etc. on the volume itself (based on the constant use of these TC volumes, I assume that there has been some times that the user has had her computer locked, restarted and turned off erroneously - so maybe some data loss etc.)
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Ok
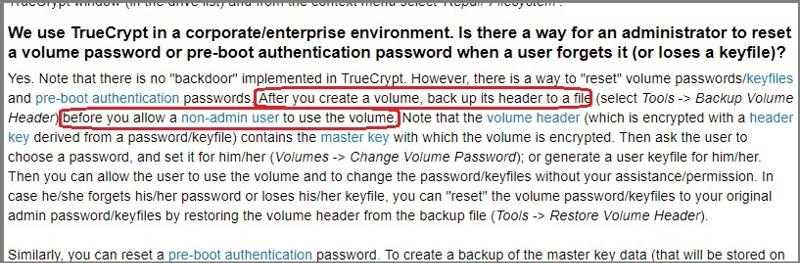
ASKER
Where it says "...before you allow a non-admin user to access the volume", that is only referencing a "first time" TC creation? In other words, when we backup now both Keyfile and volume header, there is no difference or disadvantage against backing them up at the creation time?