Event viewer not showing Security (logging) events.
Hello,
We have login audits enabled through Group Policy, however, when we go to Event Viewer>Windows Logs>Security we do not see any logon/logoff events. Is there anything we are missing? We used to see them, we do not know what was changed. We have Windows Server 2012
Thank you in advance.
We have login audits enabled through Group Policy, however, when we go to Event Viewer>Windows Logs>Security we do not see any logon/logoff events. Is there anything we are missing? We used to see them, we do not know what was changed. We have Windows Server 2012
Thank you in advance.
ASKER
Yes, that event ID. I followed these instructions to enabled it but everything seemed fine already:
https://www.lepide.com/blog/audit-successful-logon-logoff-and-failed-logons-in-activedirectory/
https://www.lepide.com/blog/audit-successful-logon-logoff-and-failed-logons-in-activedirectory/
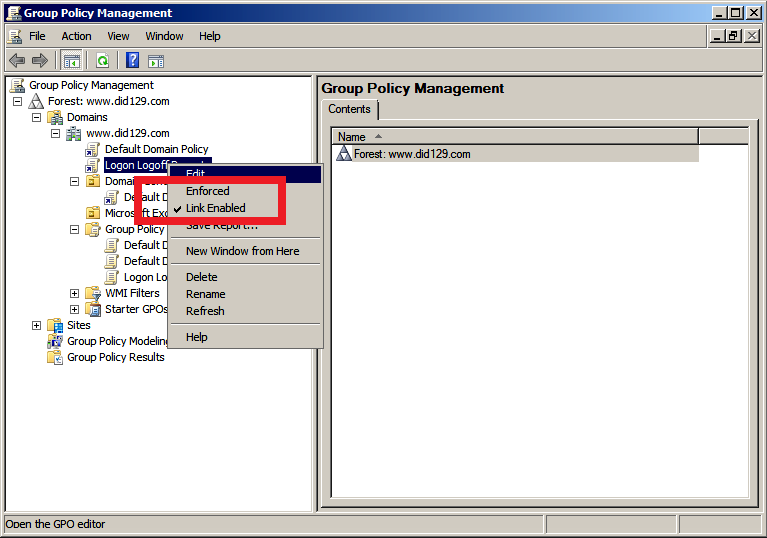
Having quickly scanned the link you gave me I don't see any part where it tells you to enforce the GPO. Can you right click on the policy you created and ensure that "link enabled" and "enforced" is checked?
Open up a command prompt then run GPUPDATE /FORCE command to apply it immediately and retest.
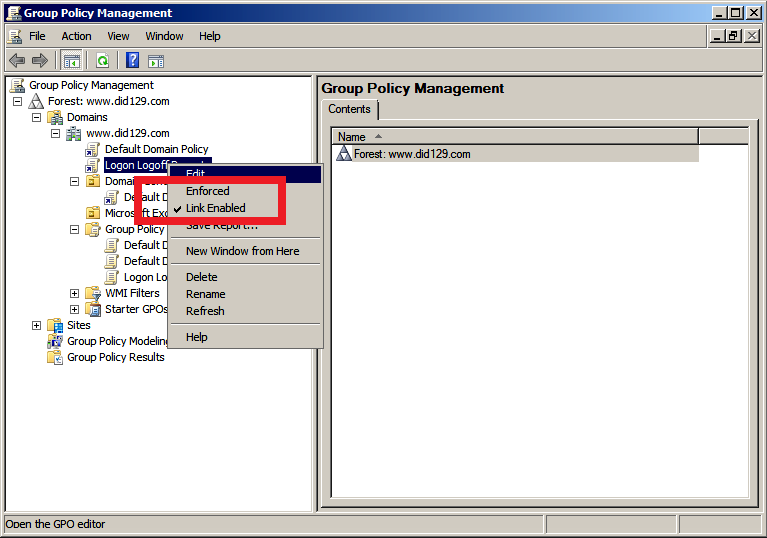
Open up a command prompt then run GPUPDATE /FORCE command to apply it immediately and retest.
ASKER
I enforced it and ran gpupdate /force. I logged out and in and I do not see any new events.
Did you create this GPO for the whole domain or a test group? The reason I asked is because if just a test group then it may not be applying correctly.
In any case, run GPRESULT to see the Resultant Set of Policy to see if the GPO you created is active.
https://www.404techsupport.com/2010/05/11/rsop-and-gpresult-must-know-tools-when-using-group-policy/
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/gpresult
In any case, run GPRESULT to see the Resultant Set of Policy to see if the GPO you created is active.
https://www.404techsupport.com/2010/05/11/rsop-and-gpresult-must-know-tools-when-using-group-policy/
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/gpresult
ASKER
It is configured for the whole domain as far as I know (Display links in this location has the domain name selected.) However, I ran RSOP and GPRESULT and GpResult does not show it under Applied GPOs.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Also how many DC do you have? if more than one then you need to check all DCs for that event log not just one.
Make sure if you have successfully configured Advanced Audit Policy in AD environment.
Run below command with admin right to get all audit settings on your computer:
auditpol /get /category:*
The below articles might be helpful:
Audit policy not registering audits: https://blogs.msdn.microsoft.com/spatdsg/2011/06/06/audit-policy-not-registering-audits/
Getting the Effective Audit Policy in Windows: https://blogs.technet.microsoft.com/askds/2011/03/11/getting-the-effective-audit-policy-in-windows-7-and-2008-r2/
Additionally, you can check AD auditing solution to audit active directory user logon/logoff events.
Run below command with admin right to get all audit settings on your computer:
auditpol /get /category:*
The below articles might be helpful:
Audit policy not registering audits: https://blogs.msdn.microsoft.com/spatdsg/2011/06/06/audit-policy-not-registering-audits/
Getting the Effective Audit Policy in Windows: https://blogs.technet.microsoft.com/askds/2011/03/11/getting-the-effective-audit-policy-in-windows-7-and-2008-r2/
Additionally, you can check AD auditing solution to audit active directory user logon/logoff events.
Just checkout and know How to Get User Logon Session Times from the Event Log
https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4802
https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4800
https://www.eventtracker.com/tech-articles/account-logon-and-logonlogoff/
https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4802
https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4800
https://www.eventtracker.com/tech-articles/account-logon-and-logonlogoff/
ASKER
This command helped me (auditpol /get /category:* ) because everything seemed configured and the results reported "not auditing." Somehow it was selecting whatever was under Advanced Audit Policy and there was nothing configured so I just enabled the logon/log off and ran gpupdate /force and that solved it. Thank you all for your help!
Glad you got it solved and thanks for getting back. Cheers!
Glad it help and you fix this. Please mark the answer and close the thread so other can get help.
"This is a highly valuable event since it documents each and every successful attempt to logon to the local computer regardless of logon type, location of the user or type of account. You can tie this event to logoff events 4634 and 4647 using Logon ID."