Class-map with Access-list
R1#sh run
Building configuration...
Current configuration : 1894 bytes
!
! Last configuration change at 01:14:56 CET Thu Jun 28 2018
!
version 15.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R1
!
boot-start-marker
boot-end-marker
!
aqm-register-fnf
!
!
no aaa new-model
clock timezone CET 1 0
mmi polling-interval 60
no mmi auto-configure
no mmi pvc
mmi snmp-timeout 180
!
!
!
!
!
!
!
!
!
!
ip cef
no ipv6 cef
!
multilink bundle-name authenticated
!
!
!
!
!
!
!
!
!
redundancy
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
interface Ethernet0/0
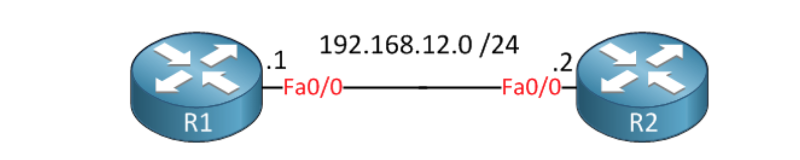
ip address 192.168.12.1 255.255.255.0
load-interval 30
!
interface Ethernet0/1
no ip address
shutdown
!
interface Ethernet0/2
no ip address
shutdown
!
interface Ethernet0/3
no ip address
shutdown
!
interface Ethernet1/0
no ip address
shutdown
!
interface Ethernet1/1
no ip address
shutdown
!
interface Ethernet1/2
no ip address
shutdown
!
interface Ethernet1/3
no ip address
shutdown
!
interface Serial2/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/3
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/3
no ip address
shutdown
serial restart-delay 0
!
ip forward-protocol nd
!
!
no ip http server
no ip http secure-server
!
ip sla auto discovery
ip sla 1
udp-jitter 192.168.12.2 17002 num-packets 20
request-data-size 58
threshold 500
timeout 500
frequency 1
ip sla schedule 1 life forever start-time now
!
!
!
control-plane
!
!
!
!
!
!
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
transport input none
!
!
end
R1#R2#sh run
Building configuration...
Current configuration : 1932 bytes
!
! Last configuration change at 01:21:17 CET Thu Jun 28 2018
!
version 15.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R2
!
boot-start-marker
boot-end-marker
!
aqm-register-fnf
!
!
no aaa new-model
clock timezone CET 1 0
mmi polling-interval 60
no mmi auto-configure
no mmi pvc
mmi snmp-timeout 180
!
!
!
!
!
!
!
!
!
!
ip cef
no ipv6 cef
!
multilink bundle-name authenticated
!
!
!
!
!
!
!
!
!
redundancy
!
!
!
class-map match-all IP_SLA_1
match access-group name IP_SLA_1
!
policy-map TRAFFIC_METER
class IP_SLA_1
!
!
!
!
!
!
!
!
!
!
!
!
!
!
interface Ethernet0/0
ip address 192.168.12.2 255.255.255.0
load-interval 30
service-policy input TRAFFIC_METER
!
interface Ethernet0/1
no ip address
shutdown
!
interface Ethernet0/2
no ip address
shutdown
!
interface Ethernet0/3
no ip address
shutdown
!
interface Ethernet1/0
no ip address
shutdown
!
interface Ethernet1/1
no ip address
shutdown
!
interface Ethernet1/2
no ip address
shutdown
!
interface Ethernet1/3
no ip address
shutdown
!
interface Serial2/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/3
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/3
no ip address
shutdown
serial restart-delay 0
!
ip forward-protocol nd
!
!
no ip http server
no ip http secure-server
!
ip access-list extended IP_SLA_1
permit udp any host 192.168.12.2 eq 17002
!
!
!
!
control-plane
!
!
!
!
!
!
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
transport input none
!
!
end
R2#I was looking at the configuration above that I got from a Blog.
I would like to understand the meaning of these lines in the configuration
class-map match-all IP_SLA_1
match access-group name IP_SLA_1what's the difference with the first match-all and the second match access-group ? is it redundant ?
Thank you
ASKER
there are 2 Matches
one match-all and another match access-group
If I understand the second match " access-group" refers to the traffic permitted through access-list,, what about the 1st match...it states "match-all" , so if it was written : class-map IP_SLA_1 without the match-all keyword, would not that be the same and simpler ?
class-map match-all IP_SLA_1
match access-group name IP_SLA_1
one match-all and another match access-group
If I understand the second match " access-group" refers to the traffic permitted through access-list,, what about the 1st match...it states "match-all" , so if it was written : class-map IP_SLA_1 without the match-all keyword, would not that be the same and simpler ?
class-map match-all IP_SLA_1
match access-group name IP_SLA_1
match-all is keyword in defining class-map's behavior, it is defining what will happen in the case that yoy have two or more statements.
class-map match-all IP_SLA_1
match qos-group 4
match access-group name acl10
other possibility would be:
class-map match-any IP_SLA_1
match qos-group 4
match access-group name acl10
In the case of match-all packet would have to be packet that matches access-list acl10 and to belong to qos-group 4 to be considered as valid member of class.
In the case of match-any packet would have to be packet matches at list one of criteria - access-list acl10 or to belong to qos-group 4 to be considered as valid member of class.
note:
match-any may not be available on newer IOS XE
name of class-map does not have to be the same as the name of access-list (typically it is not)
class-map match-all IP_SLA_1
match qos-group 4
match access-group name acl10
other possibility would be:
class-map match-any IP_SLA_1
match qos-group 4
match access-group name acl10
In the case of match-all packet would have to be packet that matches access-list acl10 and to belong to qos-group 4 to be considered as valid member of class.
In the case of match-any packet would have to be packet matches at list one of criteria - access-list acl10 or to belong to qos-group 4 to be considered as valid member of class.
note:
match-any may not be available on newer IOS XE
name of class-map does not have to be the same as the name of access-list (typically it is not)
ASKER
name of class-map does not have to be the same as the name of access-list (typically it is not)
We have the configuration below, how do you explain it ? class map is a bit confusing to me in this scenario:
ip access-list extended IP_SLA_1
permit udp any host 192.168.12.2 eq 17002
class-map match-all IP_SLA_1
match access-group name IP_SLA_1
!
policy-map TRAFFIC_METER
class IP_SLA_1
interface Ethernet0/0
service-policy input TRAFFIC_METER
just imagine that access list has different name
ip access-list extended IP2port17002
permit udp any host 192.168.12.2 eq 17002
class-map match-all IP_SLA_1
match access-group name IP2port17002
!
policy-map TRAFFIC_METER
class IP_SLA_1
interface Ethernet0/0
service-policy input TRAFFIC_METERASKER
i understand the access-list..
but
class-map match-all IP_SLA_1
does it match all traffic ??
interface Ethernet0/0
service-policy input TRAFFIC_METER
The service policy input TRAFFIC_METER above will let in the traffic permitted by the class map or the access-list ?
but
class-map match-all IP_SLA_1
does it match all traffic ??
interface Ethernet0/0
service-policy input TRAFFIC_METER
The service policy input TRAFFIC_METER above will let in the traffic permitted by the class map or the access-list ?
ASKER
ip access-list extended IP2port17002
permit udp any host 192.168.12.2 eq 17002
class-map match-all IP_SLA_1
match access-group name IP2port17002
!
policy-map TRAFFIC_METER
class IP_SLA_1
interface Ethernet0/0
service-policy input TRAFFIC_METERif you can explain the code above you wrote, what it does , probably that will help to understand the purpose of the code.
does it match all traffic ??It matches to all match statements below class-map (AND statement)
I will try to explain it differently:
create class-map with name IP_SLA_1, that need to satisfy ALL match statements
class-map match-all IP_SLA_1So, this means that some object need to satisfy both criteria to be considered as part of class-map IP_SLA_1.
match green
match apple
If it is green and it is a cherry it is not satisfying all conditions.
Only if it is green AND it is an apple it is satisfying both criteria.
With match-any statement it would be enough that object is green or it is apple.
objects in access list IP2port17002 belong to IP_SLA_1 class-map (since there is only one line it is irrelevant if it is defined with match-all, or match-any (match-all is default)). Here objects are just classified and nothing more...
class-map match-all IP_SLA_1Then in policy-map typically there are actions that supposed to be done on class-map, I will add one line for easier explanation.
match access-group name IP2port17002
policy-map TRAFFIC_METERHere traffic that is matching class IP_SLA_1 would be policed.
class IP_SLA_1
police 12000000 60000 exceed-action policed-dscp-transmit
And
interface Ethernet0/0is simply applying policing in ingress direction.
service-policy input TRAFFIC_METER
ASKER
objects in access list IP2port17002 belong to IP_SLA_1 class-map (since there is only one line it is irrelevant if it is defined with match-all, or match-any (match-all is default)). Here objects are just classified and nothing more...
class-map match-all IP_SLA_1
match access-group name IP2port17002
the access-list is permitting only udp traffic going to host 192.168.12.2 eq 17002
since you said the access-list belongs to class-map, then is the class-map match all, is to match udp traffic going to host 192.168.12.2 eq 17002 ?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you !
You're welcome.
the first line is defining class-map named IP_SLA_1
second line is matching acess-list name IP_SLA_1
ip access-list extended IP_SLA_1
permit udp any host 192.168.12.2 eq 17002