Access List Inbound
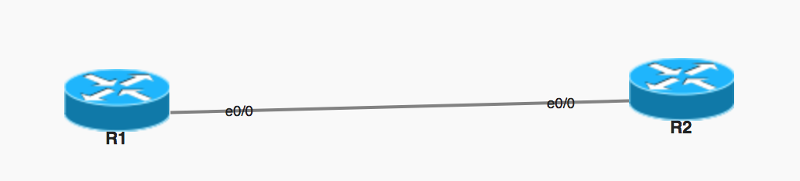
in the topology above , I have 2 routers with 2 loopbacks.
on R2 I configured an access list to permit only 192.168.12.0 which is the link between R1 and R2, for some reason I cannot ping loopback 1.1.1.1 of R1 which makes sense, but I can ping from R1 to loopback of R2. I thought both loopbacks cannot be ping because of the access list:
configuration below:
R1:
R1#sh run
Building configuration...
Current configuration : 1792 bytes
!
! Last configuration change at 16:05:15 CET Sat Aug 18 2018
!
version 15.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R1
!
boot-start-marker
boot-end-marker
!
aqm-register-fnf
!
!
no aaa new-model
clock timezone CET 1 0
mmi polling-interval 60
no mmi auto-configure
no mmi pvc
mmi snmp-timeout 180
!
!
!
!
!
!
!
!
!
!
ip cef
no ipv6 cef
!
multilink bundle-name authenticated
!
!
!
!
!
!
!
!
!
redundancy
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
interface Loopback0
ip address 1.1.1.1 255.255.255.255
!
interface Ethernet0/0
ip address 192.168.12.1 255.255.255.0
!
interface Ethernet0/1
no ip address
shutdown
!
interface Ethernet0/2
no ip address
shutdown
!
interface Ethernet0/3
no ip address
shutdown
!
interface Ethernet1/0
no ip address
shutdown
!
interface Ethernet1/1
no ip address
shutdown
!
interface Ethernet1/2
no ip address
shutdown
!
interface Ethernet1/3
no ip address
shutdown
!
interface Serial2/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/3
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/3
no ip address
shutdown
serial restart-delay 0
!
ip forward-protocol nd
!
!
no ip http server
no ip http secure-server
ip route 2.2.2.0 255.255.255.0 192.168.12.2
!
!
!
!
control-plane
!
!
!
!
!
!
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
transport input none
!
!
end
R1#R2#show run
Building configuration...
Current configuration : 1858 bytes
!
! Last configuration change at 16:06:04 CET Sat Aug 18 2018
!
version 15.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R2
!
boot-start-marker
boot-end-marker
!
aqm-register-fnf
!
!
no aaa new-model
clock timezone CET 1 0
mmi polling-interval 60
no mmi auto-configure
no mmi pvc
mmi snmp-timeout 180
!
!
!
!
!
!
!
!
!
!
ip cef
no ipv6 cef
!
multilink bundle-name authenticated
!
!
!
!
!
!
!
!
!
redundancy
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
interface Loopback0
ip address 2.2.2.2 255.255.255.255
!
interface Ethernet0/0
ip address 192.168.12.2 255.255.255.0
ip access-group 1 in
!
interface Ethernet0/1
no ip address
shutdown
!
interface Ethernet0/2
no ip address
shutdown
!
interface Ethernet0/3
no ip address
shutdown
!
interface Ethernet1/0
no ip address
shutdown
!
interface Ethernet1/1
no ip address
shutdown
!
interface Ethernet1/2
no ip address
shutdown
!
interface Ethernet1/3
no ip address
shutdown
!
interface Serial2/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial2/3
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/0
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial3/3
no ip address
shutdown
serial restart-delay 0
!
ip forward-protocol nd
!
!
no ip http server
no ip http secure-server
ip route 1.1.1.0 255.255.255.0 192.168.12.1
!
!
!
access-list 1 permit 192.168.12.0 0.0.0.255
!
control-plane
!
!
!
!
!
!
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
transport input none
!
!
end
R2#ASKER
When pinging from R2 to R1 loopback 1.1.1.1 the packets by default should be sourced from 192.168.12.2
When pinging from R1 to R2 loopback 2.2.2.2 the packets by default should be sourced from 192.168.12.1
how come from R1 I can ping 2.2.2.2 as well as 192.168.12.2 ? but from R2 I can ping only 192.168.12.1 but not 1.1.1.1
the ACL on R2 should also drop the ping packets from R1 going to 2.2.2.2
When pinging from R1 to R2 loopback 2.2.2.2 the packets by default should be sourced from 192.168.12.1
how come from R1 I can ping 2.2.2.2 as well as 192.168.12.2 ? but from R2 I can ping only 192.168.12.1 but not 1.1.1.1
the ACL on R2 should also drop the ping packets from R1 going to 2.2.2.2
Please, think about it:
Which IP address is source of icmp reply?
It is the loopback IP address and you are filtering traffic in IN direction on one interface.
icmp echo request - if source is not specificaly defined source IP address is interface address
case 1:
icmp echo request is sent from interface --> then it checked against ACL - source interface is matching permit statement in ACL traffic is forwarded --> return traffic, icmp echo, is not inspected
case 2:
icmp echo request is sent from interface --> traffic is not inspected in OUT direction --> icmp echo request reaches loopback interface --> loopback interface is source of echo reply --> echo reply is not inspected on this router, however icmp reply will be inspected in IN direction when it reaches router rhat sent echo request, but now source address is not matching permit statement since source IP address is loopback IP address and destination IP address is 192.168.12.2
Since source IP adress is not from 192.168.12.0/24 range traffic will be dropped.
Which IP address is source of icmp reply?
It is the loopback IP address and you are filtering traffic in IN direction on one interface.
icmp echo request - if source is not specificaly defined source IP address is interface address
case 1:
icmp echo request is sent from interface --> then it checked against ACL - source interface is matching permit statement in ACL traffic is forwarded --> return traffic, icmp echo, is not inspected
case 2:
icmp echo request is sent from interface --> traffic is not inspected in OUT direction --> icmp echo request reaches loopback interface --> loopback interface is source of echo reply --> echo reply is not inspected on this router, however icmp reply will be inspected in IN direction when it reaches router rhat sent echo request, but now source address is not matching permit statement since source IP address is loopback IP address and destination IP address is 192.168.12.2
Since source IP adress is not from 192.168.12.0/24 range traffic will be dropped.
ASKER
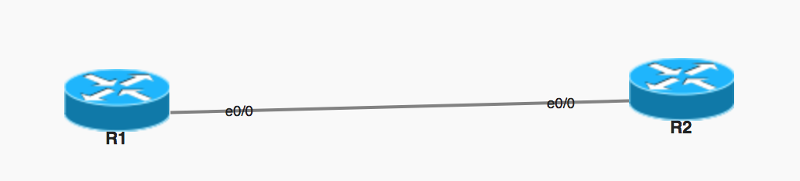 Ok in the screenshot above, the ACL is applied on R2 interface e0/0 inbound
Ok in the screenshot above, the ACL is applied on R2 interface e0/0 inboundI agree when you said , pinging from R2 to loopback of R1 , it will reach R1 Loopback but the return traffic will be dropped because of ACL that is permitting only 192.168.12.0/24
Now , let's forgot about R2
let's focus just on R1, when the ping is sourced from R1 loopback to R2, the R1 loopback IP is 1.1.1.1 , so it is different from 192.168.12.0/24, when it gets to interface e0/0 of R2 the ACL should drop it, because ACL is not permitted anything other than 192.168.12.0/24..
However in my case I am able to ping from R1 with the source of 1.1.1.1 to R2
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I believe you are correct..this time, it did not ping from source 1.1.1.1
R1#ping 2.2.2.2 source 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 2.2.2.2, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
U.U.U
Success rate is 0 percent (0/5)
R1#ASKER
Thank you
You're welcome.
When you are pinging in direction of interface with ACL assigned source IP address will be address of closest interface (192.168.12.1 which is permitted by ACL 1).
When you are pining in opposite direction - return traffic will be sourced from 1.1.1.1 with is not permitted (it will be dropped by implicit deny on the end of ACL 1).
To make ping functional to loopback1 permit 1.1.1.1 in ACL1.