Disabling VTP Pruning in a vtp domain
I am seeking advice regarding disabling VTP pruning within a collection of Cisco switches.
The background. I recently introduced a new Cisco 9300 switch into the environment and it became a VTP client in the VTP domain. We have about 25 VLANs configured in the environment. Everything was working fine on the 9300 except that hosts on a particular vlan (14) were not able to communicate.
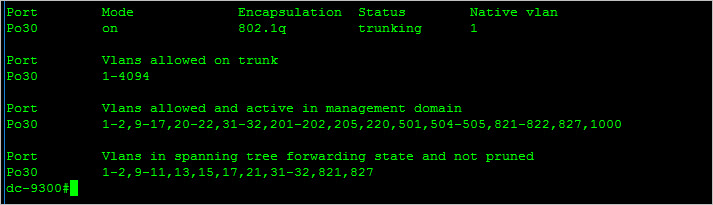
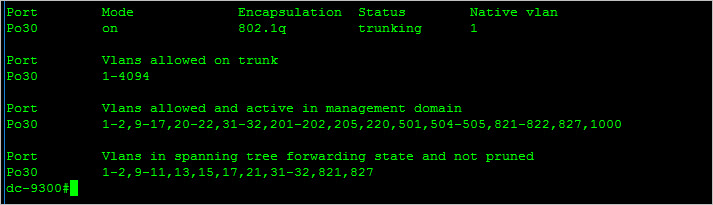
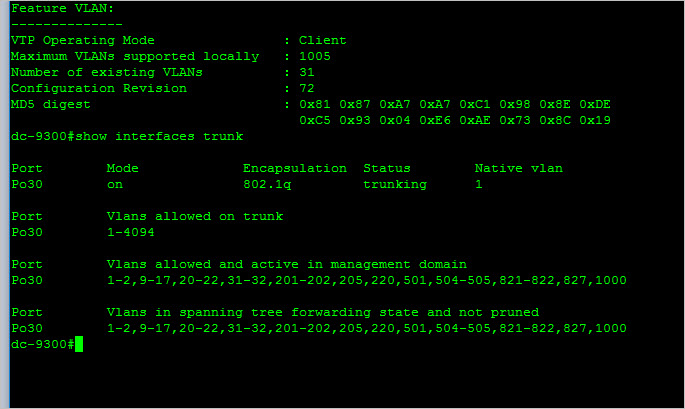
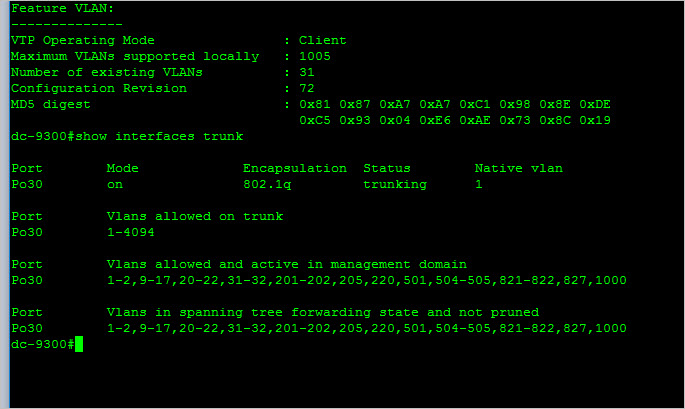
The picture below shows the output of "show interfaces trunk". There is one port channel (Po30) to our core switch. Vlan 14 is not listed under "Vlans in spanning tree forwarding state and not pruned" and that is believed to be the cause of me not being able to communicate with hosts on this switch assigned to that vlan. I was advised to disable pruning by a Cisco technician and that should bring things into alignment.
My question is, is there any downside to doing this? If I disable pruning, will the list in "Vlans allowed and active..." and "Vlans in spanning tree forwarding..." be the same? I am also curious if there are any "gotchas" with disabling VTP pruning. I am not understanding why an active vlan is pruned on this switch.
The background. I recently introduced a new Cisco 9300 switch into the environment and it became a VTP client in the VTP domain. We have about 25 VLANs configured in the environment. Everything was working fine on the 9300 except that hosts on a particular vlan (14) were not able to communicate.
The picture below shows the output of "show interfaces trunk". There is one port channel (Po30) to our core switch. Vlan 14 is not listed under "Vlans in spanning tree forwarding state and not pruned" and that is believed to be the cause of me not being able to communicate with hosts on this switch assigned to that vlan. I was advised to disable pruning by a Cisco technician and that should bring things into alignment.
My question is, is there any downside to doing this? If I disable pruning, will the list in "Vlans allowed and active..." and "Vlans in spanning tree forwarding..." be the same? I am also curious if there are any "gotchas" with disabling VTP pruning. I am not understanding why an active vlan is pruned on this switch.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Can you try changing it to transparent and then back to client? what is the output of
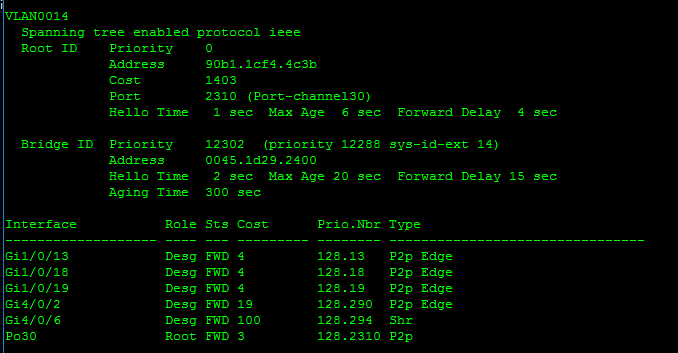
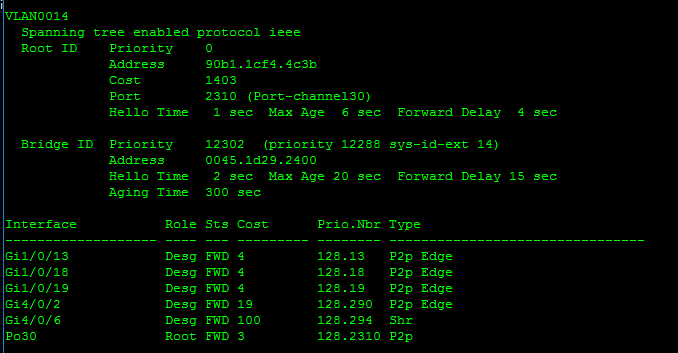
sh spanning-tree vlan 14ASKER
The output of sh spanning-tree vlan 14 while still in client mode is:
I have not tried changing to transparent and back not knowing what the effect would be on hosts connected on the switch. I wouldn't want something weird like hosts all of a sudden not being able to get anywhere because ALL vlans were pruned. I get skittish around vtp. :)
I have not tried changing to transparent and back not knowing what the effect would be on hosts connected on the switch. I wouldn't want something weird like hosts all of a sudden not being able to get anywhere because ALL vlans were pruned. I get skittish around vtp. :)
Changing to transparent shouldn't affect the passing of VTP traffic. The actual switch will just not participate in the VTP updates. It will forward them though.
ASKER
Ok, so here is what happened.
I verified that the Vlan was still pruned on the switch.
I logged into the switch designated as the VTP server
#conf t
#no vtp pruning
I verified it was disabled and I went to the problematic switch and issued a show vtp status to see that it had the setting disabled. it had also gotten the latest database from the server and I could see the revision had incremented to 72.
I issued a show interfaces trunk and the "Vlans allowed" and "Vlans in spanning.." lined up like I felt like they would. Before, there were missing (pruned) vlans that shouldn't have been pruned at all.
I was then able to ping the hosts on the new switch that were on the Vlan that was previously pruned. I am still not understanding why it was pruned in the first place.
Thanks for the help all.
I verified that the Vlan was still pruned on the switch.
I logged into the switch designated as the VTP server
#conf t
#no vtp pruning
I verified it was disabled and I went to the problematic switch and issued a show vtp status to see that it had the setting disabled. it had also gotten the latest database from the server and I could see the revision had incremented to 72.
I issued a show interfaces trunk and the "Vlans allowed" and "Vlans in spanning.." lined up like I felt like they would. Before, there were missing (pruned) vlans that shouldn't have been pruned at all.
I was then able to ping the hosts on the new switch that were on the Vlan that was previously pruned. I am still not understanding why it was pruned in the first place.
Thanks for the help all.
Sounds like VTP just hiccuped for some reason.
From other topic.
I have a brand new Cisco 9300 access layer switch that is trunked to a Dell Force 10 core switch. The core switch is a VTP Server for several VLANs.Maybe core Dell and new Cisco switch VTP are not fully compatible.
Oh man! Now that's a important piece of information missing..lol!
ASKER
I found out later that a different Cisco switch was the server. I had been under the impression that the Force 10 was a vtp server and they can't participate in VTP at all.
ASKER
Thanks to everyone for helping. I'm going with something being weird with pruning consistency among vtp clients and disabling it forced a new replication of the database and trued things up. I probably won't re-enable it.
ASKER