cURL error 60: SSL certificate problem: self signed certificate in certificate chain
Installed new Microsoft Server 2012 R2 with new MySQL 8.0, PHP 7.2 and wordpress 5.1.
Server is functioning correctly however when I download a plugin I get this error:
cURL error 60: SSL certificate problem: self signed certificate in certificate chain
I downloaded the newest cacert.pem file and placed it on the server in this directory:
C:\php\cacert.pem
I edited the php.ini file in this path C:\Program Files\PHP\v7.2 to this:
[curl]
; A default value for the CURLOPT_CAINFO option. This is required to be an
; absolute path.
;curl.cainfo =
curl.cainfo = "C:\php\cacert.pem";
However, I'm still getting the same error "cURL error 60: SSL certificate problem: self signed certificate in certificate chain" when I download a plugin.
Can you provide any suggestions on how to fix or bypass this?
Server is functioning correctly however when I download a plugin I get this error:
cURL error 60: SSL certificate problem: self signed certificate in certificate chain
I downloaded the newest cacert.pem file and placed it on the server in this directory:
C:\php\cacert.pem
I edited the php.ini file in this path C:\Program Files\PHP\v7.2 to this:
[curl]
; A default value for the CURLOPT_CAINFO option. This is required to be an
; absolute path.
;curl.cainfo =
curl.cainfo = "C:\php\cacert.pem";
However, I'm still getting the same error "cURL error 60: SSL certificate problem: self signed certificate in certificate chain" when I download a plugin.
Can you provide any suggestions on how to fix or bypass this?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Is there a simpler solution than openSSL it wants a third party tool just to install it.
ASKER
How do you inject your CA root issuance chain into your curl setup?
You could probably check out the certificate chain from your browser. Open up IE and go to https://www.wordpress.com. Then click on the lock icon in the address bar and click on View Certificates. (The process might vary depending on which browser you actually use, if not IE). Then in the certificate viewer pop-up, go to the Certification Path tab. If you're behind an SSL-intercepting proxy or firewall, the path might look different.
Here's a screenshot that shows an example of what the REAL, non-intercepted certification path looks like (left) and an example of an intercepted path (right):
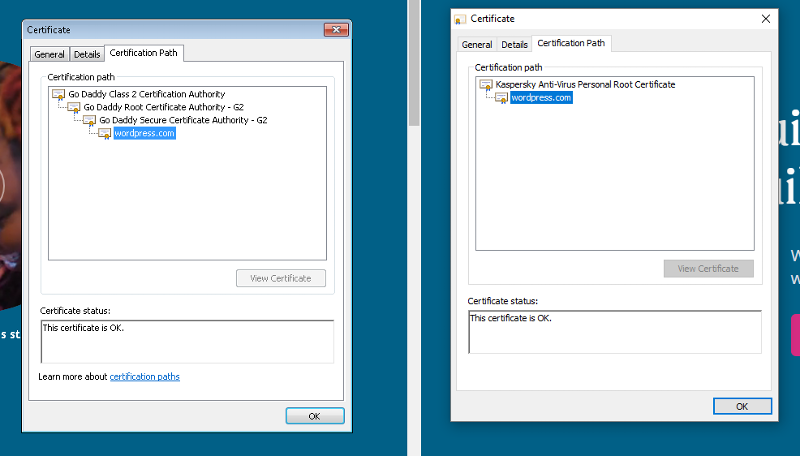
Usually SSL-intercepting proxies won't try to emulate the full chain (notice how the real path/chain has 4 elements in the full chain, whereas the Kaspersky-intercepted chain just has 2 elements, so that can be a quick giveaway.
You can also check the thumbprint of the certificate at the bottom of the details tab. For www.wordpress.com, the thumbprint should start with "79 1a 83" and end with "a0 e0 c3". So if that doesn't match what you have, then that pretty much confirms that you have some kind of SSL interception going on.
And if that's the case, then from there, you can export the root certificate in Base64/PEM format. Just go back to the Certification Path tab and select the root CA node (hopefully there's just one), then click on the View Certificate button. Then go to the Details tab and click on Copy to File... and export to Base-64 encoded X.509 .CER format and put the file in the same folder with your Wordpress site.
Then open up your php.ini file and find and set curl.cainfo to the full path leading to that exported file, like this:
curl.cainfo = "C:\path\to\your\wordpress
To be honest, I can't recall off the top of my head if there's any specific format necessary for the ca info file, but that should give you a good start.
Here's a screenshot that shows an example of what the REAL, non-intercepted certification path looks like (left) and an example of an intercepted path (right):
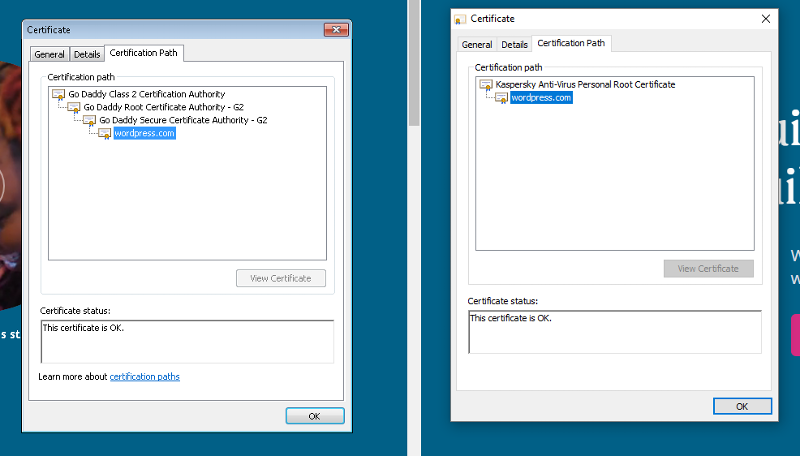
Usually SSL-intercepting proxies won't try to emulate the full chain (notice how the real path/chain has 4 elements in the full chain, whereas the Kaspersky-intercepted chain just has 2 elements, so that can be a quick giveaway.
You can also check the thumbprint of the certificate at the bottom of the details tab. For www.wordpress.com, the thumbprint should start with "79 1a 83" and end with "a0 e0 c3". So if that doesn't match what you have, then that pretty much confirms that you have some kind of SSL interception going on.
And if that's the case, then from there, you can export the root certificate in Base64/PEM format. Just go back to the Certification Path tab and select the root CA node (hopefully there's just one), then click on the View Certificate button. Then go to the Details tab and click on Copy to File... and export to Base-64 encoded X.509 .CER format and put the file in the same folder with your Wordpress site.
Then open up your php.ini file and find and set curl.cainfo to the full path leading to that exported file, like this:
curl.cainfo = "C:\path\to\your\wordpress
To be honest, I can't recall off the top of my head if there's any specific format necessary for the ca info file, but that should give you a good start.
ASKER
Figured it out by a hint from gr8gonzo.
I do have a CA FW that was blocking the certificates. When I put the wordpress domain in the bypass on the FW setting everything started to flow. Thanks.
I do have a CA FW that was blocking the certificates. When I put the wordpress domain in the bypass on the FW setting everything started to flow. Thanks.
There are 3x fixes.
1) You can inject your CA root issuance chain into your curl setup. If you don't know how to do this, best start searching online for how to do this + then you'll have to convert instructions you find over to however you installed curl on Windows.
2) You can pass --insecure to curl, to skip cert check.
3) You can use a real cert, like https://LetsEncrypt.org which has been providing free certs for years now.