Powershell- Removing NTFS File Permissions on Disabled Users
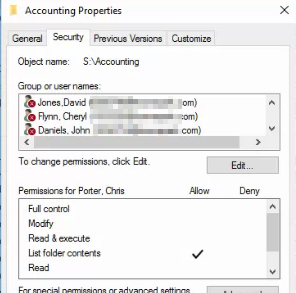
We have an issue at our company that Im trying to wrap my head around. When we off-board a user, we obviously remove the user from all AD Groups, Disable Object and reset password. But for some reason i have not found a way to remove old employees (disabled user objects) from NTFS File share permissions. So we have 100s of users still listed in our NTFS File Share Permissions that need to be removed. Their icon has a red x. Is there a script that will find all users who are disabled and remove them from the shared folder NTFS permissions of all folders within our S drive?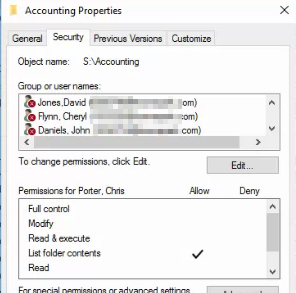
they can't read nor write.. your on boarding process is flawed never assign users to permissions, always just use groups.
ASKER
Yes sir i understand this. We took over as a new IT Department and this was what we were handed. I understand they cant read/write but still want to clean this up.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I am getting this error though when i try to run this via a For-Each statement.
New-Object : Cannot find an overload for "NTAccount" and the argument count:
"4092".
At C:\Scripts\Remove-Folderpe
+ ... $usersid = New-Object System.Security.Principal.
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: (:) [New-Object], MethodExcept
ion
+ FullyQualifiedErrorId : ConstructorInvokedThrowExc
Shell.Commands.NewObjectCo
Any idea what it might be? I tweaked the PS script as below.
$date = Get-Date -Format "MM-dd-yyyy_HH:mm_"
Start-Transcript -Path C:\Scripts\$date"removeFol
$domain=Get-ADDomain | select -ExpandProperty NetBIOSName
$CurrentUsers = get-aduser –SearchBase “OU=_Disabled,DC=townepark
$acl = Get-Acl 'I:\CorpShare\Compliance Administration'
foreach($user in $CurrentUsers){
write-host "Working on" $user.Name "Processing..." -ForegroundColor Cyan
$AccessRule = New-Object System.Security.AccessCont
$acl.RemoveAccessRule($Acc
$usersid = New-Object System.Security.Principal.
$acl.PurgeAccessRules($use
$acl | Set-Acl 'I:\CorpShare\Compliance Administration'
Write-Host $user.Name " completed..." -ForegroundColor DarkYellow
}
Stop-Transcript
New-Object : Cannot find an overload for "NTAccount" and the argument count:
"4092".
At C:\Scripts\Remove-Folderpe
+ ... $usersid = New-Object System.Security.Principal.
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: (:) [New-Object], MethodExcept
ion
+ FullyQualifiedErrorId : ConstructorInvokedThrowExc
Shell.Commands.NewObjectCo
Any idea what it might be? I tweaked the PS script as below.
$date = Get-Date -Format "MM-dd-yyyy_HH:mm_"
Start-Transcript -Path C:\Scripts\$date"removeFol
$domain=Get-ADDomain | select -ExpandProperty NetBIOSName
$CurrentUsers = get-aduser –SearchBase “OU=_Disabled,DC=townepark
$acl = Get-Acl 'I:\CorpShare\Compliance Administration'
foreach($user in $CurrentUsers){
write-host "Working on" $user.Name "Processing..." -ForegroundColor Cyan
$AccessRule = New-Object System.Security.AccessCont
$acl.RemoveAccessRule($Acc
$usersid = New-Object System.Security.Principal.
$acl.PurgeAccessRules($use
$acl | Set-Acl 'I:\CorpShare\Compliance Administration'
Write-Host $user.Name " completed..." -ForegroundColor DarkYellow
}
Stop-Transcript
Post the whole Ps1 please. and use the "code" tags for each code block.
ASKER
Thank you Jose for your quick response. I found the issue. I made a mistake in this part of the code.
$usersid = New-Object System.Security.Principal.
The alias i chose $CurrentUsers was wrong. Should have been $Users that are being piped through. Now works like a charm.
$usersid = New-Object System.Security.Principal.
$usersid = New-Object System.Security.Principal.
The alias i chose $CurrentUsers was wrong. Should have been $Users that are being piped through. Now works like a charm.
$usersid = New-Object System.Security.Principal.