not able to install windows MSI Installer on the PCs where the end point security is installed
Dear Experts,
We have end point protection SentinelOne installed on all PC’s in our network, we want
…
Dear Experts,
We have end point protection SentinelOne installed on all PC’s in our network, we want
…Making an SMTP test to email security gateway using MX Toolbox and I get the following report, SMTP
…In smaller organizations with limited staffing budgets for their IT department, it appears to be
…Hello Experts,
We're currently in the process of partnering with a company that owns a
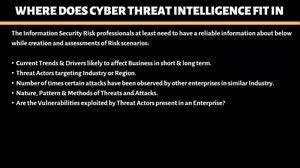
…There are so many cybersecurity issues these days. With hackers remaining on a company's systems for
…What are some great applications/tools to Scan for Vulnerabilities, and then to Fix Vulnerabilities
…