Browse All Tutorials > Security
Have a question while you're learning?
Get in-depth explanations, tips, further insights, and more from Certified Experts. Our experts are vetted industry professionals eager to help you learn from their experiences.
Tutorial Syllabus(15 Lessons)
Tutorial Description
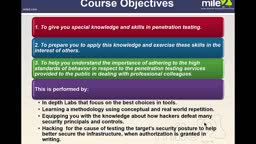
This Official Mile2® cyber security certification training series covers everything you need to know about becoming a Certified Penetration Testing Engineer. Participants will learn about logistics of pen testing, Linux fundamentals, information gathering, detecting live systems, enumeration, vulnerability assessments, undercover malware, Windows hacking, hacking UNIX/Linux, advanced exploitation techniques, pen testing wireless networks, networks, sniffing and IDS, injecting the database, attacking web technologies, and project documentation. This series, valued at $3,000, is available to Premium members, Team Accounts, and Qualified Experts.
This series prepares you to take the CPTE certification exam.
Becoming a Certified Penetration Testing Engineer lets you use the key elements of penetration testing to keep businesses safe through the practice of ethical hacking. Explore these penetration testing techniques to identify and repair the latest vulnerabilities in a system to make sure it is secure. This will protect businesses and individuals from malicious hackers. Once inside, hackers can access private information, such as usernames, passwords, credit card numbers, and social security numbers of clients and employees. Certified Penetration Testing Engineers are the solution to the problem of hackers exploiting the businesses they serve.
Having a Certified Penetration Testing Engineer on staff enhances the business. This role keeps partners, employees, and clients safe and helps identify protection needs while reducing any risks that could be there for hackers to take advantage of.
Being a Certified Penetration Testing Engineer, leads to professional roles not limited to ethical hacker, security consultants, system administrators, and chief security officers.
Certification Exam Process
Upon completion of this series, the Mile2® CPTE certification series certification exam can be purchased here.
Becoming a Certified Penetration Testing Engineer lets you use the key elements of penetration testing to keep businesses safe through the practice of ethical hacking. Explore these penetration testing techniques to identify and repair the latest vulnerabilities in a system to make sure it is secure. This will protect businesses and individuals from malicious hackers. Once inside, hackers can access private information, such as usernames, passwords, credit card numbers, and social security numbers of clients and employees. Certified Penetration Testing Engineers are the solution to the problem of hackers exploiting the businesses they serve.
Having a Certified Penetration Testing Engineer on staff enhances the business. This role keeps partners, employees, and clients safe and helps identify protection needs while reducing any risks that could be there for hackers to take advantage of.
Being a Certified Penetration Testing Engineer, leads to professional roles not limited to ethical hacker, security consultants, system administrators, and chief security officers.
Certification Exam Process
Upon completion of this series, the Mile2® CPTE certification series certification exam can be purchased here.