How to Configure ADFS Web Application Proxy for ADSF
The WAP should not be part of the domain and should be used as a standalone
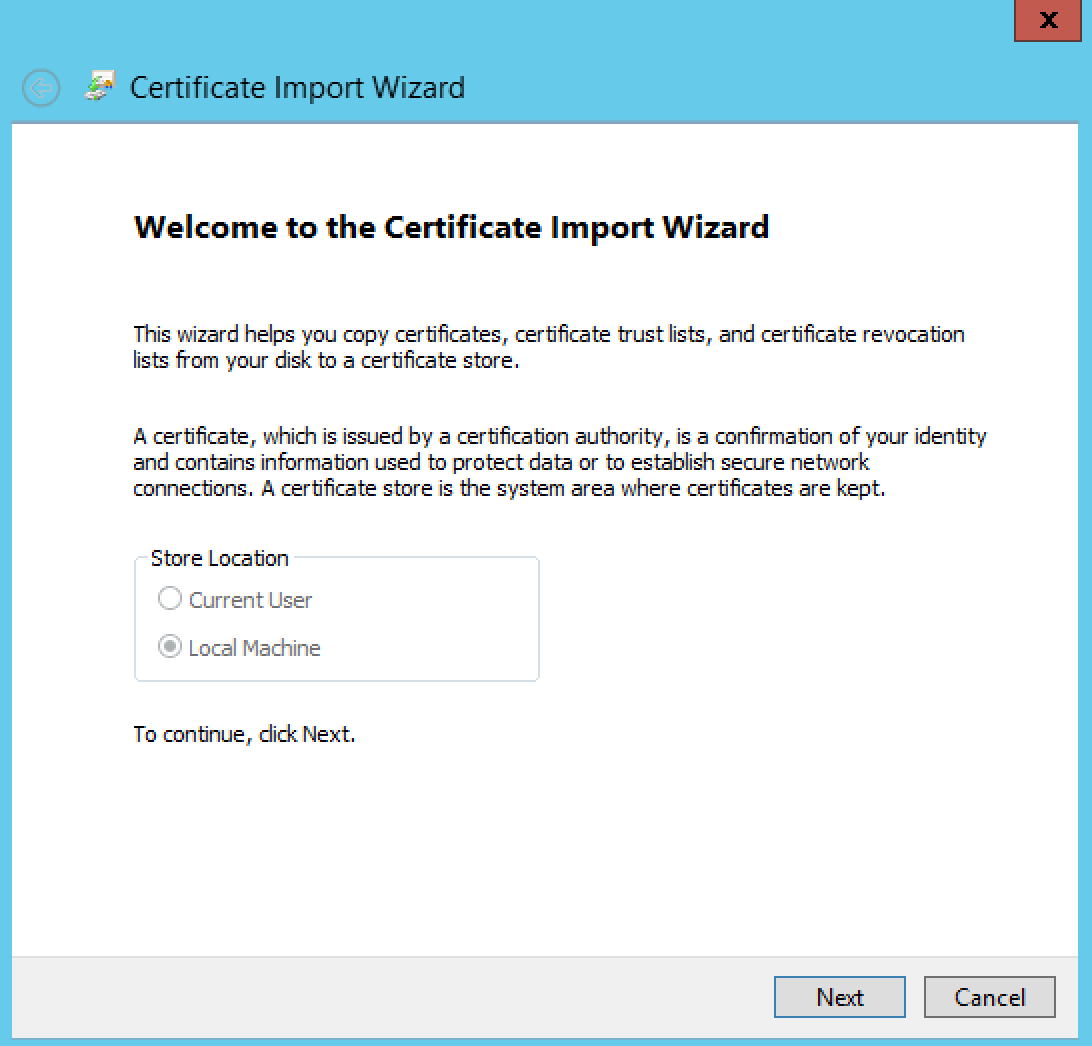
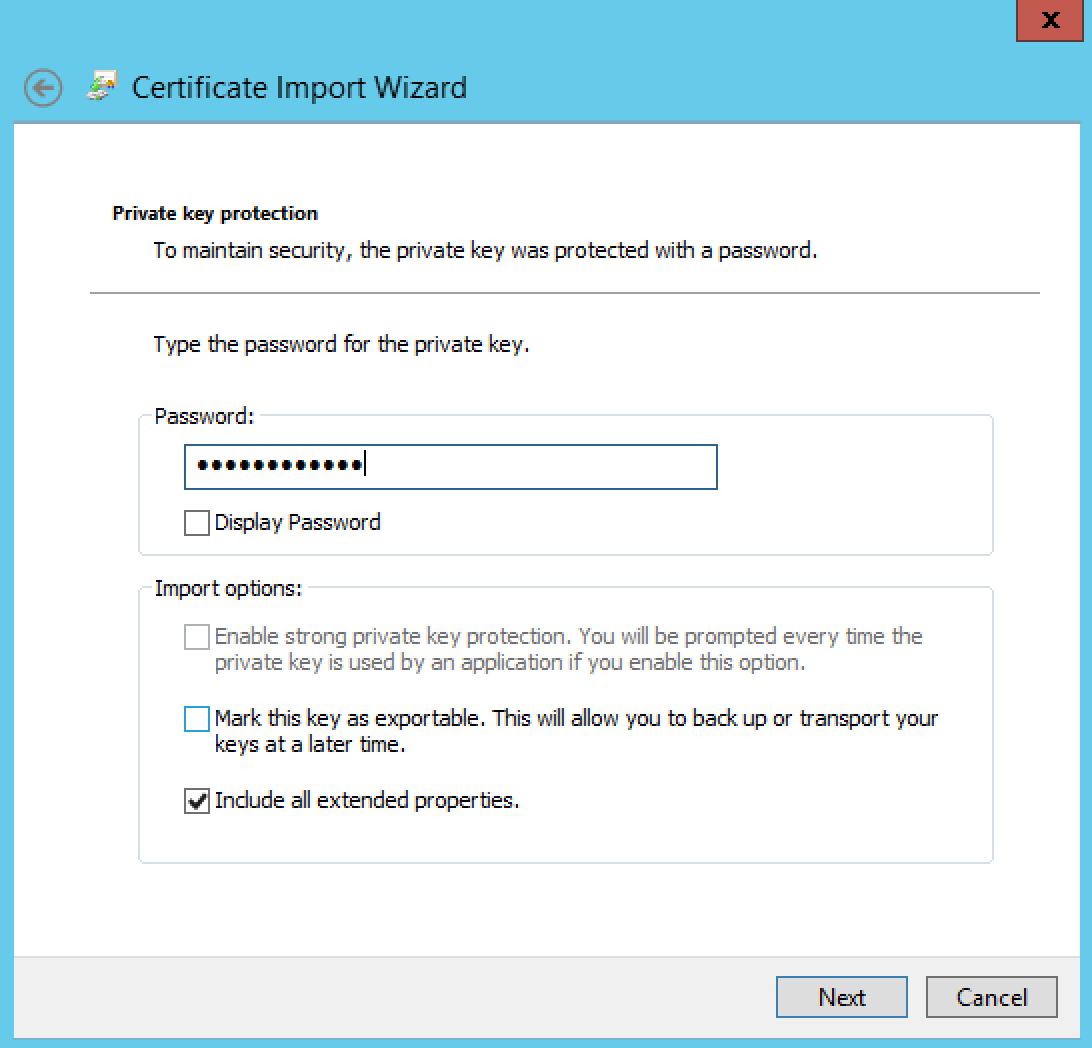
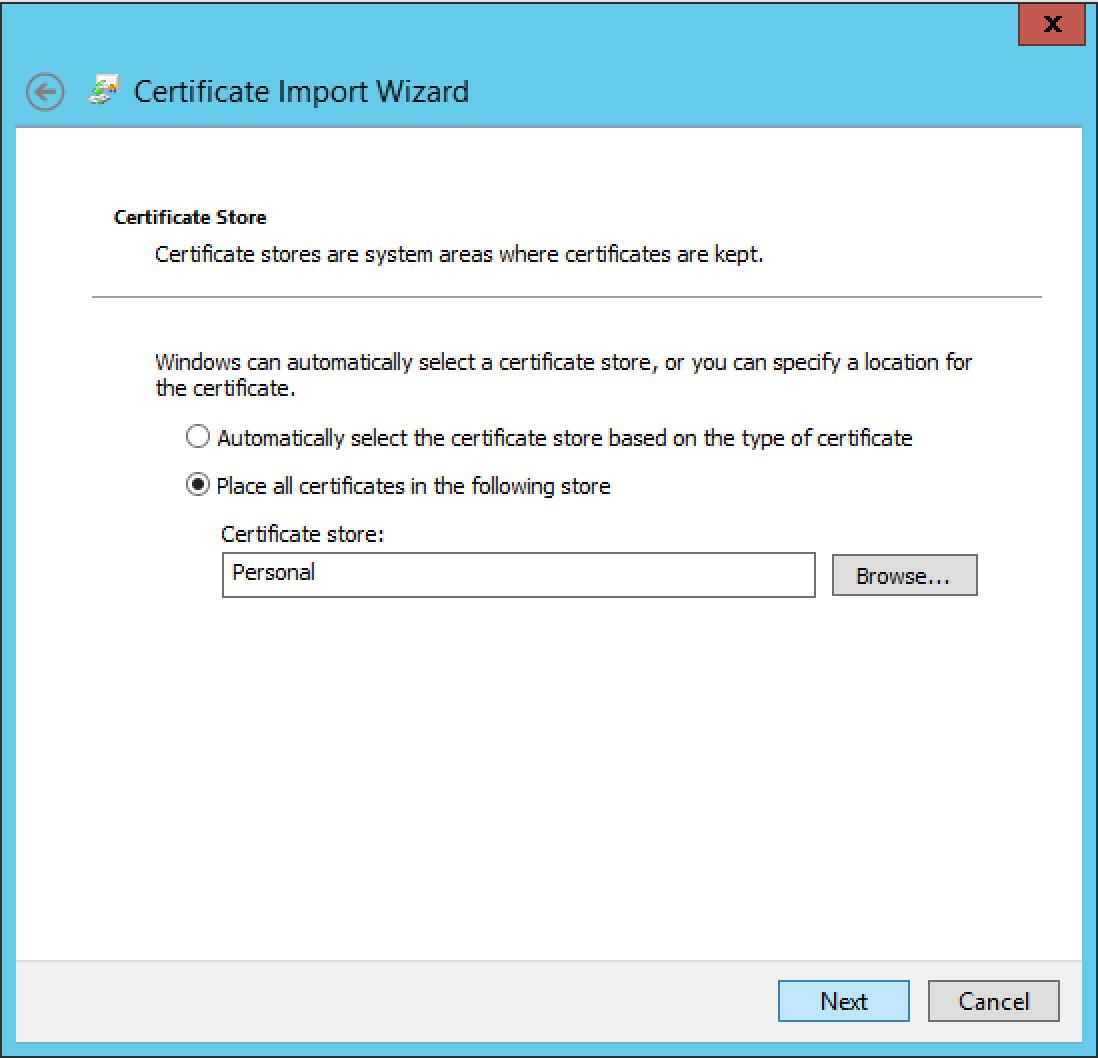
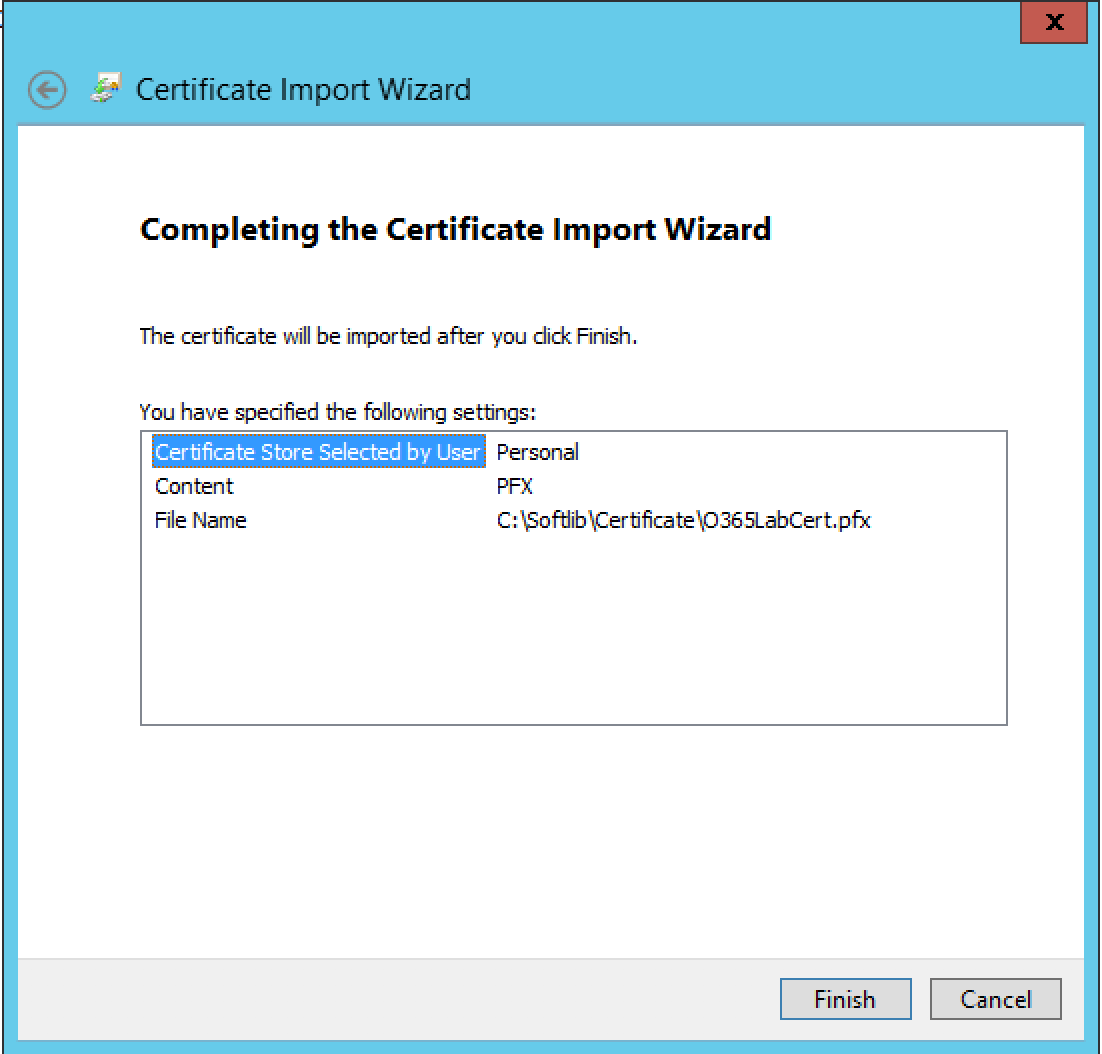
To start the configuration, the SSL certificate used on the ADFS (Active Directory Federation Services) Server needs to be installed on the WAP Server.
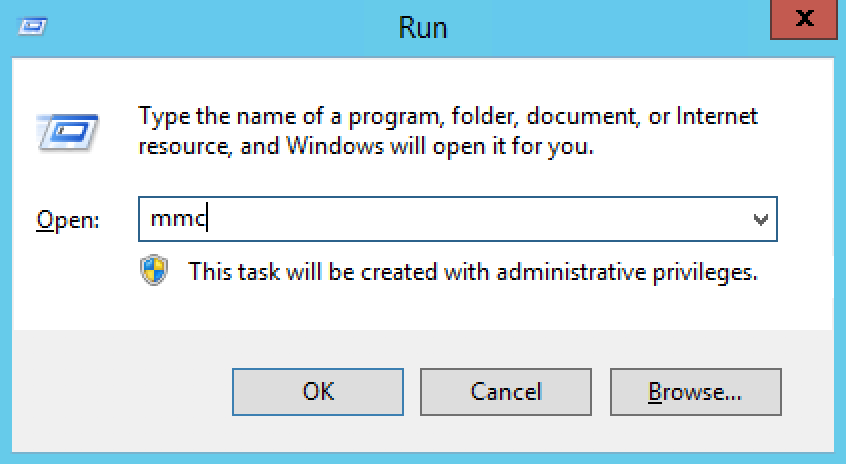
Open the Run box, then type mmc
Tip! Click any graphic to get a full-size view...
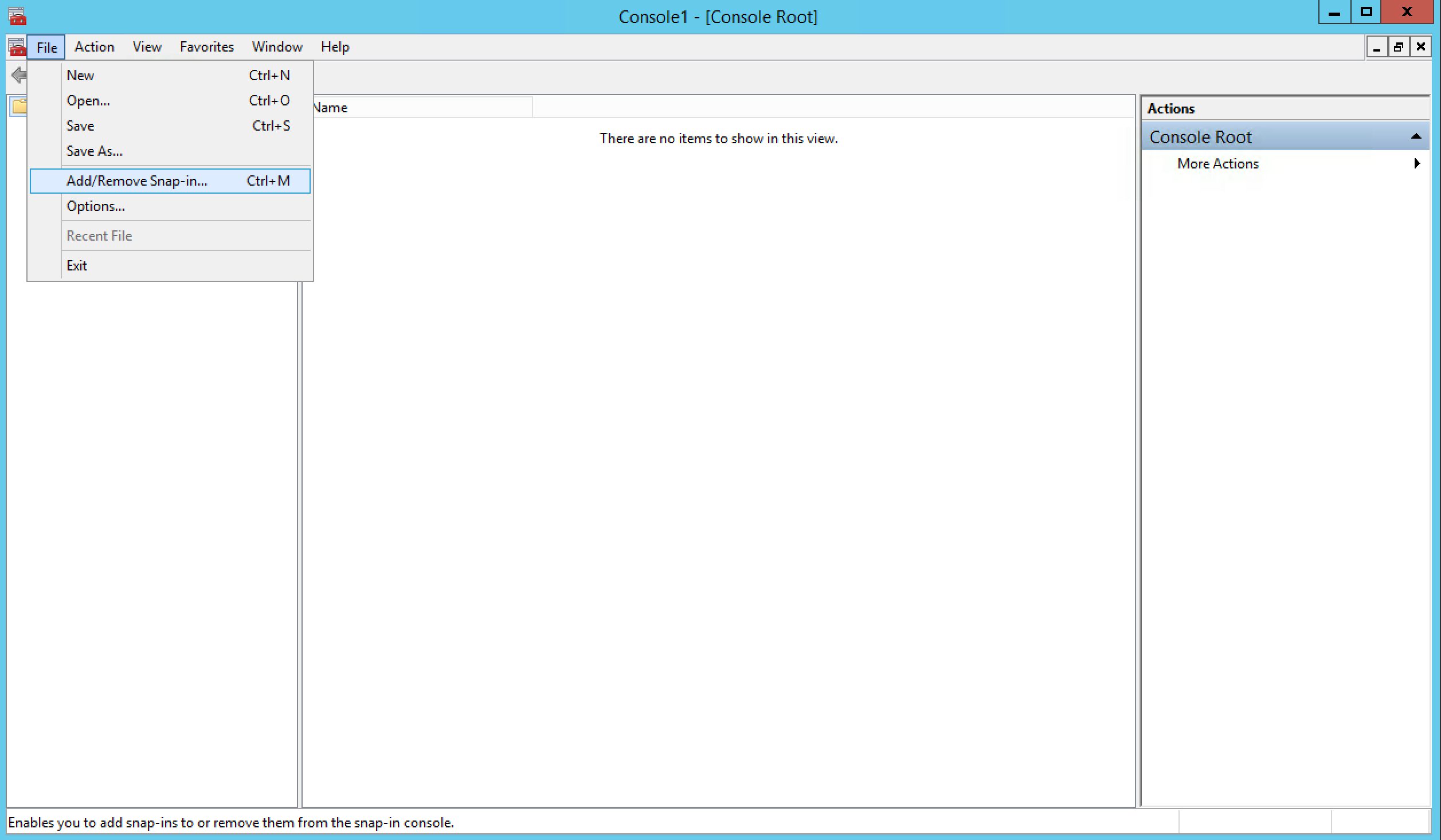
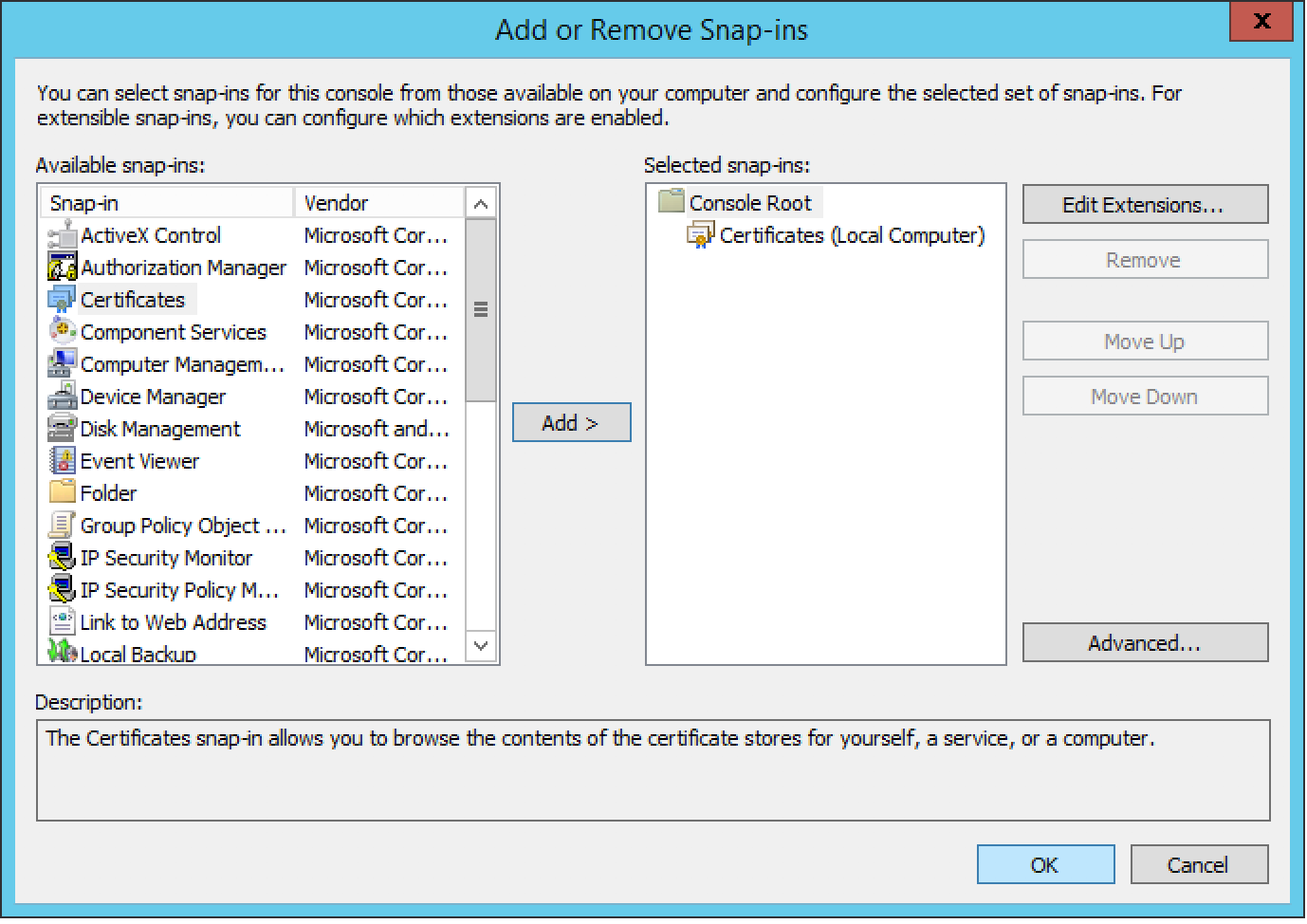
Once the MMC console is open, click on File >> Add /Remove Snap-In
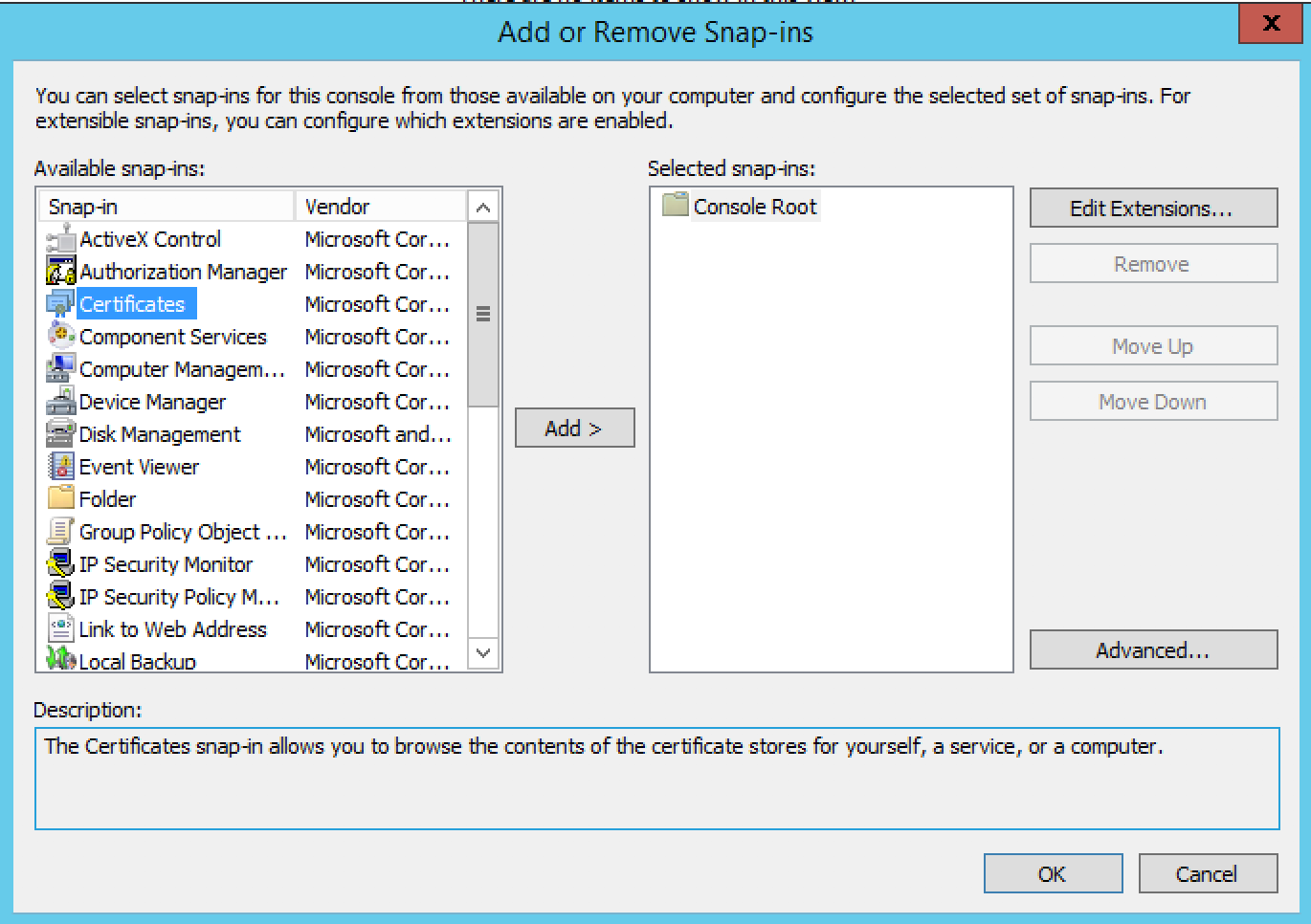
Select Certificates from the list and then click on Add.
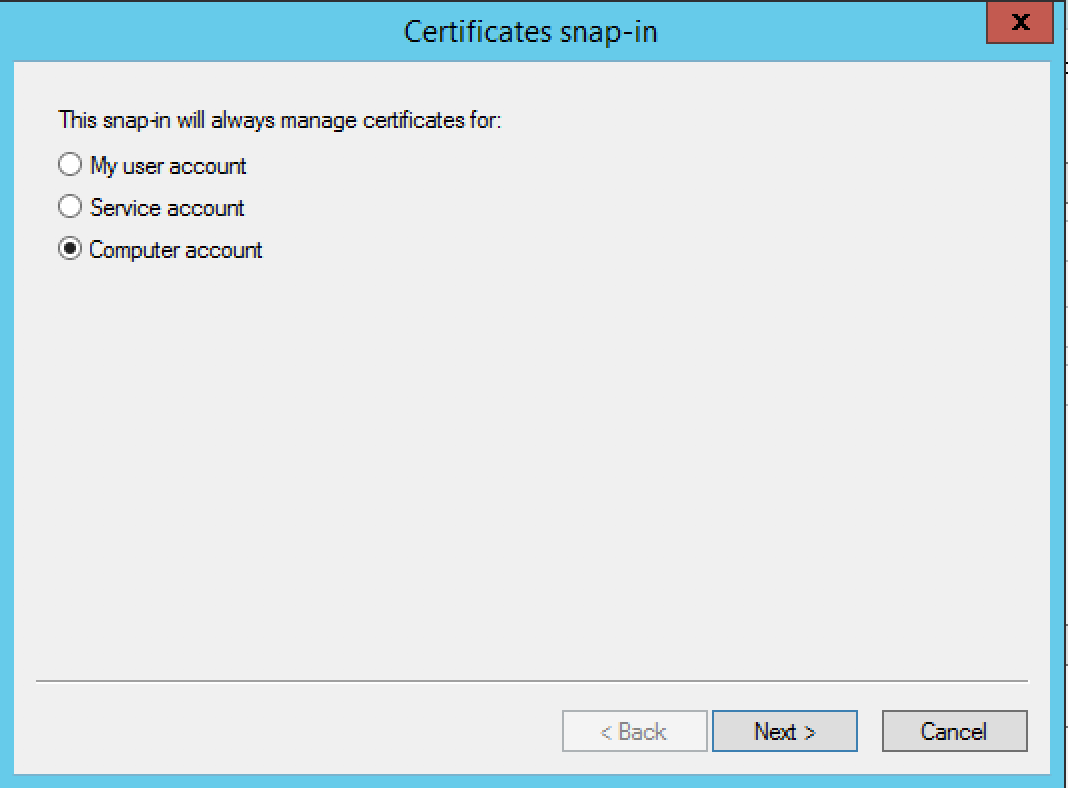
Select Computer account from the list, then click Next
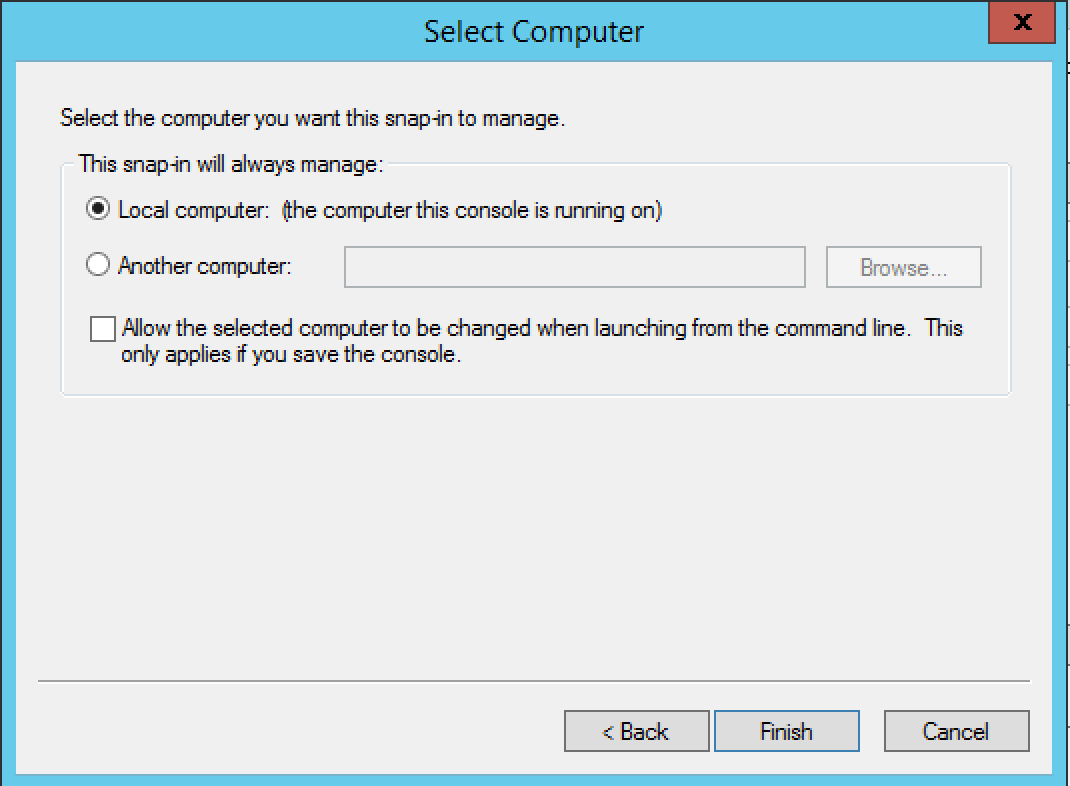
Select Local computer, then click Next
To close the Snap-in, Click on OK
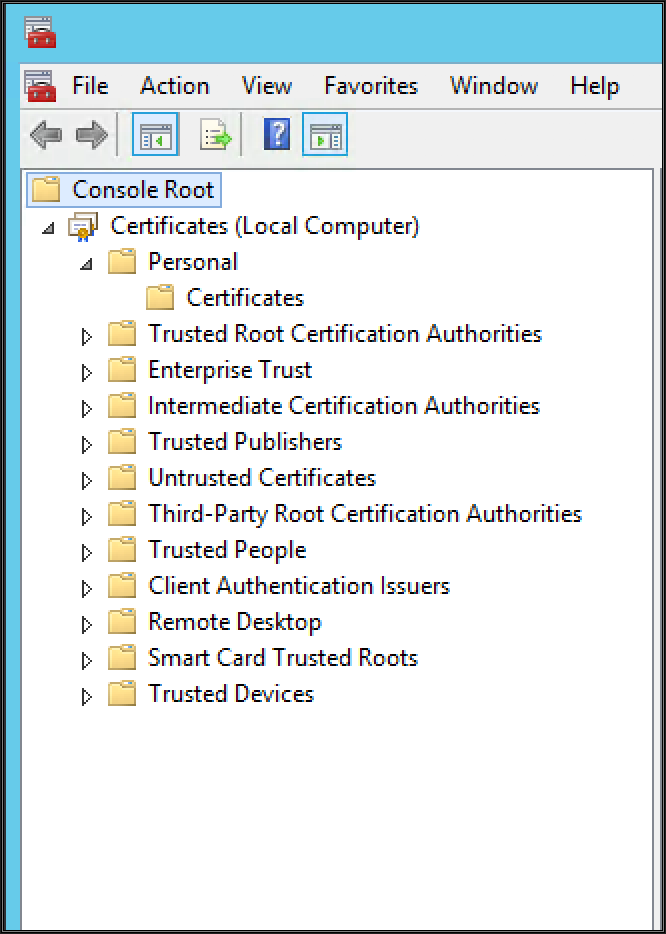
Expand Certificate, then expand Personal and click on Certificates
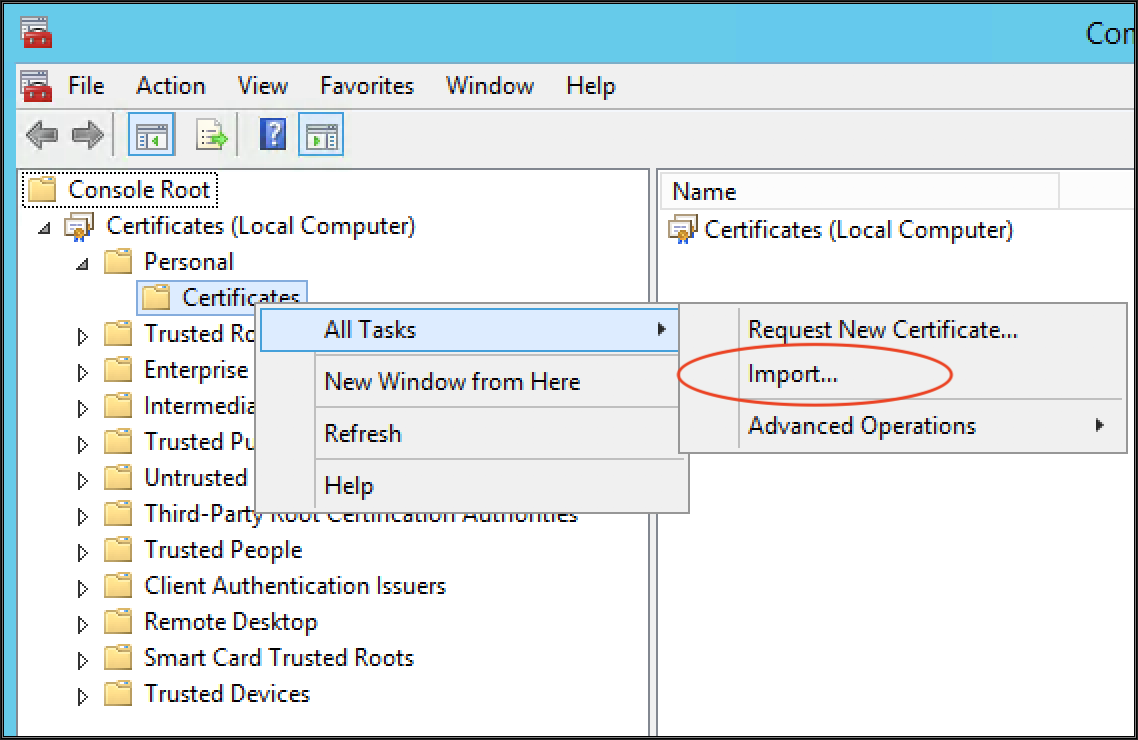
Right Click on Personal Certificates, then All Tasks and click on Import
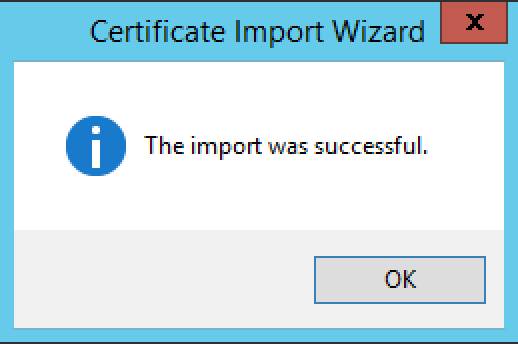
Follow the Import Wizard, then complete the Certificate import process
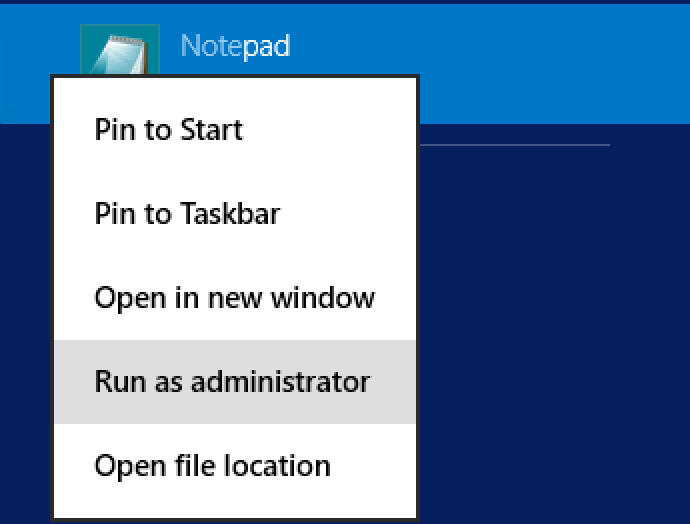
The next step is to edit the Hosts File and add an entry for the ADFS Server. To open the Host file, Run Notepad as Administrator
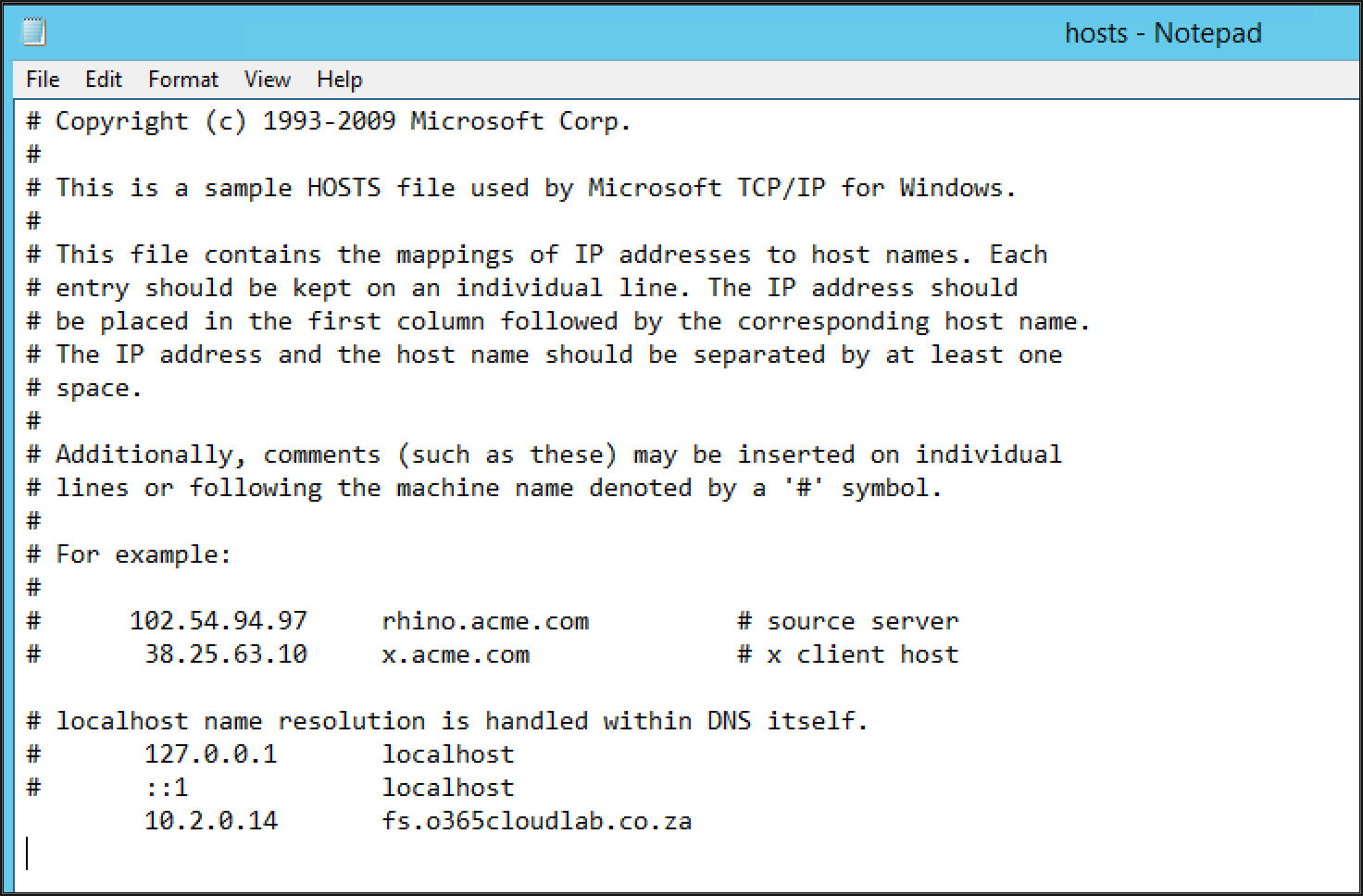
Hosts File Location: C:\Windows\System32\drives\etc
Then navigate to the Host File location
Modify the Host File, by adding the entry for the ADFS server with the associated IP.
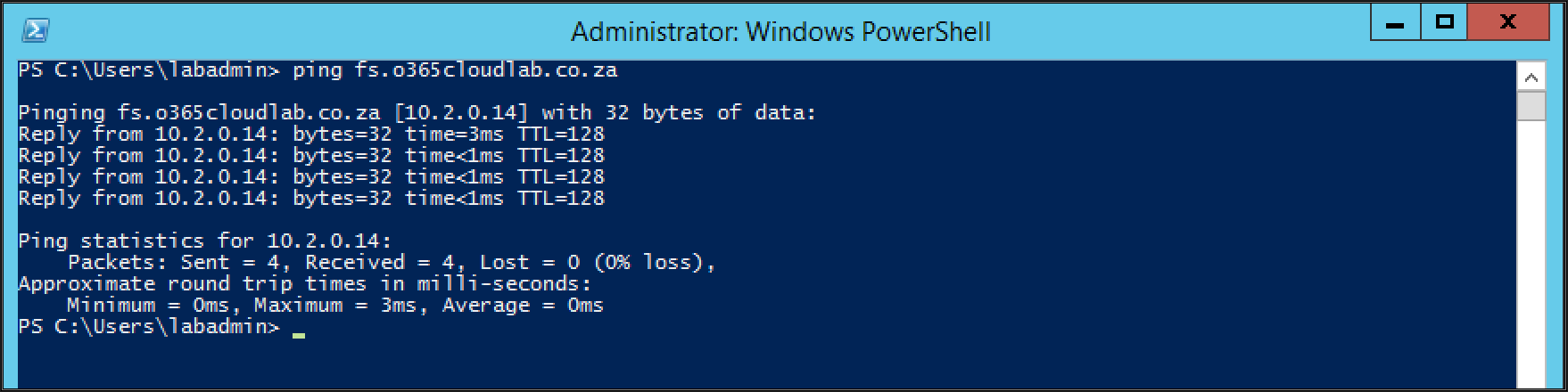
Example: 10.2.0.14fs.o365cloudlab.co.za
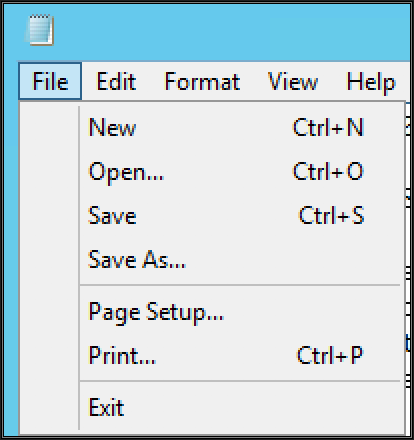
Click on File and then Save, to save the changes.
Lastly, let's ping the new entry from the WAP Server, you should receive a response.
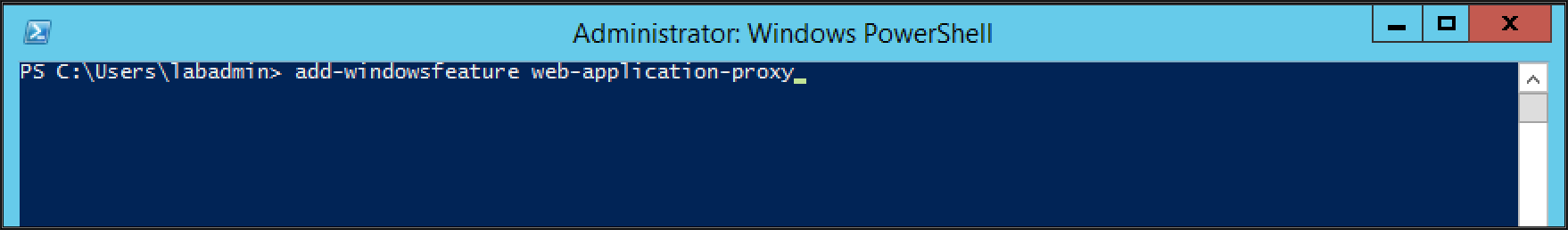
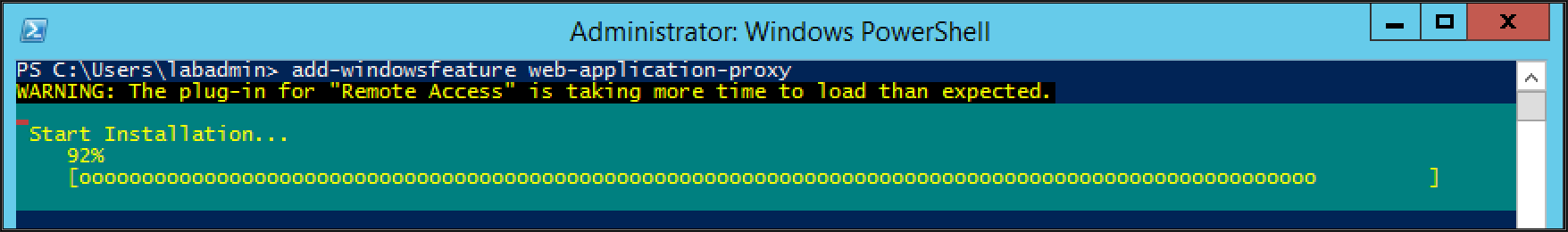
From a PowerShell session, run the following command to start the installation process of the Web Application Proxy role.
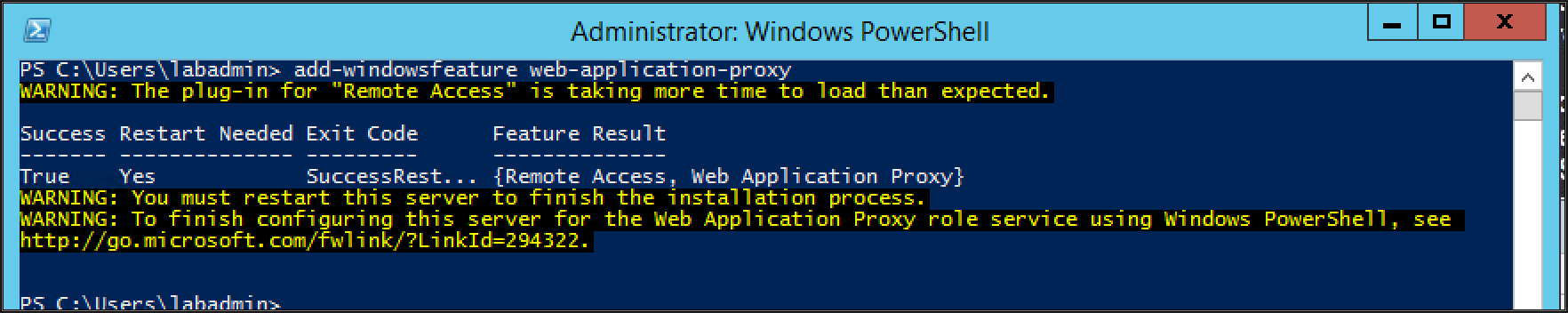
add-windowsfeature web-application-proxyOnce the Installation has been completed, run the following command in the same PowerShell Session to restart the Server.
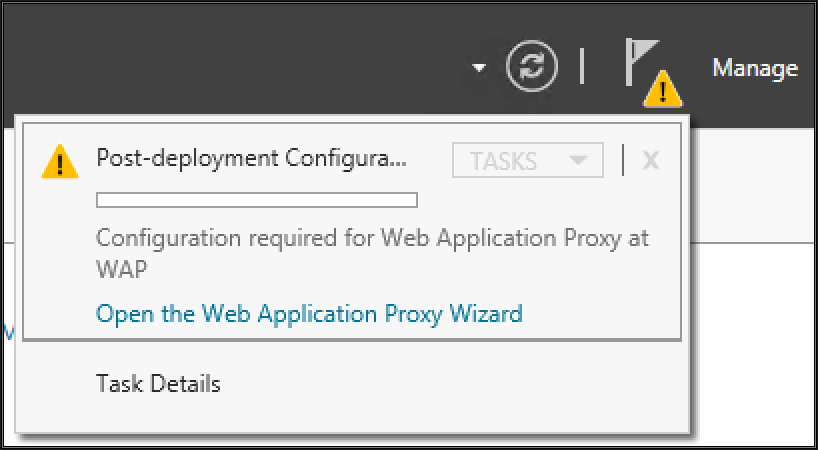
Restart-ComputerLog back in to the server with the same credentials and Navigate to Server Manager and complete the configuration Process of the Role.
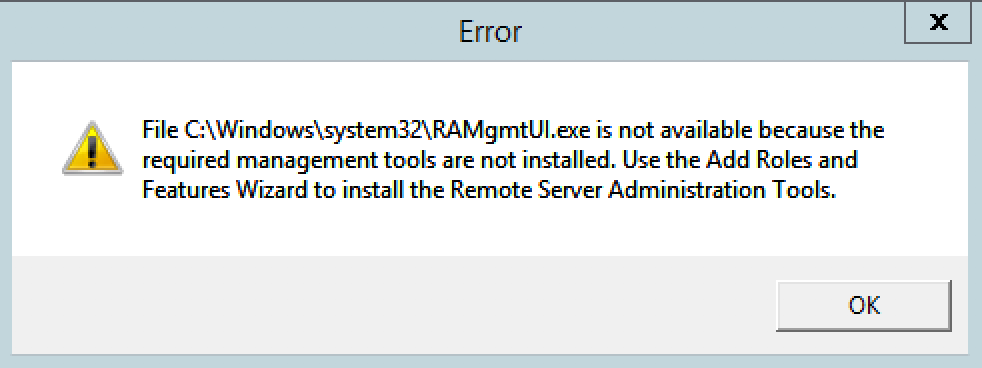
When you click on “Open the Web Application Proxy Wizard”, you are prompted with the following Error.
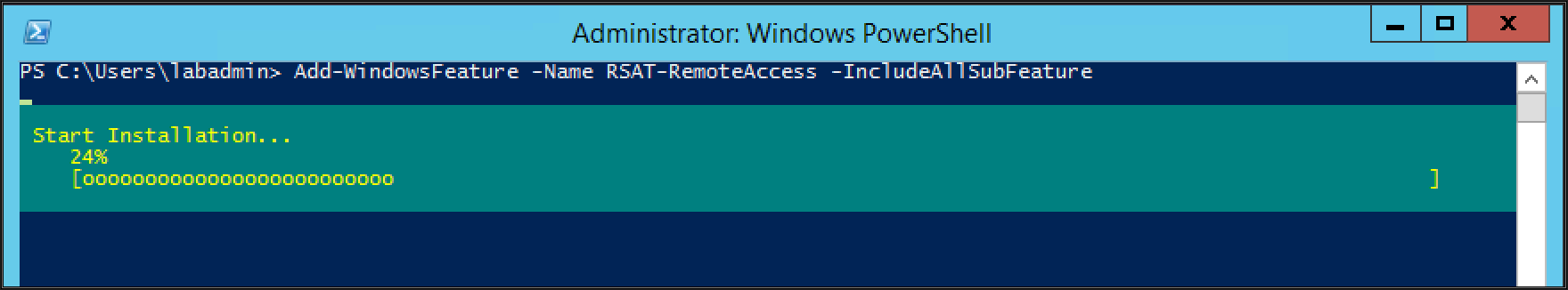
The RSAT-Administration Modules have not been added to the Server, to resolve this Error. Run the Following command in PowerShell.
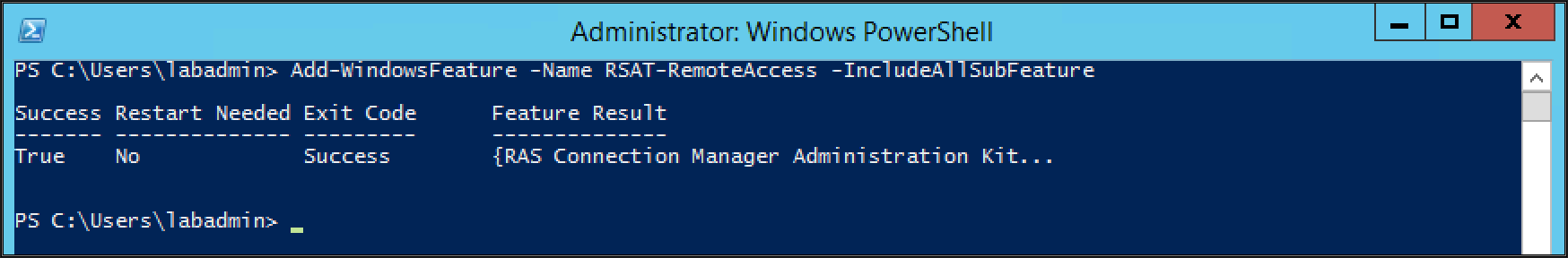
Add-WindowsFeature -Name RSAT-RemoteAccess -IncludeAllSubFeatureClose the Server Manager Console and Launch it again.
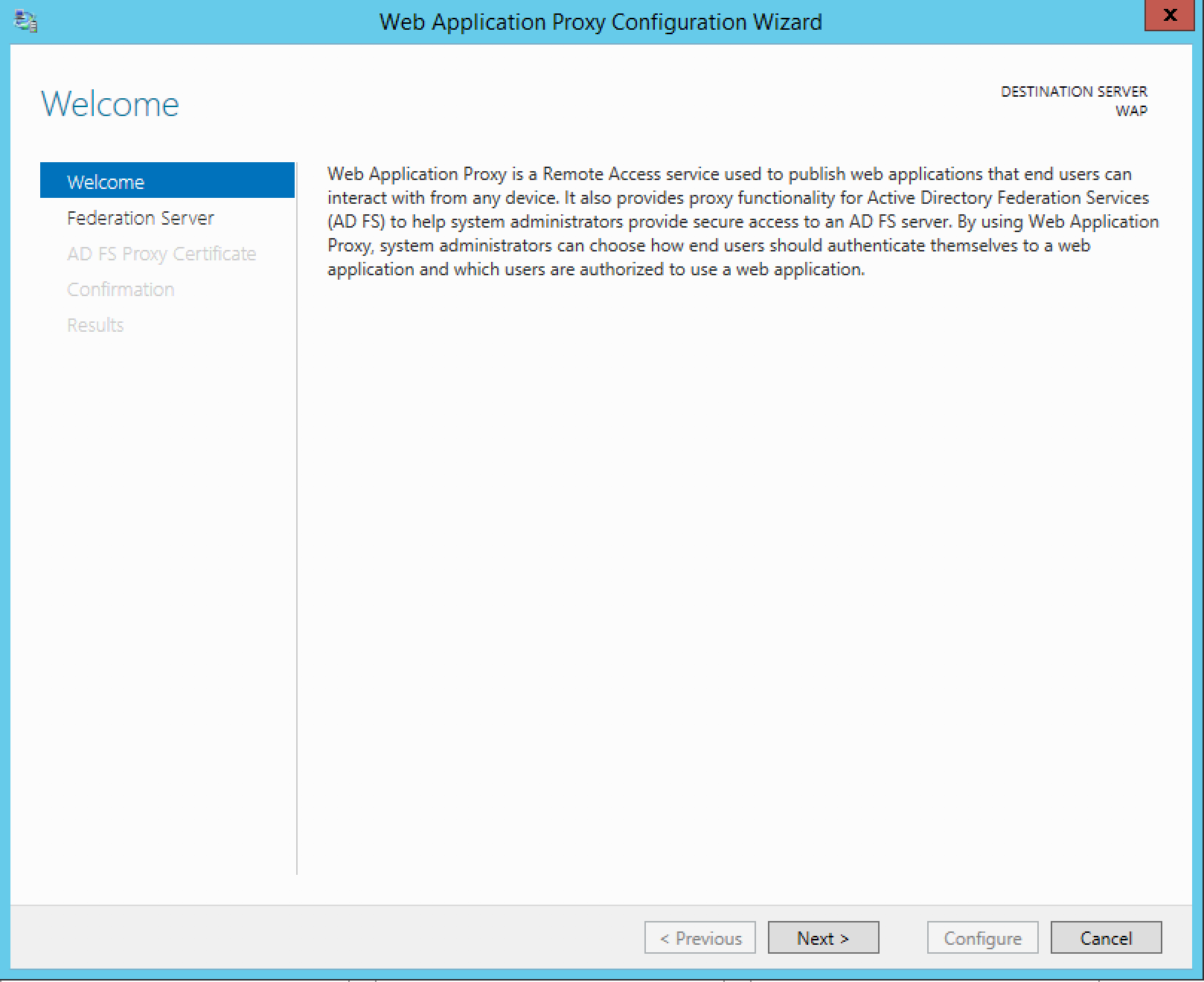
The Web Application Proxy Wizard will open, then Click on Next
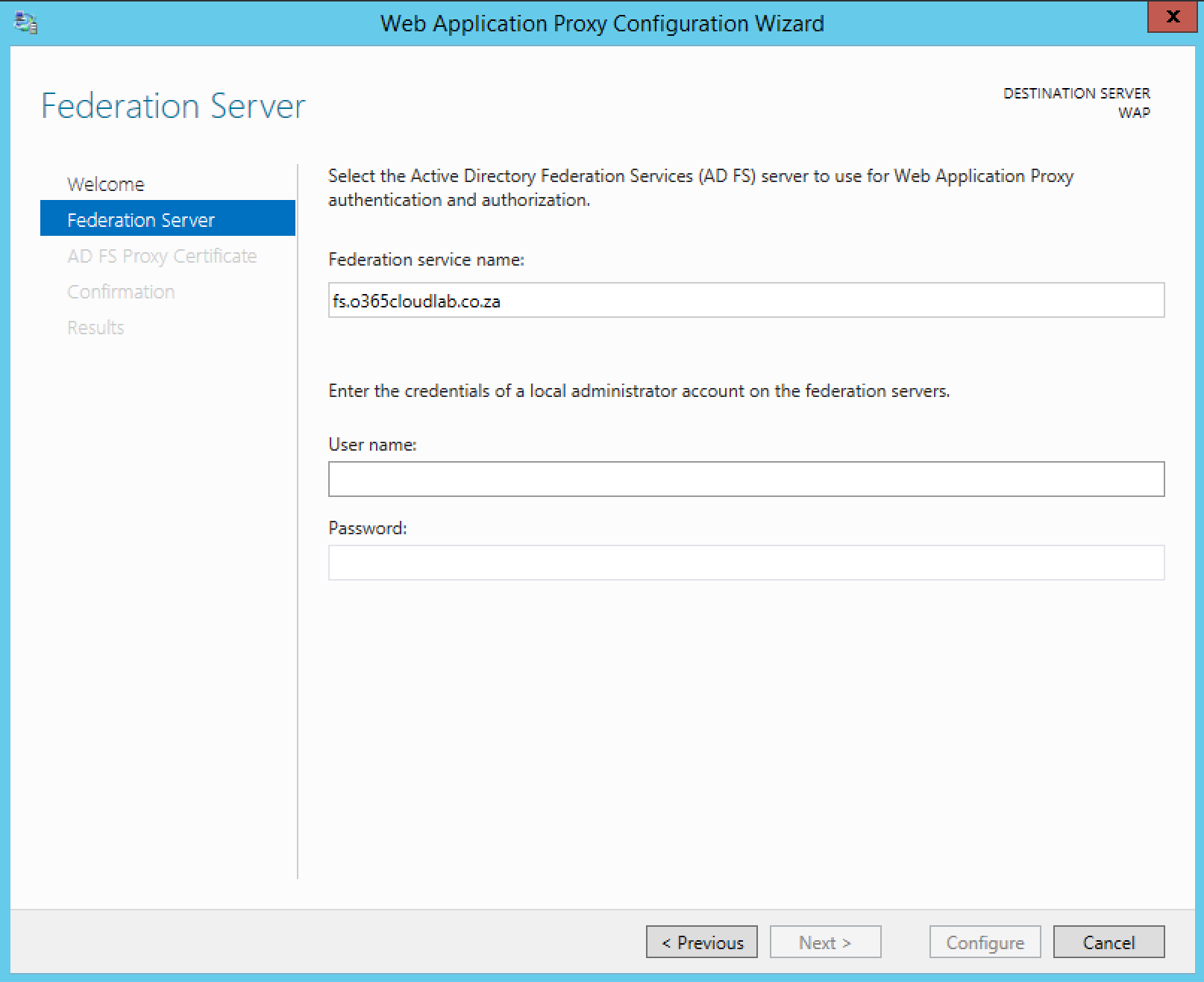
On the Federation service name, add the DNS name for the ADFS server which was specified in the Host File. Then provide a domain username and password.
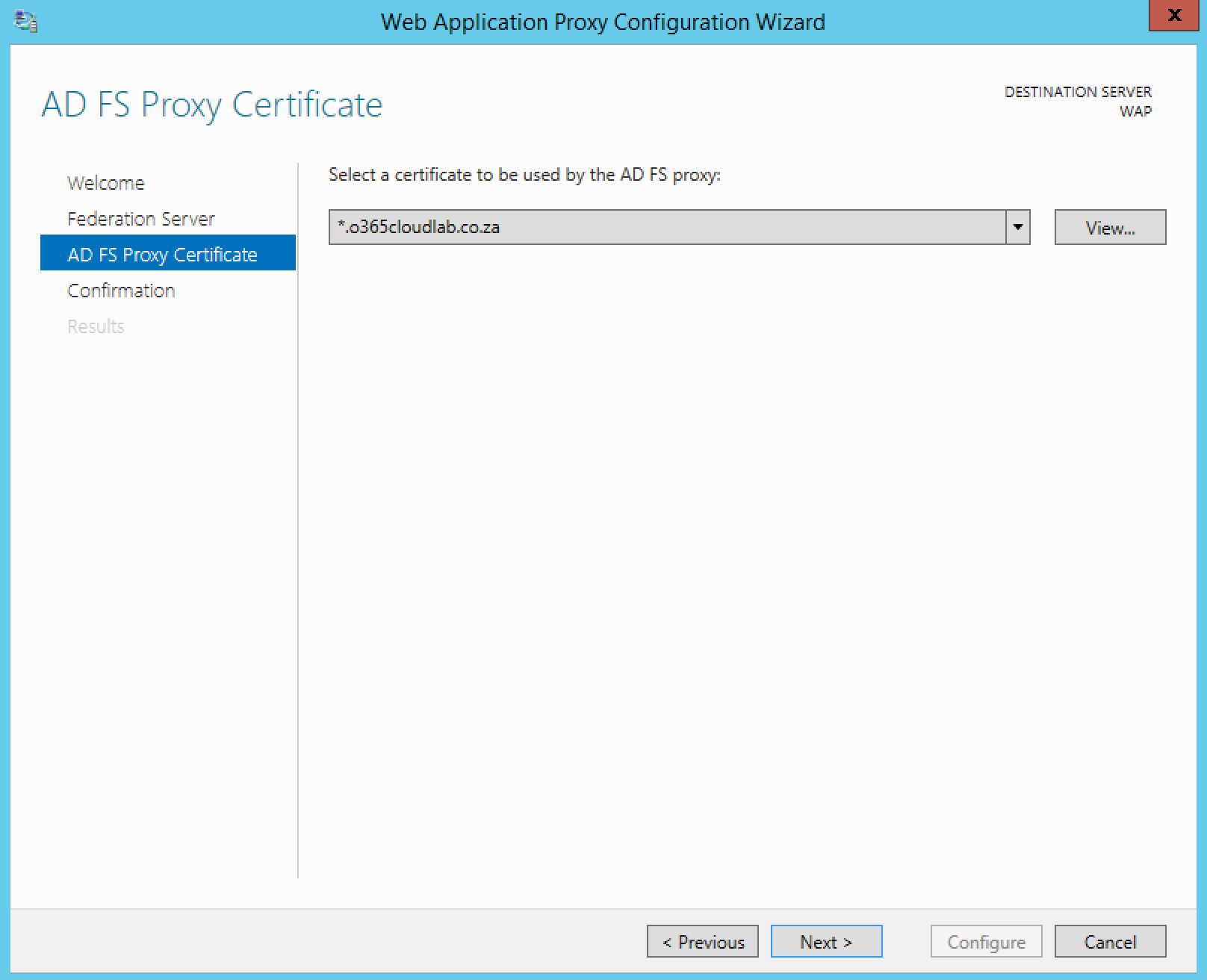
Select the certificate which was installed at the beginning of the deployment and then click next.
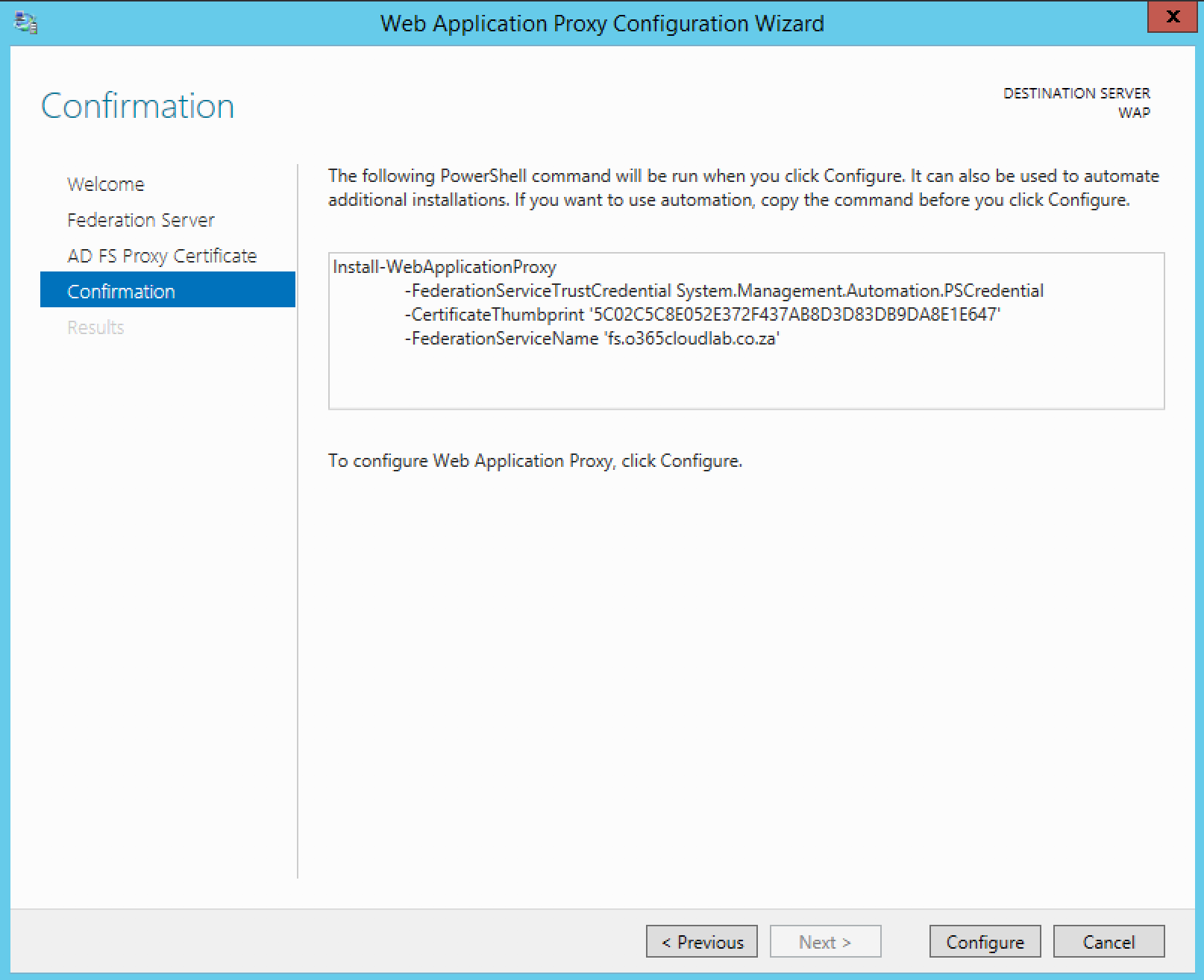
The final screen will show a confirmation screen before the configuration starts. It also shows you a PowerShell version of what will be configured.
The following PowerShell script can be used to configure the same.
Install-WebApplicationProxy -FederationServiceTrustCredential System.Management.Automation.PSCredential -CertificateThumbprint '5C02C5C8E052E372F437AB8D3D83DB9DA8E1E647' -FederationServiceName 'fs.o365cloudlab.co.za'To continue, Click on Configure.
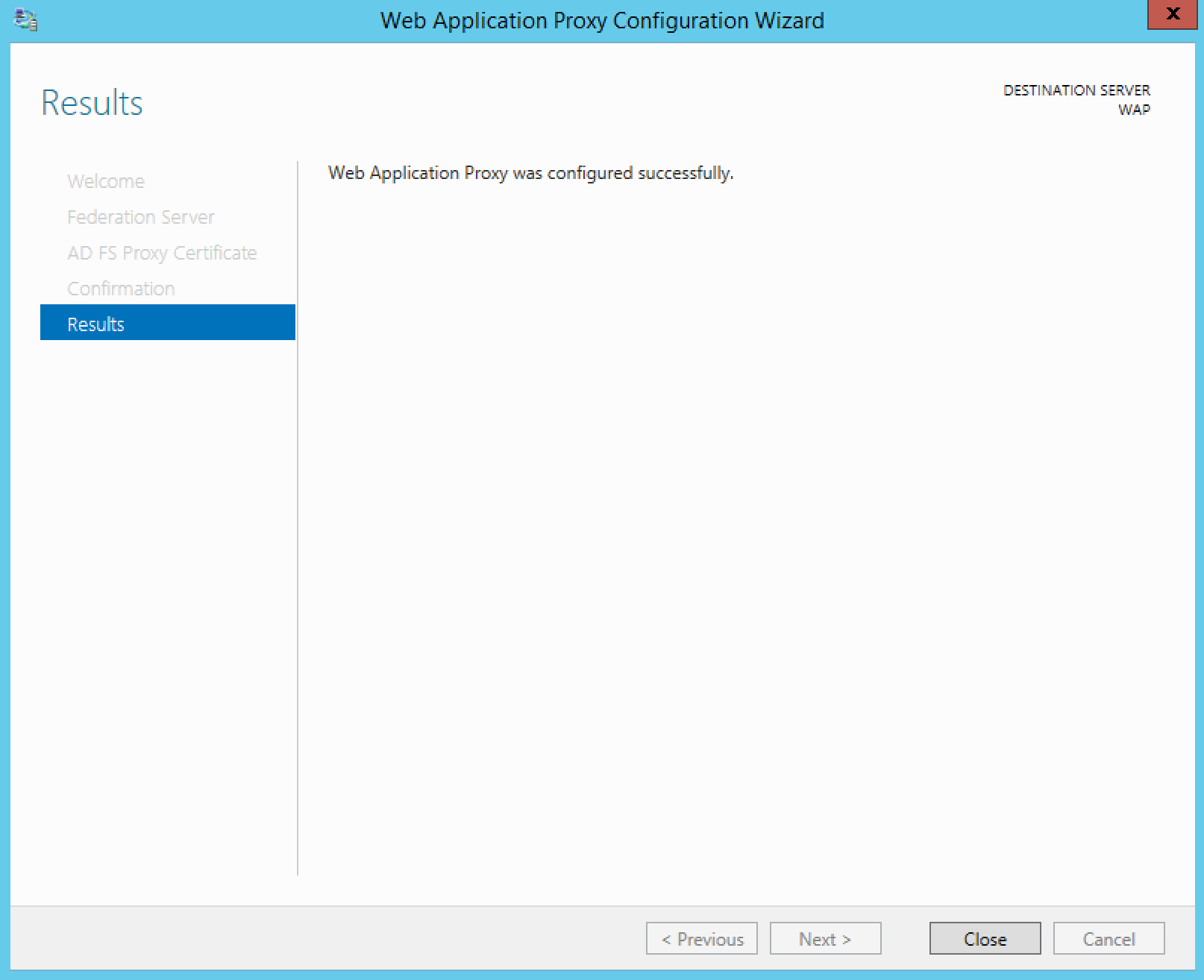
Click on Close, when the configuration is done.
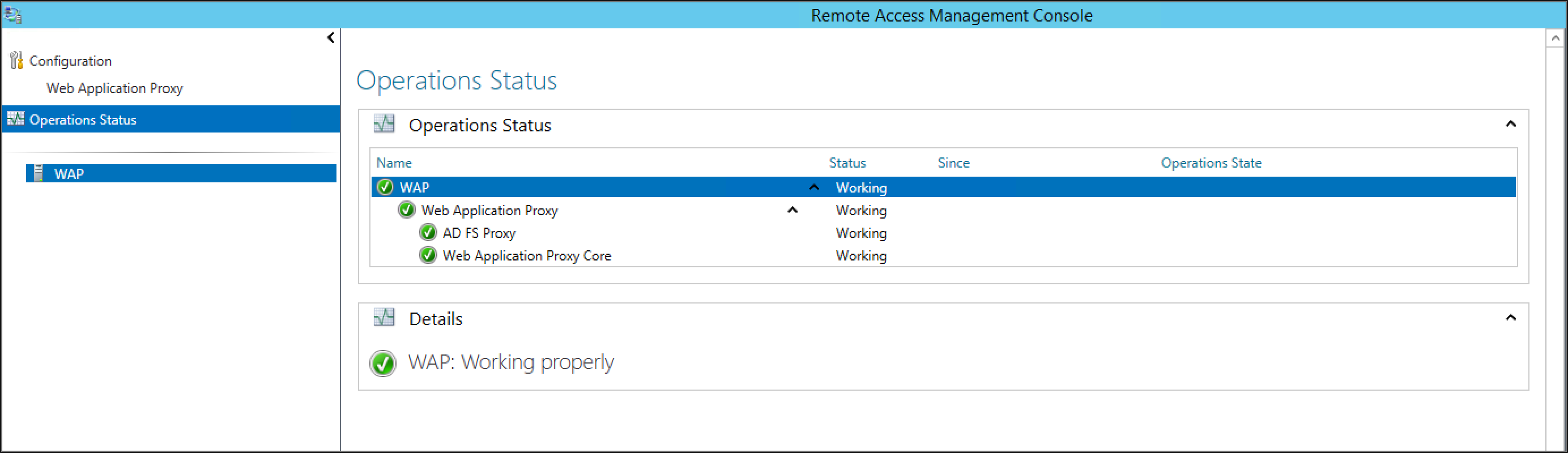
From the Remote Access Management Console, Click on Operation Status and make sure that all is green.
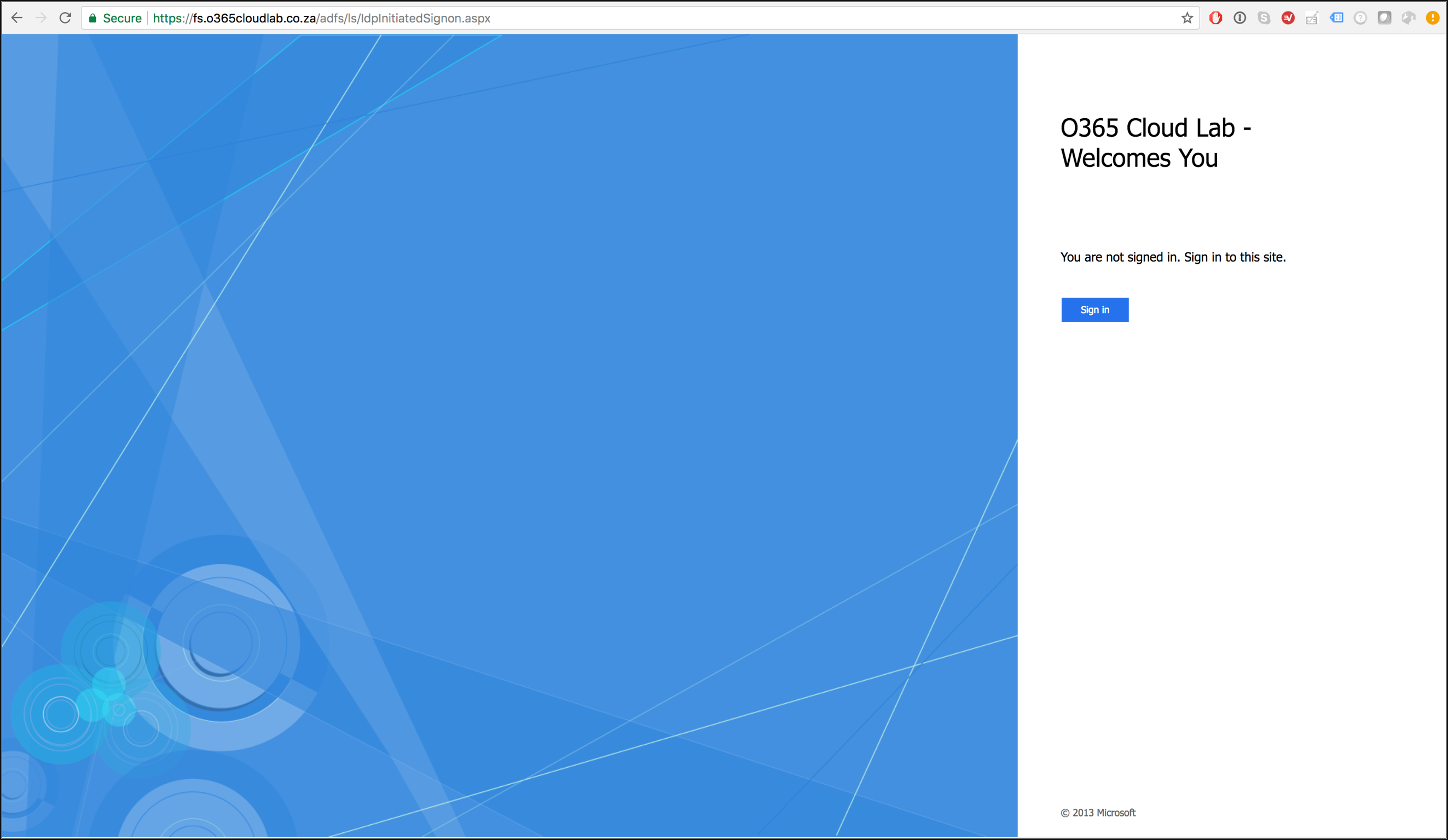
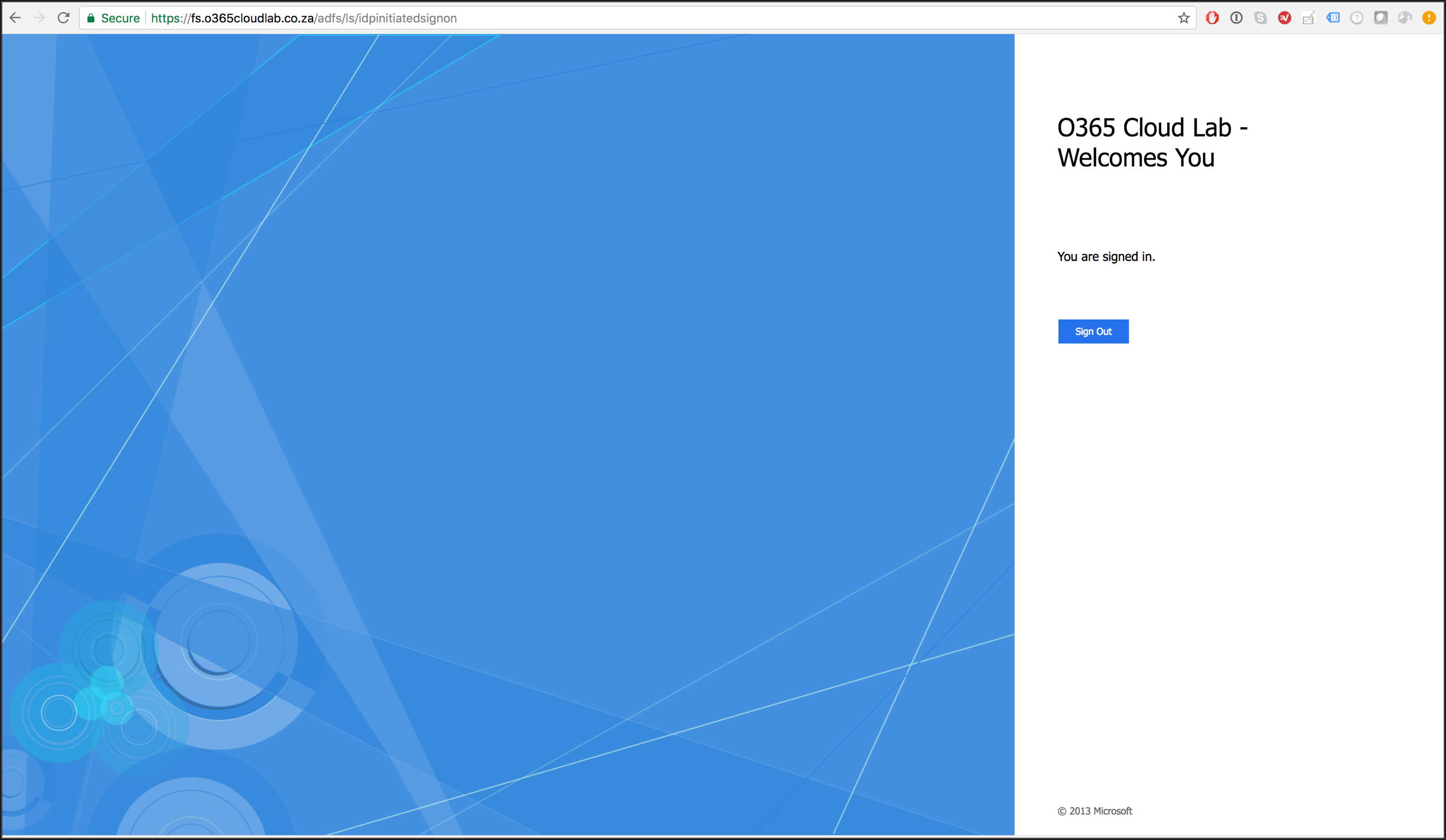
From a Machine that is connected to the internet but not part of the network, verify that you can reach your ADFS server by clicking on the following link.
https://fs.<YourDomainName>/adfs/ls/IdpInitiatedSignon.aspx
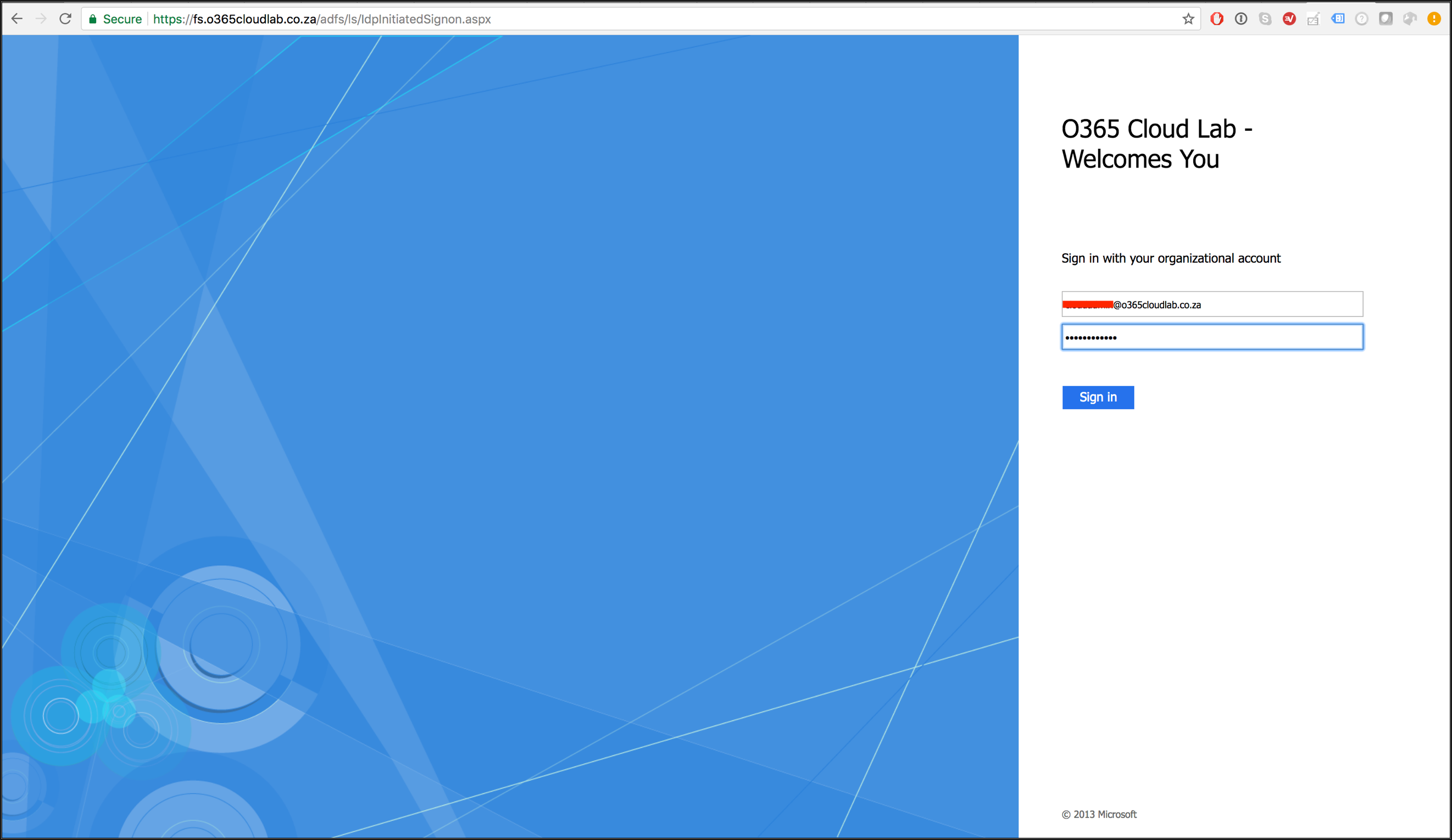
Verify that you can sign in.
On successful logon, you will be redirected to s screen showing the logout icon. This means that you have successfully connected from external.
This concludes the Installation and Configured for the Web Application Proxy.
#ThatLazyAdmin
Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.






Comments (0)