A Beginners guide to VPN Software
IT Professional - Helping others to help themselves. https://andrewleniart.com & https://www.computerhelpzone.com.au/testimonial/
Published:
Browse All Articles > A Beginners guide to VPN Software
In part one of this two-part series, I'm going to explain in layman's terms what a VPN is, what it can and can't do for you, and how it works. In part two (coming soon), I will compare two or more popular VPN services and describe which one I believe is the best to go with.
A Beginners guide to VPN Software by Andrew Leniart
What is a VPN and What does it do?
Update: Part 2 of this two-part series now available here: VPN Comparison for Beginners
A simple explanation of what a Virtual Private Network (VPN) is, goes like this. It's a means of encrypting your data while it travels around the Internet. Using VPN software creates a tunnel of sorts that allows you to surf websites, send an email and provide sensitive information to others in a strongly encrypted fashion. It protects your privacy from others on the Internet.
A VPN also allows you to make yourself appear as if your system is located in a different location or country than where you are. That all causes considerable problems for hackers looking to steal information while using the Internet or trying to hack into your computer.
VPN software is not snake oil. They do work and make it considerably more challenging for hackers to spy on your online activity. So much so that when hackers are choosing potential victims and find a VPN that protects you, they'll usually move on to find someone easier to spy on and hack.
Without a VPN, everything you do on the Internet can be spied on with relative ease. That includes Government Agencies like the Police or FBI, Hackers, and even your Internet Service Provider. If so inclined, they can easily view and log where you go, the websites you visit and things like what you download during any online session.
What a VPN does not do?
Despite the ads you see from most VPN software vendors that promise you the world, a VPN will not:
Protect you from Virus of Malware infections. A VPN is not a replacement for Antivirus and Antimalware software, so don't believe the hype.
Block cookies from collecting your surfing data. Cookies are still saved on your local computer and work as they're designed, regardless of whether you're using a VPN or not.
Make your Internet faster. I laugh whenever I see this claim because a VPN will almost always, without exception, negatively impact your Internet's speed, never increase it.
Hide who you are from your ISP. Any VPN provider that claims they can hide your identity from your Internet Service Provider is quite simply lying. Your ISP will always know that you're using a VPN while connected to their service; they just won't be able to see and track what you're doing while using a VPN.
Always keep your internet usage 100% anonymous online. VPN software can come close, but if your ISP or the Gov't is determined to spy on you, they'll still find ways to do so. Court orders can be obtained for both ISP and VPN providers to log and report everything you do online.
Note for the paranoid: The chances of Gov't Agencies going to the trouble to do this is extremely rare. Unless you're a person of interest like a potential terrorist, a suspected uploader of kiddie porn or similar, you're unlikely to fall under their radar. Just don't be fooled by the many claims that just because you're using a VPN, you can never be identified or spied on. It's simply not true.
Fact is, most people like you and I are simply not interesting enough to be spied on by advanced and time intensive spying tactics that require the co-operation of your ISP and VPN provider (by court order if necessary). Resources are limited, so they're not interested if you just enjoy watching legal porn occasionally or viewing sites with questionable material like software sites distributing illegal software cracks and the like.
How do VPN's Work?
This is a highly technical question that would take a book to adequately explain and not easy for the layman to understand. There are many types of VPN's available that employ a wide variety of encryption protocols and techniques to protect you. But what I can do is give you a palatable answer that most of you should understand.
Firstly, they hide the Internet Protocol (IP) address of your machine. Every computer connected to the Internet has an IP. Think of it as your home address.
Without the benefit of a VPN, a quick check on https://whatismyipaddress.com/ reveals that my;
IPv4 address is: 49.193.xxx.xx
State: Victoria
Country: Australia
Post Code: 3xxx
ISP: Optus
All perfectly accurate info too. That's a great starting point for someone trying to find out where I live.
With the benefit of my VPN activated, I quickly select a VPN server in New Zealand and do the same check on https://whatismyipaddress.com/ - Here's the result;
IPv4 Address is: 180.149.231.116
State: Auckland
Country: New Zealand
Post Code: 1010
ISP: Host Universal Pty Ltd
Given that I haven't moved to NZ in the last ten minutes or so, the new results are now all lies for someone trying to look me up. Have fun hunting down my location now. That's one obvious benefit for me and my privacy. This ability is particularly useful if I'm connecting to a public WIFI hotspot. It makes my laptop and any other mobile devices 'much' safer when protected by a VPN tunnel.
And, the beauty is that with just a couple of clicks, I can effortlessly change countries on the fly anytime I like (effectively giving a new set of false IP information) and even disconnect my VPN completely should I want the full benefit of my Internet speed without going through a VPN server. Pretty neat, right?
So how does a VPN work?
A VPN creates an encrypted tunnel between you and the VPN server you're connecting to, effectively hiding where you're really from and making it appear you're in the country that the VPN server is located in.
Hackers can't get into that tunnel, and even if they do, all they would get would be nonsensical ones and zeros that would mean nothing to them.
Here's a little graphic I found on the Google Images that I manipulated a bit to give you what I hope will be a good visual example:
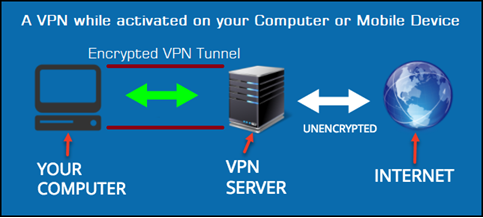
So, everything that goes from your computer to the VPN Server above is encrypted. The two lines above and below the green double arrows are what I refer to as the VPN Tunnel. The VPN server then takes your real information, issues your computer or mobile device with fake details, and then looks to everyone else like you're surfing the Internet from a totally different country, ISP, and IPv4 address.
That's about as basic an explanation of how a VPN works that I could think of to provide. If you still have questions, please post them to the comments section below this article, and I'll try to answer them for you.
Types of VPN software available
There is a ton of different VPN software solutions available to us, the consumers. They all come with their unique offerings and promises, some of those which are valid and highly useful, others which are just aimed at getting you to buy with promises that are often, well, not true.
Conclusion
In Part 2 of this series, I'll be taking a look and comparing some popular VPN software solutions available, share tests that I personally conducted with them and explain why, in my opinion, some are reasonable for the price you pay, others exceptional value for the money, others being just plain rip-offs, and explain why when using totally Free VPN servers, you should only expect to get what you pay for.
Till the next time.
©Andrew Leniart
IT Professional | Freelance Journalist
Personal Blog: https://andrewleniart.com
Please do not forget to press the "Thumbs Up" button if you think this article was helpful and useful. Thank you.

Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.


Comments (5)
Commented:
Author
Commented:Regards, Andrew
Commented:
Author
Commented:Link to Part 2 of this two-part series is now available here:
VPN Comparison for Beginners - https://www.experts-exchange.com/articles/35793/
Thanks, Andrew
Commented: