More on the two "villians" too. It has a nice description, not overly technical (though inevitable at times) for understanding. Crux of it is remediation is really for CPU vendors to issue firmware updates to protect against these attacks. The OS and affected vendor will "support" with their release to reduce the attack surface or make it harder to exploit.
Unfortunately, there are no software patches or operating system mitigations that can fully mitigate the impacts of the Spectre attacks and the flaws being abused. Only saving grace is browser vendors have begun updating their browsers to disable certain features which make the Spectre attack feasible via JavaScript. If really paranoid, back to basic to disable active scripting like Javascript.
https://research.kudelskisecurity.com/2018/01/04/meltdown-spectre-attacks-on-cpu-flaws/
Unfortunately, there are no software patches or operating system mitigations that can fully mitigate the impacts of the Spectre attacks and the flaws being abused. Only saving grace is browser vendors have begun updating their browsers to disable certain features which make the Spectre attack feasible via JavaScript. If really paranoid, back to basic to disable active scripting like Javascript.
https://research.kudelskisecurity.com/2018/01/04/meltdown-spectre-attacks-on-cpu-flaws/
Arstechnica had the best accurate reporting on these faults.
See
https://arstechnica.com/gadgets/2018/01/meltdown-and-spectre-heres-what-intel-apple-microsoft-others-are-doing-about-it/
https://arstechnica.com/gadgets/2018/01/meltdown-and-spectre-every-modern-processor-has-unfixable-security-flaws/
https://arstechnica.com/gadgets/2018/01/whats-behind-the-intel-design-flaw-forcing-numerous-patches/
and also https://spectreattack.com/
But your link is interesting. Intel is doing a microcode update for some processors, and that's the first link I've seen that clearly states that.
See
https://arstechnica.com/gadgets/2018/01/meltdown-and-spectre-heres-what-intel-apple-microsoft-others-are-doing-about-it/
https://arstechnica.com/gadgets/2018/01/meltdown-and-spectre-every-modern-processor-has-unfixable-security-flaws/
https://arstechnica.com/gadgets/2018/01/whats-behind-the-intel-design-flaw-forcing-numerous-patches/
and also https://spectreattack.com/
But your link is interesting. Intel is doing a microcode update for some processors, and that's the first link I've seen that clearly states that.
Author Comment
by:btan
Actually Intel is releasing the patches and also captured in their public statement.
https://arstechnica.com/gadgets/2018/01/intel-faces-class-action-lawsuits-regarding-meltdown-and-spectre/
Regardless here is another side by side comparison for these two villains in case anyone needs it as quick bite.
https://danielmiessler.com/blog/simple-explanation-difference-meltdown-spectre/
https://arstechnica.com/gadgets/2018/01/intel-faces-class-action-lawsuits-regarding-meltdown-and-spectre/
Regardless here is another side by side comparison for these two villains in case anyone needs it as quick bite.
https://danielmiessler.com/blog/simple-explanation-difference-meltdown-spectre/
I think the microcode patches will come through the system vendor, Dell, HP etc etc. Intel will probably supply them with the patches to distribute.
As for the lawsuits that will be interesting. Unless it can be proven that there is a significant slowdown those lawsuits will go nowhere. And at this stage there is no real evidence of that. The most likely candidates will be those who run VM instances in the cloud and we'll need to wait for those to occur.
It will be a pity if the lawsuits don't succeed because I'd love a new Core 2 Quad processor replacement ...
As for the lawsuits that will be interesting. Unless it can be proven that there is a significant slowdown those lawsuits will go nowhere. And at this stage there is no real evidence of that. The most likely candidates will be those who run VM instances in the cloud and we'll need to wait for those to occur.
It will be a pity if the lawsuits don't succeed because I'd love a new Core 2 Quad processor replacement ...
Recommended Posts
Microsoft Activation Offline - Not for you guys in secure locations anymore!
With the removal of local account setup for Windows Installer from Win 11 25H2 those of us who work in locations that do not permit connection of device to the "outside world" for security reasons (or just because we don't like the "outside world") are now also unable to activate Windows offline using telephone activation.
That's also no longer available for Office 2024.
With both you can still generate an activation challenge code from your machine, but it seems Microsoft's activation support team can't process it .
If there's anyone around who has a direct line to Redmond? Can they confirm? Otherwise it looks like this is going to be an issue for the "one or two" (I can't confirm numbers for ... well ... reasons ...) secure locations around the world that need to be air-gapped (and not just those locations that are used for <Redacted>).
With thanks to the respective posters of these questions:
https://www.experts-exchange.com/questions/29295366/No-United-States-Region-during-Windows-11-Activation.html
https://www.experts-exchange.com/questions/29284908/Retail-Office-2O24-Offline-Activation-Issues-with-Win11.html
With the removal of local account setup for Windows Installer from Win 11 25H2 those of us who work in locations that do not permit connection of device to the "outside world" for security reasons (or just because we don't like the "outside world") are now also unable to activate Windows offline using telephone activation.
That's also no longer available for Office 2024.
With both you can still generate an activation challenge code from your machine, but it seems Microsoft's activation support team can't process it .
If there's anyone around who has a direct line to Redmond? Can they confirm? Otherwise it looks like this is going to be an issue for the "one or two" (I can't confirm numbers for ... well ... reasons ...) secure locations around the world that need to be air-gapped (and not just those locations that are used for <Redacted>).
With thanks to the respective posters of these questions:
https://www.experts-exchange.com/questions/29295366/No-United-States-Region-during-Windows-11-Activation.html
https://www.experts-exchange.com/questions/29284908/Retail-Office-2O24-Offline-Activation-Issues-with-Win11.html
<<Otherwise it looks like this is going to be an issue for the "one or two" (I can't confirm numbers for ... well ... reasons ...) secure locations around the world that need to be air-gapped (and not just those locations that are used for <Redacted>).>>
I would think volume licensing would be the only way to go.
Jim.
I would think volume licensing would be the only way to go.
Jim.
UBUNTU 20.04 TERMINAL COMMANDS USEFULL FOR OPEN5GS
Linux ubuntu commands are a type of Unix command or shell procedure. They are the basic tools used to interact with Linux Open5gs platform on an individual test level. These are used to perform a variety of tasks, including displaying information about ip route files and network status of VM‘s.Example of most usefull commands are as follow;
‘sudo ip ro add default via {gateway_ipv4_address} dev {network_interface_name}’
sudo ip ro add 192.168.111 via 127.0.5
‘ip route show’ Command
Sample session:
default via 172.26.0.1 dev ens5 proto dhcp src 172.26.7.237 metric 100
10.147.164.0/24 dev incusbr0 proto kernel scope link src 10.147.164.1
172.26.0.0/20 dev ens5 proto kernel scope link src 172.26.7.237 metric 100
172.26.0.1 dev ens5 proto dhcp scope link src 172.26.7.237 metric 100
172.26.0.2 dev ens5 proto dhcp scope link src 172.26.7.237 metric 100
For External Test Node route Table
‘ip r’ Command
For adding node to list
‘Route –n ‘ Command
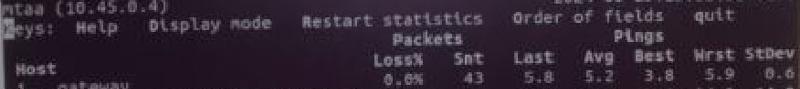
For test Statıstıcs
‘mtr -a 192.168.1.66 8.8.8.8’ Command as follows
Sample Session:
![command output sample]()
Linux ubuntu commands are a type of Unix command or shell procedure. They are the basic tools used to interact with Linux Open5gs platform on an individual test level. These are used to perform a variety of tasks, including displaying information about ip route files and network status of VM‘s.Example of most usefull commands are as follow;
‘sudo ip ro add default via {gateway_ipv4_address} dev {network_interface_name}’
sudo ip ro add 192.168.111 via 127.0.5
‘ip route show’ Command
Sample session:
default via 172.26.0.1 dev ens5 proto dhcp src 172.26.7.237 metric 100
10.147.164.0/24 dev incusbr0 proto kernel scope link src 10.147.164.1
172.26.0.0/20 dev ens5 proto kernel scope link src 172.26.7.237 metric 100
172.26.0.1 dev ens5 proto dhcp scope link src 172.26.7.237 metric 100
172.26.0.2 dev ens5 proto dhcp scope link src 172.26.7.237 metric 100
For External Test Node route Table
‘ip r’ Command
For adding node to list
‘Route –n ‘ Command
For test Statıstıcs
‘mtr -a 192.168.1.66 8.8.8.8’ Command as follows
Sample Session:
Come hang out in the ByteSize group and jump into the conversation. Can’t wait to hear what you all think!
https://www.experts-exchange.com/groups/ByteSize-Weekly-Newsletter.html?cid=2035
https://www.experts-exchange.com/groups/ByteSize-Weekly-Newsletter.html?cid=2035
Actually, ByteSize is weekly. You can view earlier ones here: https://e-e.beehiiv.com/
Keep in touch with Experts Exchange
Tech news and trends delivered to your inbox every month
Experts Exchange
The Original Tech Community
© 1996-2025 Experts Exchange, LLC. All rights reserved. Covered by US Patent.
© 1996-2025 Experts Exchange, LLC. All rights reserved. Covered by US Patent.









